How to Remove Malware from WordPress Site
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.
If you suspect a hack or suspicious activity on your website, it can be a nerve-wracking experience. Until you know for sure, you cannot determine the reason, nor the solution. Wondering how to remove malware from WordPress site?
Do not worry, we will help you clean malware from WordPress, determine the cause, and save you any future trouble.
The first thing to do now is to scan your website.
A scan will confirm if your wordpress site is infected with malware. It is important to know this information because malware attacks can wreak havoc with your WordPress site if not identified in time. Malware can stay hidden on your website and redirect your users, show them indecent content, cut off your access, or even steal confidential information.
This sounds like a nightmare, but there is a solution, and we’re going to show you exactly how to fix this situation by removing malware from WordPress successfully.
TL;DR: The first step to removing malware from your site is to scan it with MalCare. Then use the one-click malware removal feature to auto-clean your site in minutes. Remember that malware gets worse the longer it remains on your site, so act fast.
If your WordPress site has been malware on it, it’s crucial to understand how to remove it as soon as possible. Hackers inject harmful scripts into your site, which can be hidden in many places and appear in various forms. For example, a common issue like the WordPress redirect hack could impact every post and page, no matter how many you have.
The presence of malware can lead to significant financial losses for both businesses and individuals, disrupt website functionality, harm user experiences, damage SEO rankings, and even result in legal complications. The recovery process can be incredibly stressful. Moreover, malware often creates secret backdoors, so simply removing the visible malicious code might not be enough; it could just keep coming back.
Remember that the effects of being hacked amplify the longer malware stays on your site. It multiplies, extends its damage, and can spread to other websites. If you don’t address it promptly, your WordPress hosting service might suspend your account, and your site may get blacklisted by search engines like Google. Quickly scanning and cleaning with a WordPress malware removal plugin is key to minimizing troubles and restoring your site’s health.
Step 1: Scan WordPress for Malware
Identifying malware on your WordPress website is not as easy as it sounds. You may have already noticed something going awry, but the truth is that malware is sneaky, it can hide from the admin very easily and you may be the last person to see issues on your website while your users are noticing redirects and spam.
So how to confirm if your WordPress site is infected with malware?
The best way to confirm is to scan your website. There are various ways to scan your website, but not all are equally effective. We will go through the three most common ways to scan your website.
A. Scan using a security plugin
We recommend that you use a security plugin to scan your WordPress website, because security plugins such as MalCare do a thorough job, and can identify malware within minutes.
MalCare makes it very easy for you to scan your site. All you have to do is go to MalCare, install the plugin on your website, and then let the plugin work its magic.
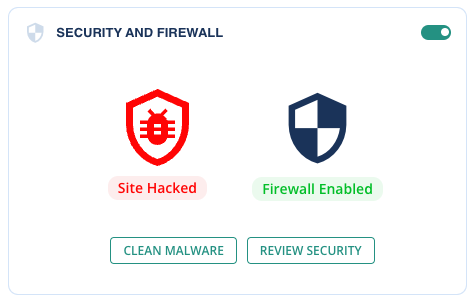
When you log in to your security dashboard, you will find the latest security status of your website.
You can click on the ‘Scan Site’ button to start scanning your website. Once you do, the plugin will conclusively tell you if your website has been infected with malware.
