WordPress Hardening: 18 Ways to Harden Security of Your Website
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.
There are systems that are hard to hack into, but more often than not, websites get hacked because they are vulnerable, and they don’t have basic security in place.
In this article, we are going to talk about how to harden your WordPress site.
TL;DR: Secure your website with MalCare, an all-in-one security suite for WordPress. With MalCare, you can also harden WordPress security in 1-click.
Before you begin
We’ve organised the list by ease of implementation, so you can start at the top and work your way down the list. We recommend that you start by installing MalCare, and using the Site Hardening option there. That’s a huge step in the right direction, and then you can come back here for more measures.
Pro tip: We always recommend you backup your website before making any changes, even security ones. Better safe than sorry!
5 EASY ways to harden your WordPress security
Let’s start this list with some low-hanging fruit. Get these basic settings out of the way, and we’ll all feel good about making progress with hardening WordPress.
Set strong passwords
Passwords are perhaps the lowest hanging of all low-hanging fruit. That’s probably why they’re just as often ignored. And that’s why they’re at the top of a how to harden your WordPress site list.
Passwords are hard to remember, and yes some of the best practices are tiresome: no duplicate passwords; not easy passwords; a mix of letters, numbers and symbols; the list is truly daunting, especially when you stop to count how many services you use.
We sympathise, and so we suggest using a password manager, like LastPass. Use an automatically-generated string of numbers, letters and symbols to keep your account safe. Even though the odds are small, brute force attacks now use dictionary attacks to guess at passwords.
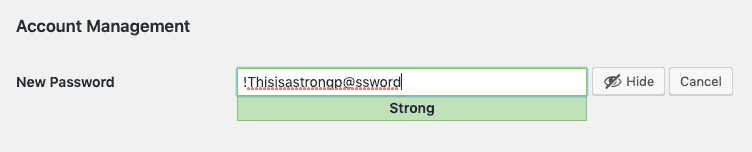
Require the use of strong passwords
Continuing with our theme of strong passwords, this needs to be the next item on your to-do list.
When you have multiple users handling your website, you need to ensure every user maintains a strong password and also changes it regularly. Now, this may be easier on a small scale, but when it comes to a bigger team, it would be better to have a software that will automate this for you.
WordPress by default will alert you if you choose a weak password:
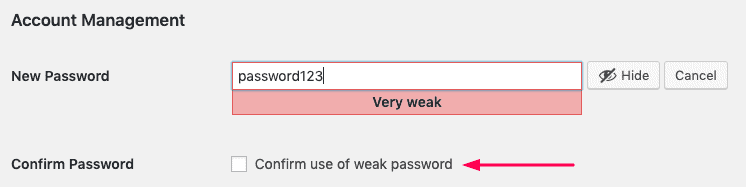
However, you can choose to override it by checking ‘confirm use of weak password’. By doing so, you are leaving your website vulnerable to attacks.
To force the users to update their passwords, there used to be plugins like Expire passwords. It would allow you to set a maximum number of days before the password expires. However, most of these plugins have not been updated for a long time, so we wouldn’t recommend using them.
Implement least privilege permissions
There are 6 pre-defined roles you can have on a WordPress website: Super Admin, Administrator, Editor, Author, Contributor and Subscriber. Each role has a set of permissions, and can therefore perform some tasks. These tasks are called capabilities. The full list of roles and capabilities is here.
Note: For a single website the administrator role is the most powerful, whereas for a multisite it is the super admin role.
If you have a single website, you only need a limited number of administrators. In fact, the rule of thumb here is to have as few administrators as you can possibly manage with. The reasoning is straightforward: you are reducing the risk of hackers stealing admin credentials.
Install SSL
SSL is a way to transmit data securely from user to server, and back again, over an encrypted connection.
Quite apart from the fact that it is a good security practice, Google requires that websites have SSL. It tends to penalise websites by showing “Not secure” in the browser, instead of the pleasant green lock that indicates a website runs on HTTPS instead of HTTP.
It used to be quite complicated to install an SSL certificate, but not any more. We have a complete guide to installing SSL, and another to make sure that all your pages are HTTPS as well.
