The Ultimate WordPress Security Guide
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

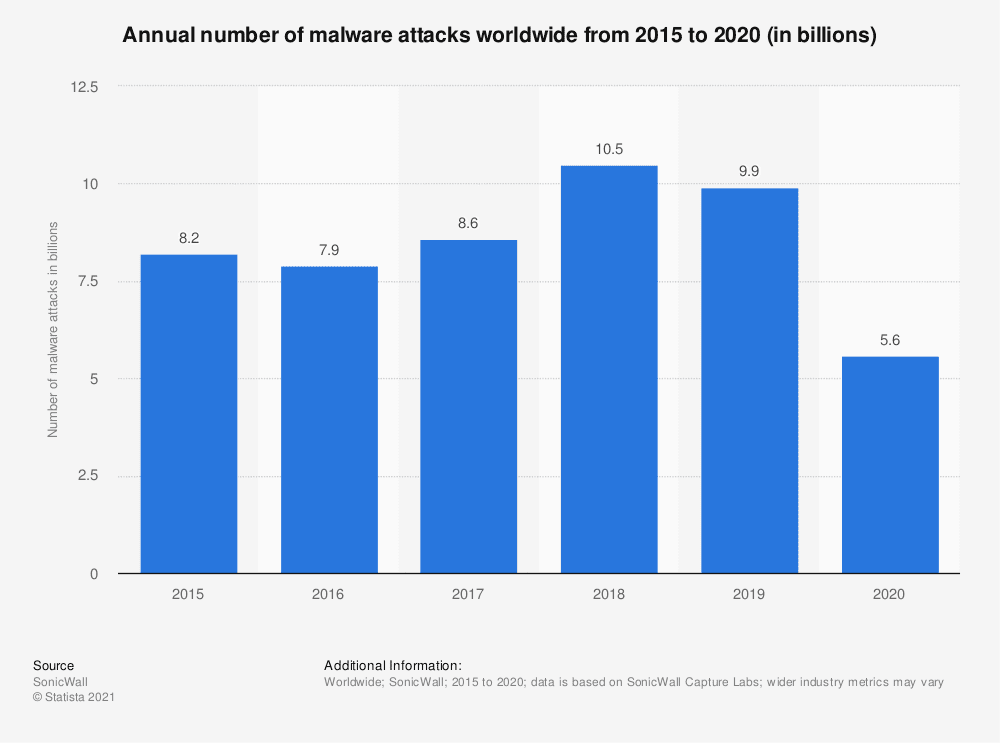
Malware costs businesses billions of dollars every year in lost revenue, legal costs, damage to branding, and data theft. To make matters worse, hackers constantly evolve their tactics, so malware keeps changing and getting harder to spot.
There are data breaches almost every day, and the scary part is how much people are losing to hackers. When WordPress admins try to protect their WordPress websites, they get their advice online. While the advice is well-intentioned, some of it is very poor.
But it is not all bad news. Quite the opposite in fact, because you’ve come to the right place.
The good news is that we, at MalCare, protect over 100,000 WordPress sites every day, so we know plenty about WordPress security. The great news is that we will take you through what you need to know step-by-step to secure WordPress site. The best news is that you don’t need to be a WordPress security expert to protect your website from hackers.
TL;DR Get the best security for WordPress site by installing MalCare. MalCare is a best-in-class WordPress security plugin that deep scans your website daily, cleans hacks in minutes, and protects your website with an advanced firewall. MalCare is built by a team of security experts, and they are instantly reachable for any issues you may encounter.
What is WordPress security?
WordPress security is about protecting your website, data, and visitors—from malware and their damaging consequences. Protecting your website is like building a fence, having a lock on your front door, and installing a security system. You hope that it is never needed, but if it is, you want it to be rock solid.
You may ask yourself if WordPress is secure, and whether it is a good choice to build a website. The short answer is yes, WordPress is secure. In fact, WordPress powers almost 45% of the Internet, and some of the biggest brands use it for their websites.
Most hacks are successful either because of security vulnerabilities or poor password policies. We will show you how you can protect your WordPress website from hacks with a few WordPress security tips. These tips do not require you to know coding or how to edit WordPress files. Your site will still be protected, and you will have successfully conquered WordPress security.