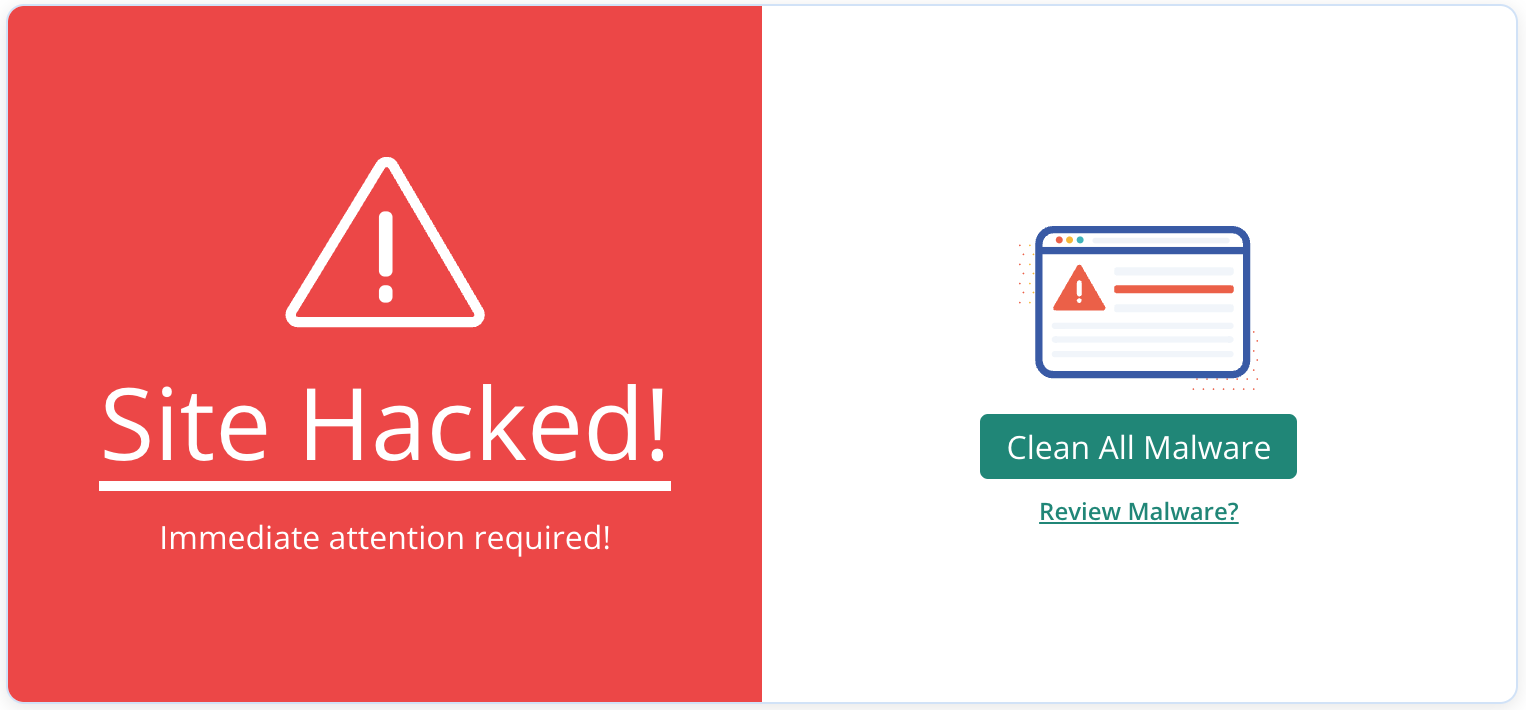
With this information, you can take the next steps to secure your website.
We recommend MalCare for a number of reasons. Most other security plugins use file matching to identify malware. Which means that they basically have a list of issues to look out for. But what happens when there is a new type of malware that is infecting your website? It isn’t on the list, so it is not detected.
MalCare does not scan your website the easy way, instead, it has a sophisticated algorithm that combs through your code to determine if your website is infected.
B. Scan using online tools
Security plugins are not the only way to scan your website. There are other ways, albeit not as effective. You can use online malware scanners to scan your website quickly, to confirm a hack.
With online scanners
However, it is important to remember that online scanners can only check the files on your website that are publicly visible, and if the malware is hidden in other files, then these scanners won’t catch it.
We recommend that you use these scanners only as of the first layer of the diagnosis and not by themselves. If an online scanner confirms a hack, you can either use a security plugin or hire an expert to do a thorough scan and cleanup of your hacked WordPress website.