Set up a WordPress security plugin
All the other entries in our list up to this point are manual additions you make to your website. Rest assured, they are the easy ones that don’t require too much configuration, or installation of plugins.
The rest of this list isn’t quite as straightforward. Many of the measures are included in MalCare’s Site Hardening feature.
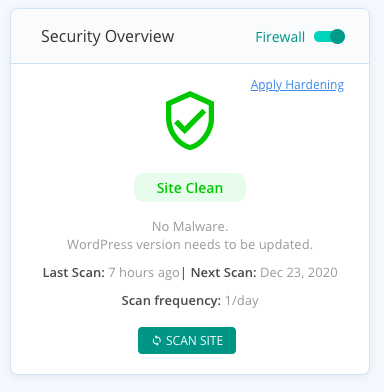
You will save a considerable amount of time by installing the plugin and using our dashboard to set up the measures.
6 MEDIUM measures to harden WordPress
Each of the WordPress hardening measures we have included in this section involve the installation of a plugin. We do not recommend installing plugins lightly, as they often contain vulnerabilities, and become the entry points to infection. Please use discretion when choosing a plugin to carry out the following security measures.
2-factor authentication
One of the most common ways hackers break into websites is through the login page. They use a technique called brute force attacks wherein they use bots to guess the login credentials of a website. Another way hackers can get in is if your data was leaked from another website. Hackers are aware that many people use the same username and password for multiple accounts across the internet, and hence, it becomes easier to play the guessing game!
To protect yourself, you can add a two-factor verification for every user – whether they are Super Admin, Administrator, Editor, Author, Contributor, or a Subscriber.
Many websites, Gmail for example, give users the option of 2-step verification to log in to their accounts. This requires a user to provide their login details first, and then enter a password that is generated in real-time (usually a one-time password sent to the registered phone number). It makes your account harder for hackers to crack, or for them to gain access to your WordPress dashboard.
Limit login attempts
There’s a reason why websites, especially banks, give users only three attempts to get their username and password right. After that, you’re given the option of ‘Forgot password’ or even get locked out of your accounts. The image below is an example of a warning that is generated and displayed on the login screen when the user has attempted to login with wrong credentials.
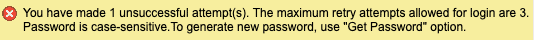
This is essentially to eliminate brute force attacks and reduce the success of hackers and fraudsters.
By default, WordPress allows an unlimited number of login attempts. Enabling limited login attempts on your website increases its security and ensures hackers can’t try thousands of combinations to get in. There are three ways in which you can limit login attempts on your website.
- You can install a plugin like Limit Login Attempts Reloaded.
- If you already have the MalCare security plugin active on your website, you automatically have limited login protection against failed attempts. The plugin implements captcha-based protection that will prevent bad bots from accessing your site.
- By manually inserting code in the functions.php file. You need to add a WordPress action and hook filter with a corresponding callback function. This method is technical and risky. If you aren’t savvy with coding, it’s best not to attempt this.
You’ll find the code for the third option and a more detailed explanation in our article about limiting login attempts.
Keep an audit log
This may not be a WordPress hardening measure per se, but it is an absolute must-have security measure.
Simply install a plugin like WP Security Audit Log which will track everything that happens on your website. And in this way, you will know exactly what your users are doing and when. You can then monitor what’s happening on your website and hold users accountable for their actions.
The plugin will keep track of everything – logins, logouts, changes made, creations, modifications, deletions, additions, updates, etc. If you are hacked, you can refer to the activity log to identify any suspicious activity or changes made.
You can get instant notifications if there have been any critical changes made to your website. You can also log off or block any user with just a click.
Auto logout inactive users
This feature is seen primarily with bank websites and apps that log you out after a period of inactivity. This is to protect your account from any unauthorized access.
To set this up, you can use a plugin that has an idle session logout feature.
Set up alerts for suspicious WordPress logins
Hackers are constantly finding ways to bypass security features, and thus it behoves us to be vigilant. It’s advisable to set up alerts on your website to be notified of any suspicious activity as and when it happens.
To do this you need to use a security plugin like MalCare. It constantly scans your site and alerts you if it detects any malware or anything suspicious.