WordPress Security Best Practices (14 Tips)
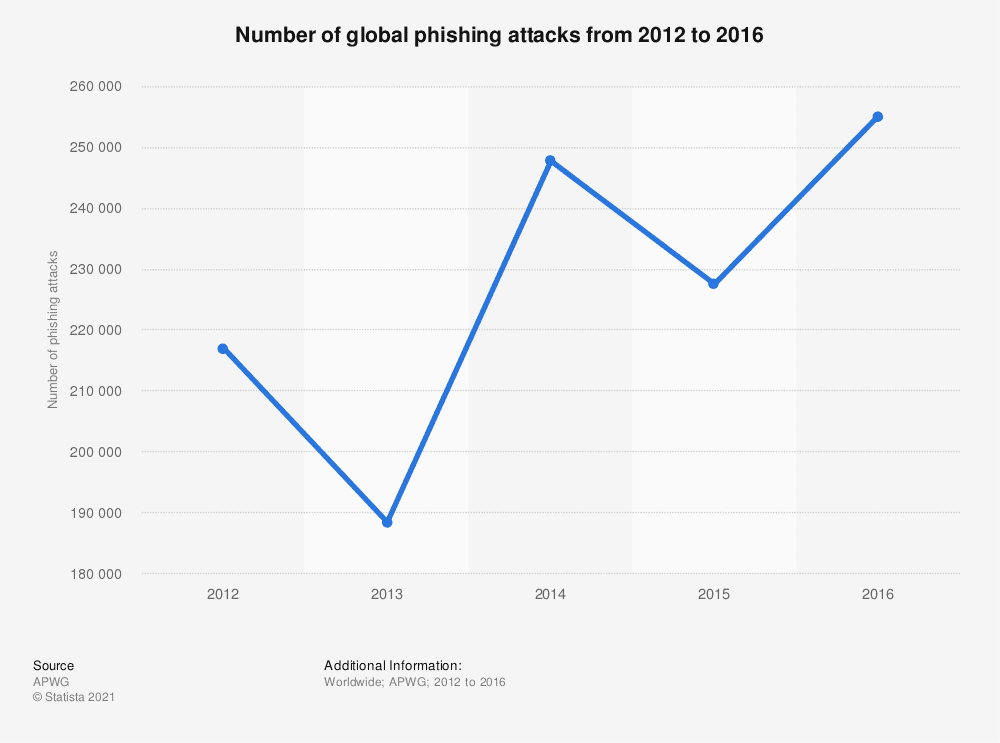
Securing WordPress appears far more difficult than it actually needs to be. It can be daunting to read about different WordPress hacks like spam injections, phishing attacks, or even malicious redirects.
However, there is no need to worry. If you implement the following WordPress security measures, you are sure to have a secure website and protect your data from hackers trying to steal it.
1. Install a WordPress security plugin
The foremost way to protect your WordPress website is to install a best WordPress security plugin, like MalCare.
We recommend MalCare because of the following reasons:
- Daily deep scans WordPress site for malware
- Auto-clean malware with 1-click
- Removes malware and backdoors to prevent reinfection
- Advanced firewall
- Vulnerability detection
- Brute force protection
- Intelligent bot protection
- Activity log
- Doesn’t use server resources of website
MalCare is a complete security plugin that combines the 3 most important aspects of WordPress security: a malware scanner, a malware cleaner, and an advanced firewall.
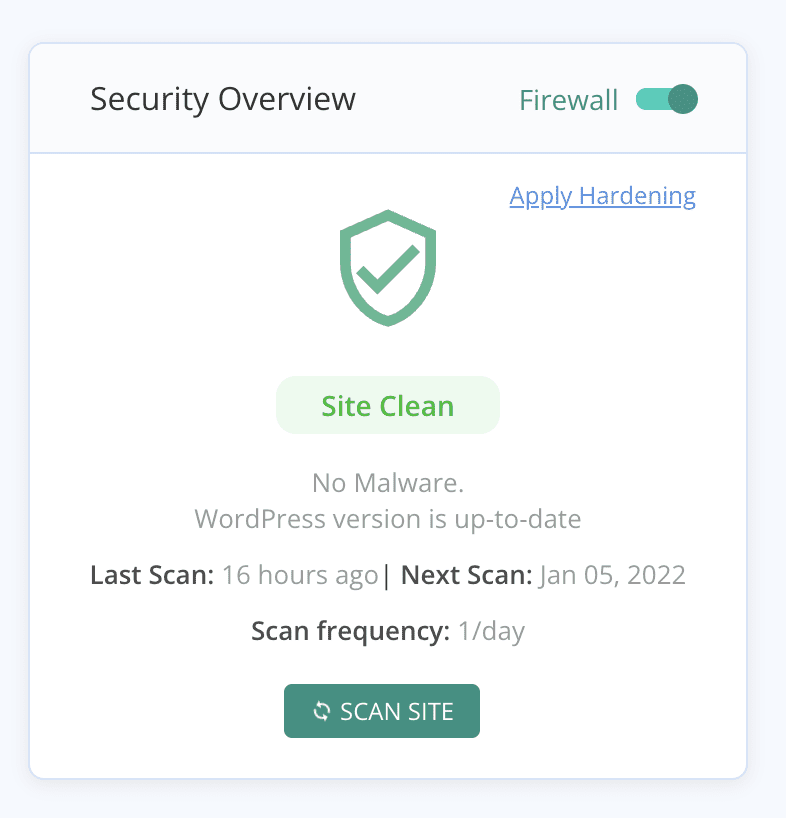
To protect your website with MalCare, all you need to do is install it and let the plugin take over. MalCare syncs your website to our servers, and then sets up a daily deep scan.