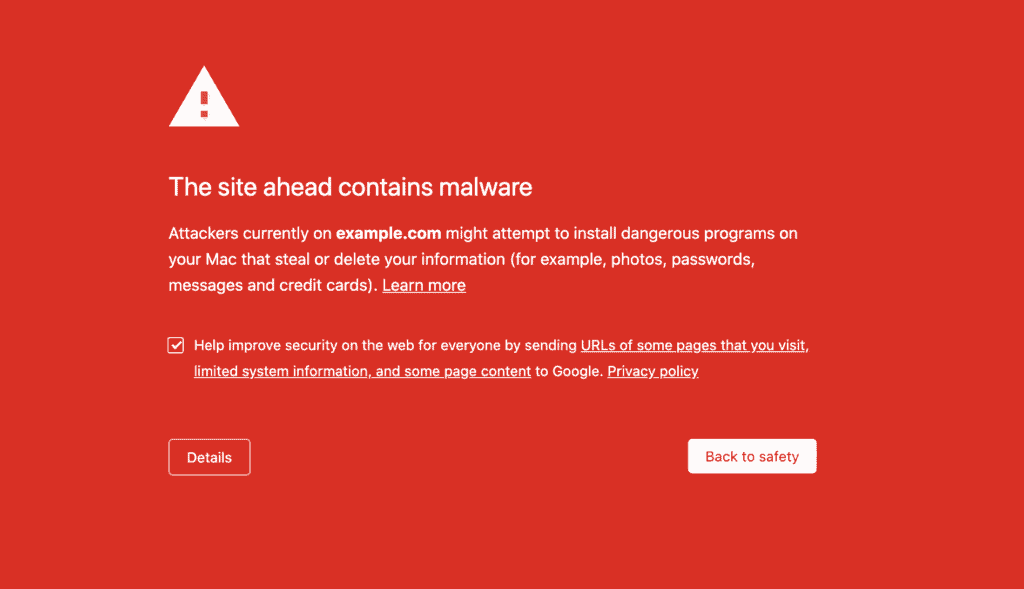
With Google Diagnostic Pages
Google offers a range of tools to help you determine if your website is infected. The browsing warning or blacklists are confirmation enough of malware on your website, but there are other tools that can help as well.
You can run your website through Google’s Transparency report, which will tell you if your website has been blacklisted. Or, you can use the Search Console which periodically scans the website.
C. Scan for malware infection manually
The final mode of scanning your website is by conducting the scan manually. We do not recommend this unless you are a security expert. Malware is complex and can hide effectively if you don’t know what you are looking for. Therefore, it is best to rely on experts who have spent thousands of hours building WordPress security plugins for this express purpose.
But if you must scan your website manually, look for recently modified files. To do this, you can use an FTP client such as File Manager and it will show you the last modified date on each of the files. If you notice any modifications on unusual files, it could be a sign of malware.
You can also check WordPress core files, which are what make up the foundation of your website. In order to check if the core files’ integrity is still intact, you will need to download WordPress from WordPress.org and match the files with the ones on your website. Make sure to download the same version that was installed on your website. If you notice any differences, it could be a sign of malware on your website.
Step 2: Remove malware from WordPress site
If you have confirmed that your wordpress site is infected with malware, you have already identified the issue. So you are closer to getting your site back on track.
There are different ways to remove malware from WordPress site, and some are more effective than others. We are going to discuss the two most common ones.
A. Clean malware from WordPress using a WordPress malware removal plugin
MalCare is the easiest way to clean malware from the WordPress website. Not only is it fast, but it is extremely effective. We recommend this course of action for anyone who has an infected site because MalCare is thorough, and its intelligent algorithm learns from every hacked site that it cleans. Follow these steps to remove malware from your WordPress website with MalCare.
- Log in to your MalCare dashboard
- Go to the Security section on the dashboard
- Scan your site, to get an updated status of your site
- MalCare will show you the latest status of your website
- Click on the Clean site or ‘Auto clean’ button
- Sit back as MalCare cleans up your website
This way, your website is not only rid of the malware, but MalCare also has a powerful firewall that protects your website from any future attacks that may occur.
B. Remove malware from WordPress manually
Before we get into the nitty-gritty of removing malware from WordPress manually, we must tell you that this course of action is NOT RECOMMENDED. Not only is there a chance of you missing out on malware, but if you accidentally delete a crucial file, it could break your entire site.