Set up a web application firewall
A web application firewall will block hackers even before they visit your website. They do this by tracking IP addresses – a numerical identifier assigned to every device that’s connected to the internet.
If the IP has carried out malicious activities before, they’ll be marked and blocked from coming to your site.
Set up a firewall using a security plugin, and rest assured you have the best protection possible for your website.
7 COMPLEX WordPress hardening methods
Now we come to the real scrappy stuff to harden WordPress. The following measures need some coding or development experience, otherwise mistakes can cause site crashes and breakdowns.
Proceed with these hardening methods with some caution, and if you haven’t already done so, please backup your website.
Block PHP execution in untrusted folders
This is a bit technical but let’s try to simplify it as much as possible.
First, you need to know PHP is a scripting language that is used in web development. A PHP function is a block of code written in a program that can be executed to perform a certain task. Next, your WP website is made up of files and folders. However, only certain files and folders use php functions. Once a hacker gains access to your website, they can create their own folders, or they can insert their PHP functions into your existing ones.
To prevent such a hack, you can block the execution of PHP functions from any unknown folder. And you can also disable the PHP executions in places where it doesn’t need to happen.
For this, follow these steps:
Caution: Meddling with the backend files and database tables of WordPress is risky business and can cause your site to break. It requires technical knowledge. If you don’t know what you’re doing, it’s best to get professional help.
1. Access your website’s files via cPanel > File Manager. If you don’t have access to cPanel, you can use an FTP client like FileZilla. You’ll need your FTP credentials to access your files.
2. Go to public_html and you’ll see three folders called wp-includes, wp-admin, and wp-content, like so:
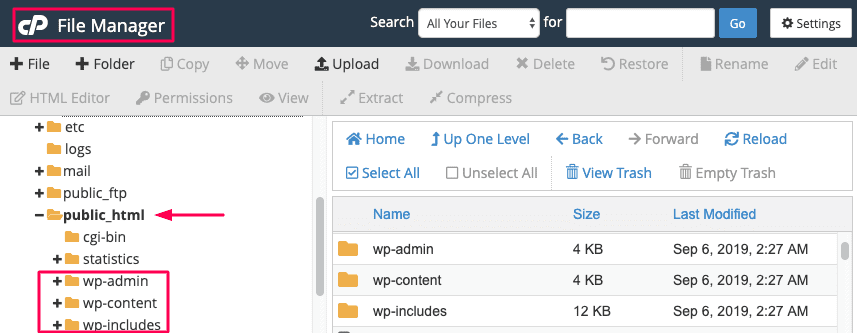
3. Next, look for the .htaccess file. If it doesn’t exist, you can create one by opening a text editor like Notepad and saving it as .htaccess.
4. You need to paste the following code in your .htaccess file.
<Files *.php>
deny from all
</Files>
5. If you’re creating a new file, you need to upload it to two folders: wp-includes and wp-content/uploads
This will alter the file permissions and prevent any PHP file from running in these directories. If this is all too technical, security plugins like MalCare automate this for you.
Disable file editor
If a hacker gets access to a WordPress Administrator account, they can take full control of your website. From the dashboard, they can edit the coding of your theme and plugins through the option of “Editor”. They can also upload their own scripts to display their content, deface your site, spam your users, etc. The most common hacks that occur through these editors include SQL injections , SEO Spam hacks and Japanese SEO Spam.
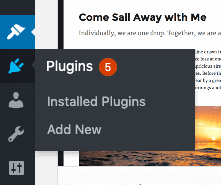
To find the editor, go to Appearance > Editor. And Plugins > Plugin Editor like so:
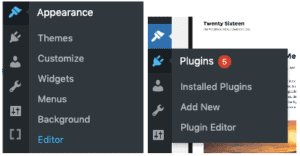
To disable the editor, you need to access your wp-config file. The same way we accessed the website’s files using File Manager or FTP can be used here as well.
The next part requires technical coding knowledge and comes with potential risk of breaking your site if not done correctly. If you don’t know what you’re doing, it’s best not to attempt it even though it seems so easy. We recommend using the ‘Disable file editor’ feature in MalCare.
If you wish to carry on with the manual method, we’ve detailed the steps you need to carry out.