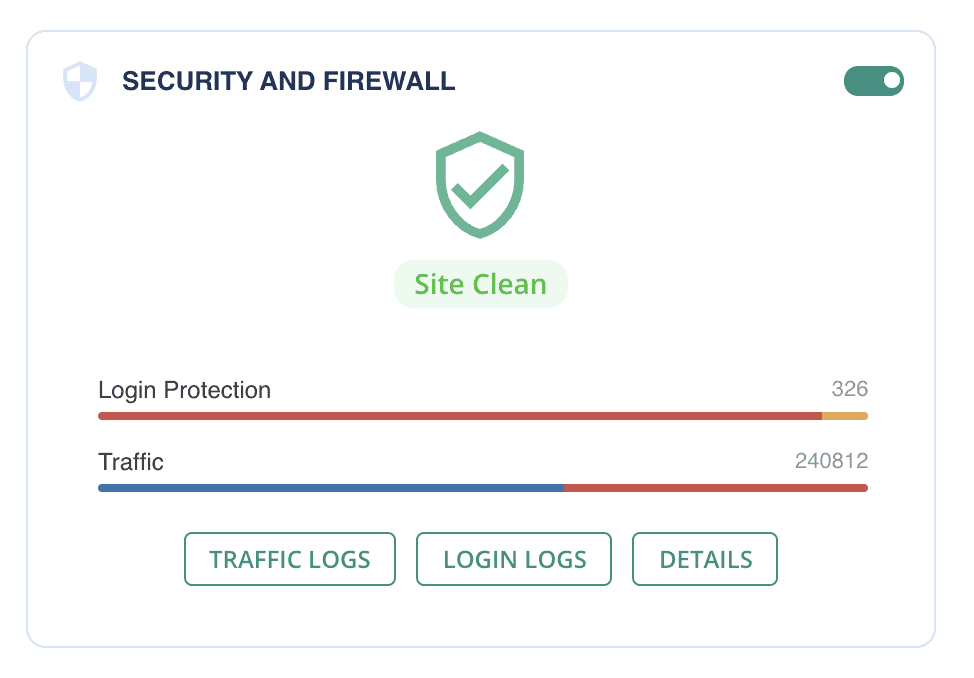
If there is any malware detected on your website, MalCare will alert you, and you can auto-clean the malware with a single click. MalCare removes the malware surgically from your website, while making sure your website remains completely intact. You can also reach out to our team of WordPress security experts who can help you resolve any deeper issues with hacks.
You can use MalCare to protect your WordPress login page from brute force attacks, and limit login attempts. These attacks have been known to overwhelm websites, keeping real users out. Similarly, the plugin comes bundled with bot protection, keeping out bad bots that scrape your website data or bombard your website with so many requests that the site goes down. There are good bots though, like uptime monitoring bots or googlebot used for indexing, so MalCare intelligently keeps out the bad bots while letting the good bots in.
The best part about MalCare is that the performance of your website is unaffected by the scans or cleanup. If you have an e-commerce or membership site, other plugins will have a noticeable impact on the user experience. This is because plugins like Wordfence and Sucuri use your site resources to run their scans. This has led some web hosts to ban Wordfence altogether.
2. Use a web application firewall for your website
A web application firewall, also known as a website firewall, protects your WordPress website by blocking out malicious traffic. A firewall is an essential component of WordPress security because it makes sure that malicious traffic never reaches your website by blocking it.
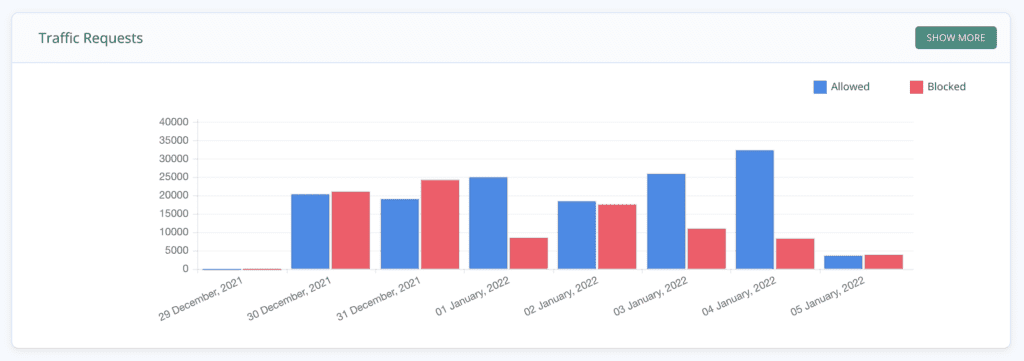
MalCare has an advanced firewall, integrated with the security plugin. When you install the plugin, the firewall comes into effect, protecting your WordPress website from being infected with malware. The benefits of using MalCare’s firewall are:
- Protects your website against SQL injection attacks, remote code execution, spam injection attacks, cross-site scripting attacks, and more
- Prevents hackers from exploiting vulnerabilities on your website
- Global IP protection for 100,000+ websites
- Advanced firewall which learns from each of the protected websites to proactively block bad traffic on others
- Loads with WordPress, so check all incoming traffic for malicious intent
- No configuration necessary; works out of the box
- Bundled with all MalCare’s security plans
There are different types of website firewalls, categorised by where they are installed and how they work. The most effective firewalls load before WordPress, like MalCare and Sucuri, so they can filter out all the bad traffic. Firewalls at the plugin level, like Wordfence, can filter out most of the bad traffic, but not all of it.