Having said that, if you must proceed with a manual clean-up of your WordPress site, this is how you do it. Just follow the steps mentioned below for WordPress malware cleanup manually.
1. Backup your website
First of all, make sure to get a complete backup of your WordPress site before you attempt to clean it up manually so that if anything goes wrong, you can restore your website. It is better to have a hacked site over losing it completely.
2. Download clean versions of WordPress core, themes, and plugins
In order to restore your website, you need uninfected files for your WordPress website. Given that malware could be anywhere on your website, it is best to download the clean installs of your website files from the WordPress repository. Make sure you download the same version as the ones on your website to compare the files and locate any malware.
3. Reinstall WordPress core
Now that you have the clean versions of your website components, it is time to start the actual WordPress malware clean-up process. The first step is to reinstall the core files. We have said this before, but ensuring that you use the same version as before is extremely important, or else your website will not work properly.
You can use cPanel or SFTP to access your WordPress files, and then replace the ‘wp-admin’ and ‘wp-includes’ folders. These folders do not contain any user content, so replacing them is relatively hassle-free. Once you do this, look for malware in the following folders:
- index.php
- wp-config.php
- wp-settings.php
- wp-load.php
- .htaccess
There is no one kind of malware that we can ask you to look for. Therefore, it is important that you ensure that any strange code you come across is malware before deleting it. Additionally, take a look at the ‘wp-uploads’ folder. If you see any PHP files in this folder, delete them, as it is not meant to have any.
4. Clean themes and plugins files
If you have identified malware in particular themes or plugins files, or it appears suspicious to you due to recent modifications, you need to clean these files. Themes and plugins files can be found in the wp-content folder. You need to go through each of these files one by one and compare them to fresh downloads to find any suspicious code.
Bear in mind, that not all changes in the files are bad. If you have customized any of your extensions, it will reflect as additional code in these files.
Important note: Never use a nulled theme or plugin on your WordPress site. Not only are they riddled with security vulnerabilities, they often carry hidden malware.
5. Clean malware from WordPress database tables
In addition to the files, you also have to remove malware from WordPress database tables. For this, you need to use your database admin panel. Once you log in to the admin panel, you need to look for any suspicious content. Check the ‘wp_options’ and ‘wp_posts’ tables specifically. If you want to clean your database tables effectively, you can go through this detailed guide.
Once you locate the table with suspicious content, you need to open the table and manually delete said content. Once you’re done with this, test your website to make sure that it is still functional.
6. Remove all backdoors
You have cleaned your WordPress site now. But unless you remove the cause for malware, there is a strong chance of your WordPress website getting reinfected. To secure your WordPress site from any future attacks, you need to remove all the backdoors.
Backdoors are gaps in the website code that allow hackers to inject malware into your website and gain access to it. You can search for common backdoor keywords or terms such as eval, preg_replace, str_replace, base64_decode, gzinflate, etc. and delete them if you find any.
Important note: The keywords mentioned above can also be used in website code, and may not be a part of malware. If you’re not an expert at clean-ups, it is best to use a WordPress malware removal plugin for this purpose.
7. Reupload cleaned files
Once your clean-up is done, you need to reupload these files to your website. This process is very similar to restoring a backup manually, and you can use cPanel or SFTP to do the same.
First, you need to delete the files and tables that you plan on replacing, and then upload the clean versions. Make sure you have your backup in place in case anything goes wrong in this step.
8. Clean the cache
Cache stores versions of your site in order to reduce the requests that go to your website server. But this means that if your site is hacked, the cached version of your website will also have malware. You need to clear the WordPress cache to make sure that your website is completely clean.
9. Verify each plugin and theme
Your themes and plugins could hide security vulnerabilities or traces of malware even after a clean-up. So verifying each one of them is important.
To verify your themes and plugins, you need to disable them all. You can do this by renaming your wp-content folder to anything else. Then, activate them one-by-one and see if your website behaves differently, or if the extension works fine. If everything goes smoothly, your extensions are malware-free.