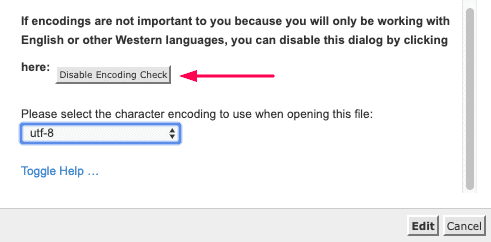
1. In your File Manager, find your wp-config file and right-click to get the Edit option.
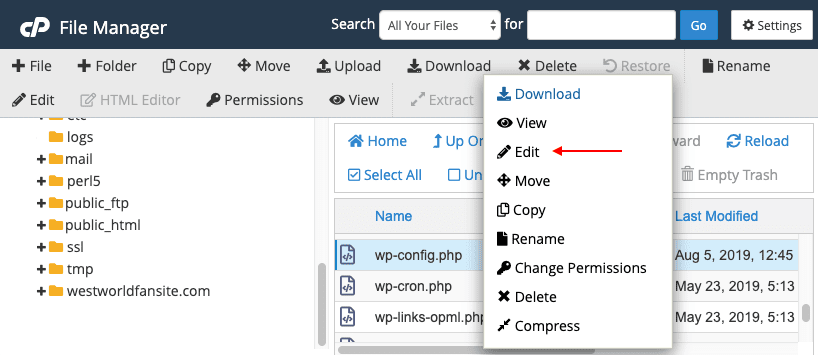
2. Here, you will see more information about it and you can select Disable Encoding Check. Then proceed to Edit.
3. Now, it opens up your wp-config file and leaves you wondering what to do next! Don’t stress. Scroll down and find the line:
/* That’s all, stop editing! Happy publishing. */
4. Above this, paste the following code
define( ‘DISALLOW_FILE_EDIT’, true );
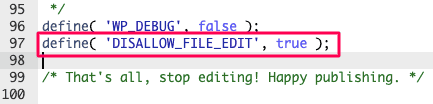
5. Save changes and close the editor.
6. Return to your dashboard and you’ll see that you no longer get the editor option.
Note: If you do not have access to cPanel, you can download your wp-config file via FTP. Open it in any text editor and add the line of code. Upload it back to the website the same way you downloaded it. You can overwrite the old file.
Change security keys
To log in easily, WordPress stores your credentials so you don’t have to enter your credentials every time you want to login. But what’s important here is that it’s stored in an encrypted form.
If the data is stored in plain text, when a hacker gets a hold of the data, they can just read it. If the data is encrypted, it will look like random text that they cannot use.
To encrypt the data, WordPress has to use something known as security keys and salts. In simple terms, keys are random variables that encode your admin username and password, and salts basically help improve the encryption one step further.
If hackers are able to get their hands on your security keys and salts, they can decipher the encrypted data and hack into your account.
It’s recommended to replace your old keys and salts from time to time. To get a fresh set of keys and salts you can use this link: Secret Key. You will get a page that looks like this:
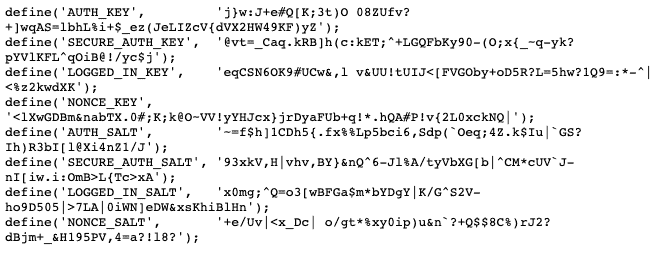
Now using the same method above, access your files and copy-paste the values that are generated into your wp-config file, here:
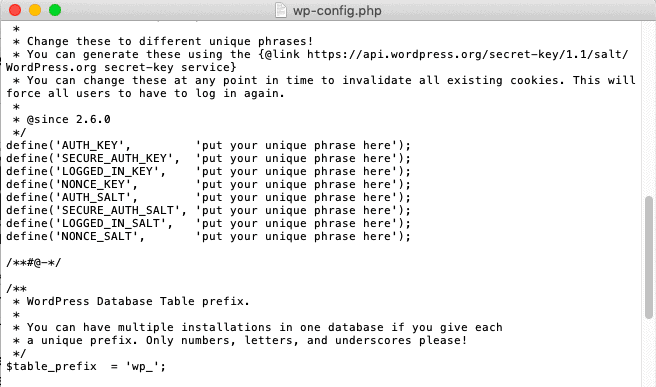
Here too, since it requires altering the code, we caution WordPress website owners to not attempt it if they are not tech-savvy. It’s best to use a security plugin that will handle this for you.