3. Deep scan your WordPress site daily
The first pillar of WordPress security is to detect malware as soon as possible. You can do that by scanning your website with a WordPress malware scanner. We recommend installing MalCare, which has a free malware scanner, and a host of benefits:
- Daily automated deep scans
- Identifies even the most well-hidden malware and backdoors
- Advanced scanner that goes beyond signature matching used by most other scanners
- Identifies malware based on 100+ signals for risk assessment
- Scans core WordPress files, website database, and plugin and theme files and folders; both free and premium versions
- 95%+ accuracy with no false positives
- Doesn’t use site resources to run scans
With MalCare, you will have a definitive answer as to whether or not your site is hacked. Once you have the scan results, you can upgrade to clean your website in minutes.
Important: If you discover malware on your website, clean it immediately. Malware gets worse with time, as hackers get time to spread the malware through your website, steal your data, and infect devices and other websites. It is crucial that you remove malware on priority, otherwise you run the risk of Google blacklisting your site, or your web host suspending it.
Malware scanners are not all built the same, and have varying levels of efficacy. Most malware scanners use a signature database to detect malware on websites. They compare the code on the website to all the signatures, and if any match, the code is flagged as malware.
There are several problems with relying solely on a signature database to detect malware.
Firstly, the database needs to be kept up-to-date at all times. Since malware is essentially code, it can have infinite permutations, so a newer variant is likely to pass through matching scanners without being flagged.
Secondly, the team maintaining the database needs to have seen the malware to add it to the database. This is easy with free plugins and themes, but premium software often gets short shrift. We have seen malware go undetected in page builders like Elementor and Divi, or in popular themes from Envato and Themeforest for this very reason.
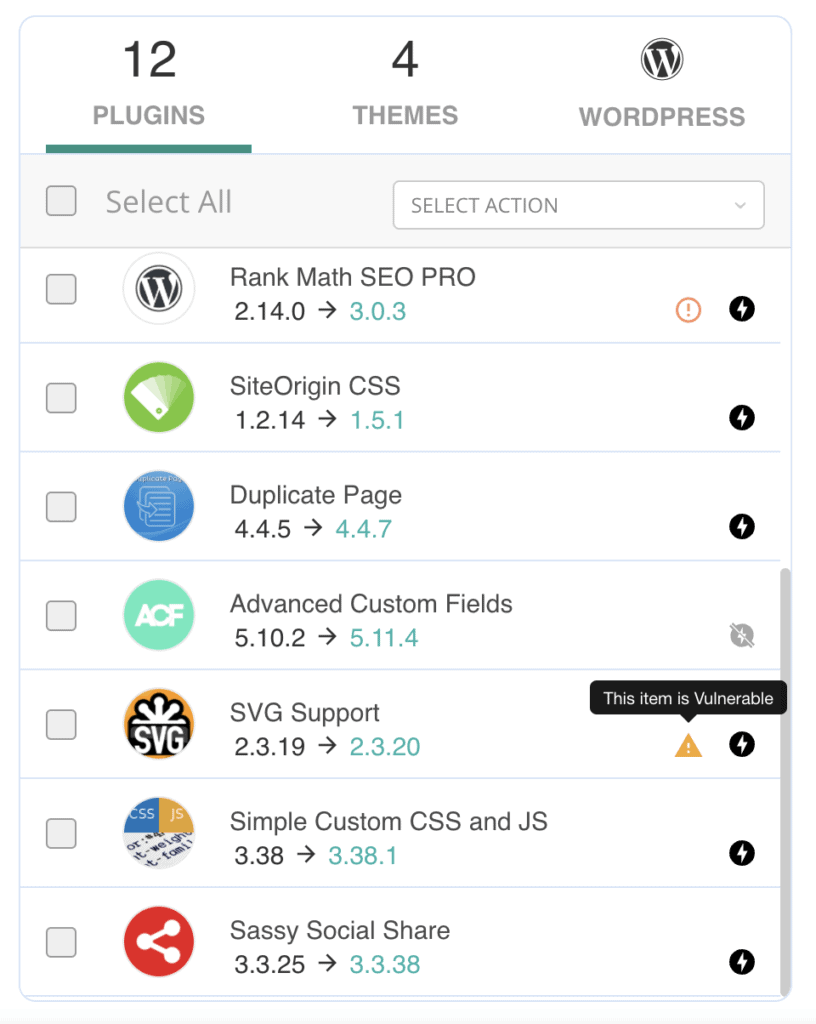
4. Keep everything on your WordPress website updated
The primary reason websites get hacked is because of security vulnerabilities. Vulnerabilities are errors in code that allow unauthorised access to a website, like unsecured file uploads or SQL injections.