10. Use a security scanner to confirm
Malware is not predictable, so it is worth confirming that your WordPress site is completely malware-free after cleaning your website manually. Use a malware scanner to scan your website thoroughly and determine that there are no traces of malware left on your website.
This step will give you additional confirmation and tell you if your efforts have borne fruit. If the scanner still detects malware, it may be prudent to use a WordPress malware removal plugin for clean up.
Step 3: Remove malware warnings from Google
When your site is infected, it is flagged by search engines and web hosts alike. Many websites and web hosts use Google’s blacklist too, so it is important to take off the malware warnings on Google. You can do this through the Search Console, which allows you to request a review once your WordPress website is clean from malware infection.
Make sure your website is completely clean of malware by doing a thorough scan before you request a review. It’s a critical step since Google will turn down your review request if it finds any malware. Keep in mind that Google checks these requests manually, so if you have several requests denied, you might be labeled a ‘Repeat Offender.’ If that happens, you’ll have to wait 30 days before you can submit another request.
Steps to remove your site from Google’s blacklist:
- Log into your Google Search Console account.
- Select the Security Issues section and scroll to the bottom of the page.
- Click on Request a review.
- Fill out the form with details of the actions you’ve undertaken to fix the security problems.
- Click submit to send your review request.
Once you’ve sent off the form, you’ll need to wait. It typically takes a few days for each request to be reviewed and processed. Remember, there’s no way to speed it up, and repeatedly checking or following up could actually backfire and get you marked as a repeat offender. So, it’s important to stay patient during this time.
What should you do if your site is clean but your review request is still rejected?
Occasionally, Google may deny a review request due to remaining signs of malware:
- Not clearing caches: Always remember to clear your WordPress and browser caches after cleaning up. If caches aren’t cleared, Google might still detect and flag malware, keeping your site on the blacklist. Check some pages that were flagged; if they show a 404 error, it means they don’t actually exist on your site anymore.
- Remaining problematic links: Double-check Google’s scan results for any links that might still lead to suspicious sites.
- Insufficient malware removal: If the cleanup was done by hand, there’s a chance it missed something. It might be necessary to use a security plugin to ensure thorough WordPress malware removal, indicating that manual efforts weren’t entirely successful.
Google Safe Browsing rarely has false alarms. Therefore, address the issues as explained above and submit a new review request.
Step 4: Protect your site from malware
If your website has been infected, chances are that it will get reinfected. Hackers tend to exploit backdoors or security vulnerabilities on your website, and it becomes easier to hack a website once it has already been hacked. But there are ways in which you can secure your website from future attacks.
Don’t remove malware from a site with a backup
While no one advocates for WordPress backups like we do, using them to restore your site after a malware infection is not a good idea.
- You could lose any updates or changes made since the backup was created.
- It’s difficult to know which backup is clean, especially if you’re not sure when the malware infected your site.
- Restoring from a backup could reintroduce the same vulnerabilities that were exploited in the attack.
The only scenario where a backup is useful is if the malware has completely decimated your website, leaving no other option. In such cases, a backup could serve as a foundation for rebuilding your site.
Symptoms of having malware on your WordPress website
When malware infects your website, you may not notice big changes. But there are other ways in which malware will affect your website. This can be noticed through the following symptoms.