Disallow plugin installations
There are occasions when a user or a client might install a plugin without checking its compatibility or credibility, as thoroughly as you may do. This can lead to a number of problems on your website, so it is best to remove the ability for them to do so altogether.
You can disable plugin and theme updates and installations in two ways:
By adding a line of code to your wp_config php file
Follow the same method as detailed in the previous section, you need to add the following line:
define(‘DISALLOW_FILE_MODS’,true);
Please note: Please bear in mind that to update themes and plugins, and to install new ones, you will need to go back and delete this line of code.
Using a security plugin
The easiest way to enable and disable this function is by using a plugin. If you’re using MalCare, you simply need to click a button to enable it and thereafter disable it.
This is an extreme measure but a necessary one in cases where you have many users handling your site; or in the event you would like to limit your client from installing plugins unnecessarily.
Secure your wp-config.php file
One of the more critical files in your WordPress installations, wp-config.php is a prime target for hackers. Apart from containing the database access credentials to your website, wp-config is responsible for making a WordPress website function.
You can do two things here, in addition to disabling file editing: change security keys and disallowing plugin installation.
Hide wp-config.php
The first is to move the wp-config.php file one level up. This is not a safety move as such, but more to make it harder for malware to find the file. Moving the file doesn’t make it impenetrable though, so set expectations accordingly.
Note: There is no consensus amongst developers about whether or not moving the file is a good idea. In some instances, such as the Contact Form 7 vulnerability, this measure may be altogether ineffective. However, we like to err on the side of let’s-make-it-as-hard-to-be-hacked-as-possible.
Deny access to wp-config.php
Denying access is a much more concrete measure, and if you do this, you won’t have to move the file at all. Go to your .htaccess file and add the following code, right at the top:
<files wp-config.php>
order allow,deny
deny from all
</files>
There are a few things you can do to protect your wp-config.php file. This article has a checklist for all of them that you can pull off in one session.
Separating out databases
If you run more than one website with separate installations of WordPress, it is wise to keep the databases distinct from each other, and stored in different locations. Therefore if hackers gain access to one website, your other websites will remain unharmed—at least theoretically, because much depends on the security of the other websites themselves.
Although this is best accomplished during installation, it can be done later and it is worth the effort. However, this does require some familiarity with MySQL and its configurations.
Securing wp-admin
To take login security to the next level—which you totally should—you can force logins to be transmitted over SSL. Make sure you’ve installed SSL and addressed any mixed content issues.
Then navigate to the wp-config.php file that you are comfortable with by now, and add this code:
define(‘FORCE_SSL_ADMIN’, true);
We know this is a super simple step, but there is a reason why it is included here in the complex section. Plugins don’t always play nice with SSL, and sometimes SSL can be configured in unusual ways. For a full explanation of how this works and what to watch out for, check out this article.
Using a WordPress security plugin
To do much of what we have suggested above easily and quickly, install MalCare.
Good WordPress security plugins combine the website hardening measures you need to implement on your website, along with a web application firewall, bot protection and scanner. So now, you don’t have to worry about spending a lot of time figuring out the technical aspects of it.
However, not all plugins offer the same convenience and benefits. There are quite a few plugins out there, but we recommend MalCare simply because it gets the job done quick and easy in just a few clicks.