WordPress core, plugins and themes are all built with code, and despite best efforts and talented developers, the odd vulnerability may exist. Security researchers often discover these issues, and disclose them to the developers discreetly, so they can resolve the issue. Responsible developers will then release security patches for their products through updates.
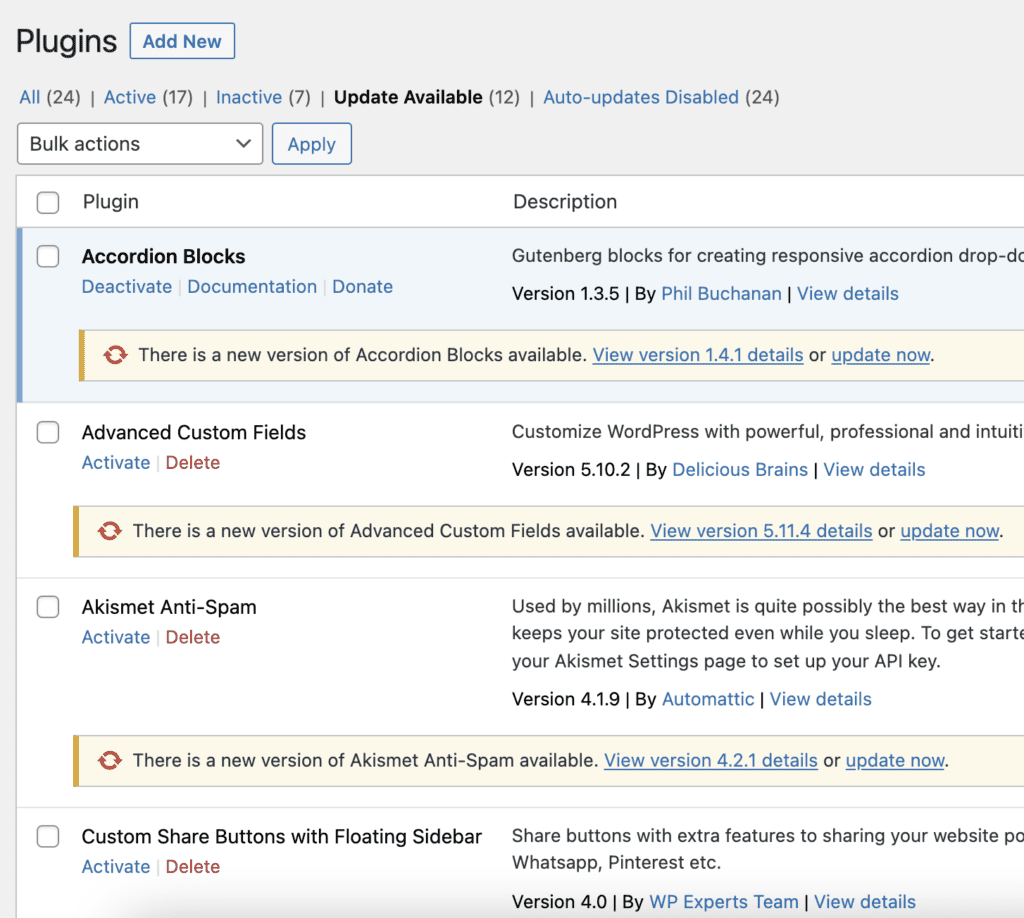
After updates are released, security researchers will disclose the findings publicly to alert users about the vulnerabilities on their websites. Since the vulnerability is now public knowledge, hackers will try attacking sites that haven’t updated yet. Often, they will succeed. Therefore, it is super important to keep everything on your website updated as soon as possible.
Updating your website can be a bit daunting, especially since updates are known to break sites at times. Ideally, you should take backups of your website beforehand, use staging to test the updates first, and only then update on your live website. BlogVault takes care of all these aspects in one place, and you can update your WordPress website safely.
Important: Never use nulled themes and plugins. They are usually chock full of malware, and because they are pirated, they don’t get updates from the developer.
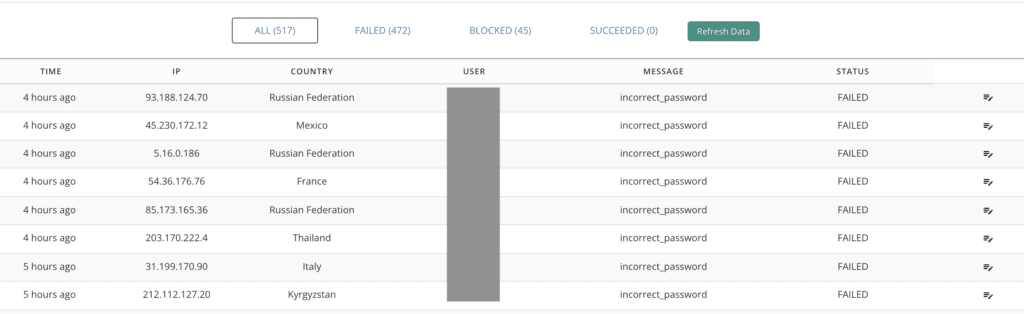
5. Enforce strong password policies
After vulnerabilities, the next biggest reason that WordPress sites get hacked is because of poor passwords. Passwords are often the weakest link in your WordPress security for 2 reasons:
- Easy to remember, therefore easy to guess: We have seen countless websites being hacked because admins have set passwords such as: pass@123, P@ssword, or some combination like that. Hackers use bots that try out common passwords, with different combinations to crack into WordPress sites. Bots can sometimes try as many as several hundreds per minute.