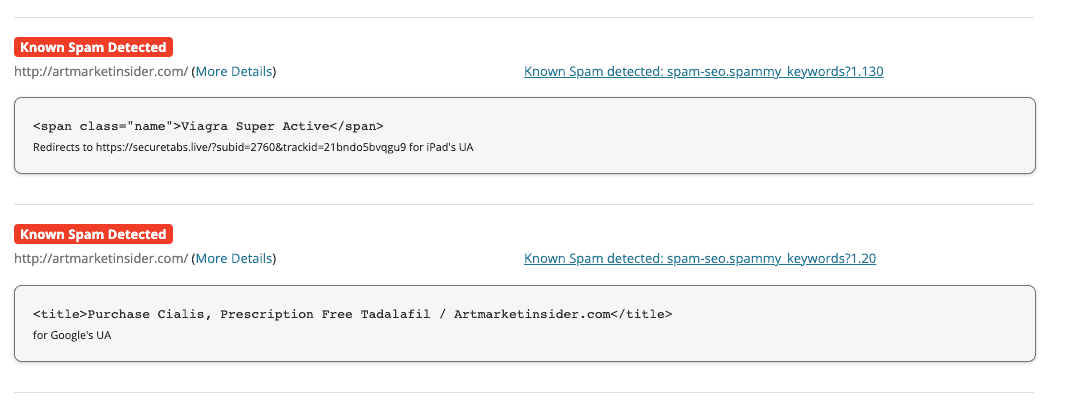
1. Spam results for your website on Google
If you have spent time working on the SEO of your website, then this can especially be a low blow. Google your brand name or the keywords you rank for, and examine the search results. Do you see any of these warning signs?
- Meta descriptions have junk values, like pharmaceutical or unrelated keywords.
- Google is indexing pages that shouldn’t exist on your website. When you click through one of these links, it takes you to a page you’ve never seen before.
- Japanese keyword spam in the search results
- Site may be hacked notice appears alongside your website name, warning off potential visitors
- The big red notices indicating that your website is now on Google blacklist
2. Visible issues on your website
Malware plays havoc with your website, and unfortunately, sometimes that is visible to every visitor on your website. You, as an admin, may not see some of these symptoms at all. However, your visitors are experiencing some of this—and it is costing you.
- You may have clicked through from Google and seen spam pages. Hackers piggyback on legitimate sites for their SEO rankings, so that they can drive traffic to their own spam websites. Alternatively, these pages could have phishing content, designed to extract credentials from people.
- Pop-ups with weird and unrelated content can appear on your website. Spam pop-ups can either be due to malware on your website, or something that has gotten through an advertising network. Either way, it is showing up on your website, and needs to be addressed.
- One of the more egregious kinds of malware, malicious redirects cause WordPress admin a ton of grief. Often, they cannot stay on any of their websites for more than a few seconds, before being taken to a spam website.
- You may also see code appearing on your pages, where none was visible before. Code isn’t supposed to appear on the frontend of your website, so this is bad regardless of malware. Partially broken pages can be because of a coding error or a plugin malfunction, but are often indicative of malware.
- Another awful symptom is the white screen of death. When anyone visits your website, nothing is visible: nothing loads, there is no error message, and refreshing your browser does nothing. It can be very disconcerting.
3. Changes in the users, files, or database of your website
Hackers can and often will alter configuration or user settings that are visible from wp-admin. These changes are often impossible to discern without an activity log because they can be really small.
- Code changes in the core, plugins, and themes files. WordPress is built with software, and malware can insert itself anywhere.
- You may also see changes to posts and pages, or completely new pages often with spam links and deceptive content. Google will also index these pages, and they will show up in analytics and your sitemap.
- New or upgraded users usually with unauthorised admin privileges. If you’ve enabled the setting to receive emails about the creation of new accounts, you might see weird names and email addresses showing up as admin accounts.
- Configuration settings change without warning. Some admin are familiar with how the core files, like index.php and .htaccess, work, so they can see additional code added in those files. If they try removing the extra code, it often comes back almost instantly. This is typically the case with the wp-vcd malware.
- On your plugin dashboard, everything might look fine, but if you look through the wp-content folder, you might come across fake plugins. These are folders masquerading as plugins, with malware hidden inside. Usually fake plugins have odd names and do not follow WordPress naming conventions. It is not a rule, but more of a signal for identification.
4. WordPress hosting flags issues with your website
Often web admin are the last to find out about malware on their websites, so these signals come out of the left field. WordPress hosting providers are very vigilant about malware on their servers, because they can experience a ton of problems as a result. Good web hosts will scan their servers and the websites on them for malware regularly.