Once you install the plugin, your website is already secured. Here’s how:
- Scans your website regularly and checks for any suspicious activity
- Proactive firewall that blocks malicious traffic from visiting your site
- Real-time notifications for any malware present on your website
- 1-click malware cleanup
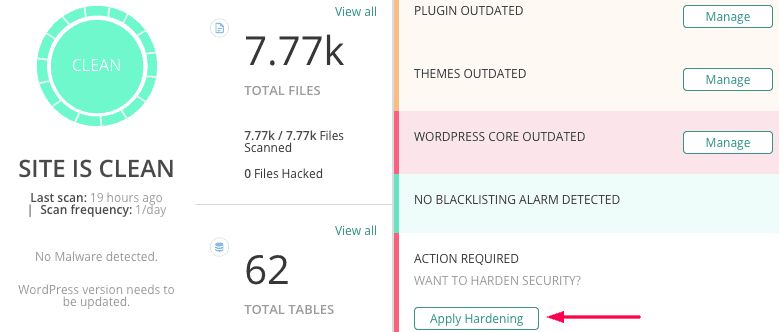
Quite apart from all of these features, there are different levels of website hardening you can implement on your website. These measures are optional because not all website owners will want to execute these security measures on their website. You can choose what to do according to your needs.
The three levels of website hardening you can implement are:
Essentials
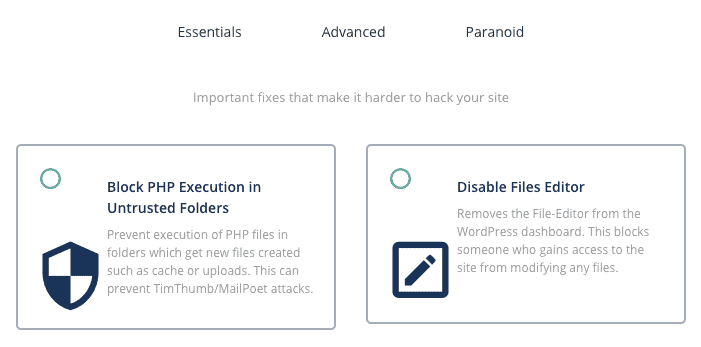
This enables you to block PHP execution in untrusted folders. You can also disable file editing. As we discussed earlier, this is a step you absolutely should take.
Under normal circumstances, you wouldn’t actually meddle with the files and folders of WordPress. You would only operate your website from the wp-admin dashboard. You also don’t need to edit anything in the files editor of themes and plugins. Disabling them closes some of the doors hackers can use to attack your site.
Advanced
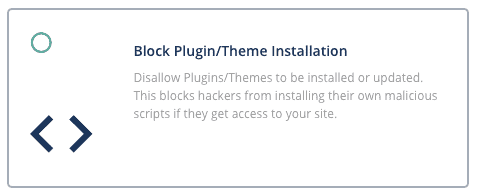
You can block plugin and theme installations which means no one can install new ones on your website. This measure is a bit extreme and should be taken only if you suspect a hack or you have too many people working on the website. If you want to install a new plugin/theme, you will need to disable this from the MalCare dashboard.
Paranoid
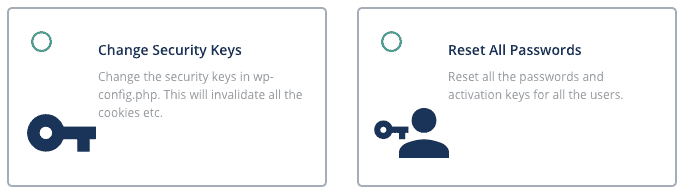
Here, you can change security keys and reset the passwords for all users. Often WordPress websites are operated by a team of people, with each person having their own login. This increases the opportunities for hackers to guess credentials and access your site.
It’s important to change all security keys and passwords at regular intervals. If you have a large team, this helps automate the process and make it faster.
In case you’re recovering from a hack, this is an essential step to take to ensure you don’t get hacked again.
Apart from this, you benefit from the following WordPress security features on your website:
- Limited login attempts
- CAPTCHA-based login
- Alerts for unauthorized access
- An activity log that shows file modifications/updates on your site
- It also analyses every IP request to protect you from hacks like brute force attacks
- It also prevents common WordPress security threats like SQL injections attacks, SEO spam, and your website being used in DDOS attacks
A full-featured WordPress security plugin is more than the sum of its parts. Even though these measures are effective protection against threats on their own, when used together they erect a formidable barrier against malicious activities. Install MalCare now, and rest easy in the knowledge that you have done the utmost to protect your website.