- Data leaked from a breach: Passwords are hard to remember, so people tend to reuse them across different websites and products. However, if one of those websites is hacked and there is a data breach, your login credentials are compromised. Hackers have both tokens—your email address and password—needed to crack into your website.
You can use a plugin to enforce strong passwords for all your users. Users will be required to set strong passwords which have not been compromised in a data breach. Understandably, strong passwords are also difficult to remember, so we recommend the use of password managers. The slight inconvenience is definitely worth the security it brings to your website.
6. Enable two-factor authentication
If you applied the steps in the previous section, then you have a strong password. But that doesn’t change the fact that there is only a password between your website and a hacker.
Two-factor authentication is an extra layer of security for your website’s login. Usually, you need a username and password to log into your website, and the username is often your email address. Which means, if an attacker knows your email address, they only have to guess one authentication factor—your password—to gain access.
Adding another authentication factor amplifies WordPress security considerably, and it is very simple to do. You can install a plugin to do it, without having to fiddle about with code.
Here are a few free plugins that will enable two-factor authentication on your website:
Wordfence’s free version also has the feature, as does iThemes Security. We don’t recommend using iThemes for anything other than two-factor authentication though, for many reasons.
7. Use SSL
SSL is a security protocol used by websites to encrypt communication. When someone visits your website, data is sent from their browser to your website server, and then back again. This is how communication occurs over the Internet, and much information is transmitted this way.
It is very easy to install an SSL certificate. Over and above that, SSL is a worthwhile investment of time for a few reasons:
- Encrypts data that is sent to and from the website server, which protects the data from being readable to unauthorised people
- SSL-enabled websites have a green lock next to their URL in most browsers which is a badge of trust for visitors
- Google actively promotes SSL and will display ‘Site not secure’ message in search results if the website doesn’t have SSL
The way SSL works is to encrypt communication, so even if an unauthorised person eavesdrops, they will not be able to understand what is being transmitted.
It is helpful to think about it like a phone conversation. Ideally, the phone conversation is private to the two people on either end of the call. However, if a third person is able to tap into that phone line, the information exchanged is compromised.
Similarly, communication to and from your website can be compromised. In your website’s case though, the data exchanged can be sensitive, like identity information or passwords, which is why encryption is necessary.
It is straightforward to set up with Really Simple SSL, and is often also offered by web hosts as a part of their services.
8. Backup your website daily
Malware has been known to wipe websites out, or cause web hosts to delete websites along with their backups. Sometimes malware can get so bad that people are forced to start their websites from scratch. However, if you backed up your website, you still have a fighting chance to salvage your website.
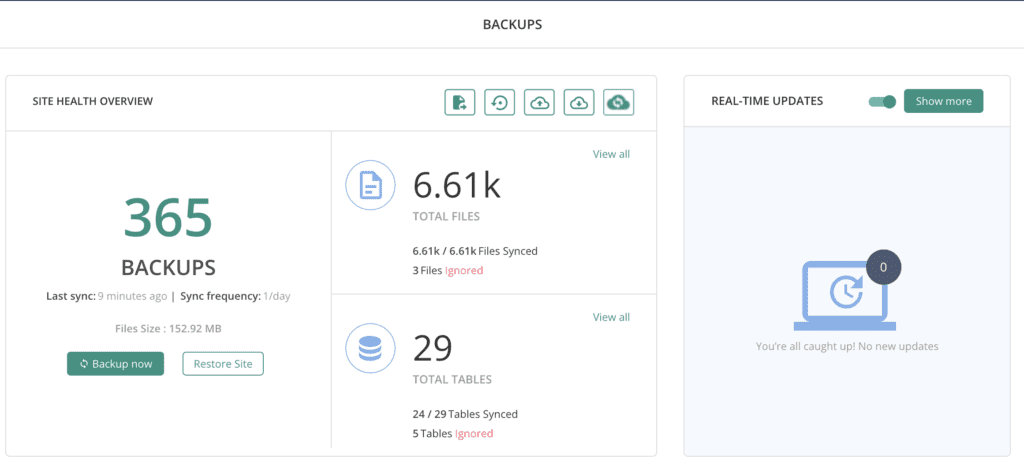
The best WordPress website backups are automatic, regular, encrypted for security, with reliable restores and completely independent of your web host. Many backup plugins store backups on the same server as your website, so run the risk of being affected by whatever befalls your live site. Web hosts backups only work in best-case scenarios, because a web host can be very trigger-happy about deleting sites that are infected with malware.
9. Choose a good web host
It is a common misconception that web hosts are responsible for malware infections, because people mistakenly assume that the web host isn’t securing their servers. On the contrary, the web host has a lot to lose if malware is discovered on their servers, and therefore their security is usually watertight.
We say ‘usually’ because web hosts occasionally face data breaches too. In November 2021, GoDaddy had a breach that exposed the SFTP and database credentials of 1.2 million users. Since GoDaddy is one of the biggest web hosts, the number was correspondingly huge.
However this is an exception and not the rule. Generally speaking, good web hosts have network firewalls, and a ton of other security infrastructure to protect their servers from malware.
If you are on the lookout for a good web host, these are the things you should look for:
- Up to date infrastructure
- Published security policies and certifications
- Clear terms and conditions, about how they deal with malware for instance
- Prompt support
Choosing a good web hosting provider is akin to building a strong foundation for your website. Once you’ve got it, you can forget about it.
10. Harden WordPress Security
WordPress hardening is an umbrella term for measures you can take to make your WordPress security stronger. Strictly speaking, setting strong passwords and using two-factor authentication is technically WordPress hardening as well, but those have an immense impact on security, whereas these points are good-to-haves.
There are a few ways to implement the following measures on your website. If you are comfortable with coding, then you can do them manually. We have linked to articles that tell you the exact steps to take. Alternatively, you can use MalCare to apply these measures for you, or protect your WordPress website against vulnerabilities being exploited.
- Blocking PHP execution in the /wp-uploads folder: A hacker can upload a PHP file to your website, execute it and take control of your website. This type of hack is known as a remote code execution attack. The /wp-uploads folder doesn’t need to have executable code ever, so blocking PHP execution prevents this type of attack altogether.
- Limit login attempts: Hackers use bots to perform brute force attacks on the login page, trying out many different passwords. You can limit the number of incorrect attempts a user can have at a time, by temporarily locking out the user, or implementing a captcha. This measure reduces the total number of attempts a bot has to guess the correct password, and protects the site from being brute-forced.
- Disable XML-RPC: The XML-RPC function is an old one used by WordPress to communicate with other systems. It has mostly been replaced by REST API in recent years, but it is still included in later versions for backwards compatibility. It can be used to log into the website though, and that’s why it is considered a vulnerability.
There are a lot of articles about hardening WordPress in order to protect it from hackers. Some of these measures work well; others have minimal security impact while hampering the usability of your website. The tradeoff usually is not worth it. We’ll cover some of the measures that fall into this category in a later section.
11. Remove any unused plugins or themes
Once in a while, review the list of installed plugins and themes. If they are not in active use, these tend to get overlooked for updates. Then, if vulnerabilities are found, they become a weak link in your WordPress security.
It is best practice to remove any unused themes and plugins from your WordPress site. At the very least, remove those that are deactivated.
12. Implement user management policies
Hackers are out to get access to your website, and the quickest, most efficient way to do that is to gain control of an administrator account. They can also get into a user account and upgrade the account to give them admin privileges using malware, although this is harder to do. Either way, user accounts can be a gateway to your website.
For this reason, there are steps you should take to ensure none of the user accounts are currently compromised, and prevent them from being compromised in the future:
- Install an activity log: Unexpected changes to users, files, posts, settings, plugins, themes, or any other part of the website can be an early signal of a compromised user account. In fact, many hackers take advantage of insufficient logging to hide their activities.

- Review users regularly: The management of a website can change over time, like writers and editors coming and going. Keep an eye on the users, and remove any that no longer need access to the website. Dormant user accounts have the same password as before. If they reused their password elsewhere and it was part of a breach, your site is now vulnerable as a result.
- Implement least privileges policy: Make sure to give each user only as much access as they require to your website. A writer doesn’t need admin access, nor does an editor. Limit the number of admin users altogether.
You can manage users easily from within wp-admin. MalCare includes an activity log as a part of its security plans.
13. Use SFTP/SSH
If you are unfamiliar with code or managing the files and folders of WordPress, it is unlikely you will need to change to SFTP or use SSH. However, if you use FTP at all, consider switching to SFTP instead.
It works in exactly the same way as FTP, except that the data transmitted is encrypted and is transferred using SSH. That means that the data cannot be read while in transit, much like how SSL works for securing data transmission over HTTP.
14. Manage multiple WordPress installations
There are many reasons why there could be more than one WordPress installation in the same website folder. Perhaps it is a staging site, a sub-domain, or even an old design that was eventually replaced by a new one. Regardless of the reason, a nested WordPress installation is one of the main causes of malware reinfection.
Older WordPress installations tend to have vulnerabilities that are overlooked, because they are not on the primary site. Because of this, they are prone to being easily hacked. As malware spreads easily between WordPress files and folders, this leads to the primary website getting infected.
Even if the admin cleans the malware from the primary site, unless they do the same for the nested installations as well, the malware will just reappear. The wp-vcd malware is a great example of a pernicious malware that absolutely refuses to budge.