For extra credit
The following tips don’t fall into the category of WordPress hardening, but they are still best practices for the security-conscious website administrator. We highly recommend carrying out these measures, once you’ve finished with the list above.
Backup your website
The decidedly unexciting entry on this list: backups. We know; we develop the best-in-class backup plugin for WordPress.
The importance of a good backup is best illustrated by a bad scenario. Imagine you have spent months and years on building your website. It has customers, engaging content, generates revenue with ads, and has a reputation. And poof, one day that vanished. It could be a malware infection or a server failure with your web host; any one of a million reasons. Imagine. What would you give to have a backup under those circumstances?
Backups are vital. That is just common sense.
Keep your computer clean of malware
It is sometimes the obvious things that trip us up. Whichever computer you use—or indeed WiFi—has an impact on your website security. There is no point in hardening WordPress, if there is a keylogger on your computer; you’ve handed over your login credentials to a hacker.
Always keep everything updated
Apart from WordPress itself, it is important to keep themes and plugins updated. Vulnerabilities are discovered every day, and developers of plugins release patches to address those vulnerabilities.
If you aren’t using any plugins or themes, get rid of them. You can always reinstall them later, if you need them again.
As an aside, this is a core reason to purchase plugins. A paid plugin is often actively maintained and has a support channel for issues you may face. At MalCare, we use our experience with hacked websites to improve our security plugin every day. An actively maintained plugin is an investment in security.
Use SFTP
If you use FTP to transfer files to your server, consider switching to SFTP instead. It works in much the same way for transferring files, except that it does so using SSH. The data that is transferred is encrypted and cannot be read while in transit. Also, SFTP uses authentication for both the user and server.
SFTP is becoming the new standard, and replacing FTP as a result. The configuration is practically the same, so there is no good reason to continue with the legacy protocols.
Use a trusted web host
Most security articles (like this one) will focus heavily on what you, as a website administrator, can do to keep your website secure. Granted, there is a lot you can do, and most vulnerabilities are brought in by installed applications. However, that doesn’t mean that the server is invulnerable.
There is little you can do if your web host doesn’t do their part in protecting their servers. Servers are also vulnerable to attack, and not just of the digital variety. Are the servers in a physically secure location, for instance? Could a hacker gain access to the room and steal data that way? These are important considerations, but again a website administrator has limited control in this regard.
So what can you do? Pick a trusted web host. A good web host is transparent about their practices, and will include concrete measures they undertake to protect their servers from attack. This is not the place to cut costs, because an inexpensive web host could prove to be a very costly decision in the long run.
Conclusion
We cannot stress the importance of installing a WordPress security plugin enough.
Removing malware is a painstaking and difficult process, subject to missteps and costly errors. Only experts should undertake the process at all, and that can be an expensive proposition. Plus, you will already have lost data, traffic, reputation and much more by that point.
So yes, take a preemptive approach to security, and install a good WordPress security plugin. Then come back to this article and implement hardening measures, and then finally audit your website to check for common WordPress hardening mistakes.
Your future self will thank you for your foresight.
FAQs
What is WordPress hardening?
WordPress hardening is a catch-all term used to describe settings and configurations that increase the security of your website. These techniques cover the gamut of website assets and strengthen known weak entry points, in order to reduce the risk of infection.
Why should I harden WordPress?
If you care about your website’s security, and by extension the safety of your visitors’ data, then that’s why you should harden WordPress. These are simple measures to take in order to address vulnerabilities and reduce the risk of malware infection.
Remember that getting rid of malware is much much harder than preventing its infection in the first place.
Is it difficult to harden WordPress?
There are measures you can take to harden WordPress that are simple and done via your dashboard. Those aren’t hard. There are others that are a little more complex, but installing a WordPress security plugin will go a long way to mitigating that complexity. And let’s face it: installing a plugin is not difficult at all.
Do I need to harden WordPress if I have a security plugin?
Yes, because even though a good WordPress security plugin will include quite a few of the critical WordPress hardening measures, they will not be able to perform all of them. This is very simply because things like choosing a strong password or implementing strong authentication protocols is outside the scope of a security plugin.
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