Common misconceptions about WordPress security
There is a lot of bad information available about WordPress security. It is all well-intentioned, but bad nevertheless. As security experts, we want to debunk some of the most egregious notions we’ve seen floating around the Internet.
WordPress is not secure
On the contrary, WordPress is well-developed as a secure CMS. It didn’t start out as the most secure, obviously, but over time, the security kinks have been straightened out. Releases and patches have been addressed, and it is now one of the best options available.
The reason that WordPress sees more than its fair share of hackers and malware is because of its immense popularity. More websites are powered by WordPress, so it makes sense for hackers to find security loopholes in it, because the payoff is bigger.
In fact, because of this constant threat of hacks, WordPress has eliminated many of the security issues that still exist in other CMS.
Your web host is responsible for malware on your website
At least, 95% of the time they aren’t. Websites are chiefly hacked because of vulnerabilities or compromised passwords. Both those things are squarely in control—and therefore the responsibility—of the site owner and admin.
Web hosts have a lot to lose if there is malware discovered on their servers. That is why they can be quite trigger happy about suspending sites that have malware on them.
Multiple WordPress security plugins will protect your website better
We can see the logic behind this misconception: if one security plugin is good at one aspect, and another is good at another, by using both I will cover all my bases. Well, no.
We did a series where we tested all the major security plugins pretty thoroughly. iThemes Security, Jetpack and Sucuri all failed to detect malware on our hacked websites. And that’s just one example of failure.
One security plugin—we obviously recommend MalCare—should be able to scan, clean and protect competently for it to deserve the title of security plugin. Wordfence comes a close second, but it will drain your server resources in the bargain.
All WordPress hardening advice is good
Don’t do any of the following things, because they cause more problems than they solve or they are ineffective as security measures:
- Hiding the WordPress version number
- Changing login url
- Changing database prefix
Additionally, avoid the following. You should not have to configure your security settings so minutely, because it can become problematic if you are managing more than one website.
- Geoblocking: Geoblocking involves blacklisting a range of IPs that correspond to the geographic location you want to keep off your website. It could be a city, a country, or a region. However, IPs are not always 100% accurate, so you may end up keeping out visitors you want. Over and above that, if you block out some countries, search bots that operate from those countries will not be able to index your website.
- Protecting individual core files: A good firewall should take care of this, and a reliable scanner will find malware quickly in WordPress core files.
My website is too small to be hacked
Websites have value whether it is obvious or not. All websites have assets that can be used for a multitude of purposes. Website owners tend to believe that smaller sites fly under the radar of hackers. This is not true. While bigger sites have more value that doesn’t negate the value of a small site altogether.
For instance, a small site may not be a store, and therefore not have financial details. But it can be used as a part of a botnet. Or it may have a small dedicated following, which can be tapped for phishing scams via their email addresses.
Because people tend to use the same passwords for different accounts, it is theoretically possible to now hack into another site or system using this information. Your website played a small but crucial role in this chain of events.
Why is WordPress security important?
A hacked WordPress website is a nightmare for everyone concerned. Businesses lose revenue and brand reputation. Hackers can steal your website visitors’ data, identity, and passwords. Malware can spread from your website to other websites and devices. You will see your SEO rankings plummet, Google may blacklist your website, your web host may suspend your account. All because of hackers and their malware.
The impact of a hacked website can be wide-ranging in bad consequences. And those consequences are not confined to individual websites or their owners and administrators, but have far reaching implications.
Takeaways
WordPress security is important because it protects your WordPress website, your business, your visitors, your web host, and yourself from the damage that malware can wreak on everyone. In a nutshell, WordPress security means protecting your corner of the Internet from bad actors. The best way to do that is to install a security plugin like MalCare.
FAQs
What are the best WordPress security measures?
The best WordPress security measures are:
- Install a security plugin that can scan and clean malware
- Install a firewall to block out bad traffic
- Scan your website daily for malware
- Keep your WordPress, plugins and themes updated
- Implement two-factor authentication
- Make sure you use strong passwords
- Install an SSL certificate
What are the must-have security requirements?
The most important security requirement for a WordPress website is a good security plugin that can scan and clean malware. It should also be able to protect the WordPress site from hackers with a firewall.
How do I secure my WordPress site?
The best way to secure your WordPress site is to install a WordPress security plugin. MalCare is a best-in-class security plugin that can detect malware in your website files and in the database, and clean it in minutes. Additionally, a good security plugin will come with a firewall that prevents malicious traffic from exploiting vulnerabilities on the website.
Why is WordPress security important?
WordPress security is important to protect your WordPress site from hackers that want to steal your data, and that of your visitors. Malware causes billions of dollars of lost revenue every year. WordPress admin should take steps to protect their website, their data and their visitors from the damage that malware can cause.
How secure is WordPress?
WordPress is very secure, however no software is 100% hack-proof. That includes WordPress, and its plugins and themes. However, it is possible to protect against hacks by installing a security plugin, and secure WordPress better.
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