- If your website is found to have malware, your web host’s first response will be to suspend your website and ask questions later. This means your site is now offline. They will probably send an email about it as well, since malware and its attendant deceptive content usually is a policy violation.
- Another signal to look for is if your website is using more server resources than normal. If the increase is steady and sustained, in line with growth you see on your website, then it is fine. But malware and attacks cause the CPU and memory usage to spike abnormally, which will lead to the web host sending you a warning.
5. Performance issues
Malware can also affect the performance metrics of your website. These symptoms are harder to tie to malware off the bat, because they could be caused by other factors like poorly coded plugins or no caching. However, if you see your website becoming noticeably slower, it could be a sign of malware.
Additionally, if server resources are exhausted because of malware, you might see 503 or 504 site is inaccessible errors. Again, these can be caused by other things.
6. User experience issues
Your website visitors are the intended targets of malware, so they will be the ones most likely to see the signs of malware. This is the worst possible way to find out about malware, so you should make it a practice to visit your website from an incognito browser from time to time, so you can see the issues firsthand.
Look out for these sorts of complaints from your visitors:
- Login issues
- Redirects to another site
- Website emails trigger spam warnings
- Deceptive content or spam pop-ups
- Website defacement
7. Unexpected behaviour in analytics
Some malware is entirely invisible so you might not see any of the symptoms above. You could look for signs that something is off, and the best place to do that is in your analytics.
Using analytics regularly will give you a sense of what is happening on your website; how many visitors you get, where they come from, their behaviour on your website, and so on. Any anomalies from the usual patterns should have a reason. Otherwise it could signal malware.
Google indexes your website periodically, and uses a frontend scanner to look for deceptive or harmful content. Google Search Console will flag security issues if the scanner detects malware.
Key points to takeaway
All the symptoms we have listed can be attributable to something entirely benign. However, if you see more than one, then the chances of malware on your website are pretty high. When trying to figure out if your website has malware, you need to remember a few things:
- Hackers want malware to remain on the site as long as possible, so they design it to be undetectable and prolific
- Symptoms can be inconsistent, appearing and disappearing without any discernible pattern
- Malware can be entirely invisible to everyone, except Google
How did your WordPress Site get infected with malware?
You may have taken measures to secure your site, and still ended up with malware. This happens because code always has gaps. Your WordPress website is entirely made up of code, so it is important to realize that no website is 100% secure.
This can sound disheartening, but there are ways in which you can secure your website so that even if there are hacks and attacks, you can avoid them or keep the damage to a minimum. But if you are wondering what causes hacks in the first place, here are some common causes:
- Vulnerabilities in themes and plugins
- Undetected backdoors
- Weak passwords
- Unnecessary user privileges
- Active old accounts
- Unsecured communication
- Web host issues
If you have MalCare installed, it will detect vulnerabilities in advance and alert you. While also securing your website from other issues.
Impact of malware infection on your WordPress site
You already know that malware is bad for your website. But how bad is it exactly? The effect of malware on a website can be far-ranging. Depending on your website, the type of malware, and a few other factors, the presence of malware on your website can very well derail your business operations. These are just some of the consequences of malware that you may expect:
- ‘Deceptive site ahead‘ warning by search engines
- Account suspension by your web host
- Google blacklisting
- Website defacement
- IP blacklisting
- Traffic redirects to spam sites
- Addition of spam pages
- Data breach or loss
Malware is never good news, and the best course of action to follow is to secure your website at the earliest. If you suspect malware, get rid of it as soon as you can, because the situation will get worse the longer malware stays on your website.
Conclusion
Congratulations! You have taken the first step towards securing your website. The more you know about malware, the better you can protect your website. We hope this article clarifies all your questions and concerns regarding WordPress malware removal.
The best thing you can do for your website now is to get a security plugin, which not only protects your website but improves it. MalCare protects over 300,000 websites with its powerful algorithm, intelligent firewall, and thorough scans. But that’s not all, it actively enhances your website performance by offloading its processing to offsite servers and keeping bot attacks at bay.
FAQs
How to remove malware from my WordPress site?
If you suspect malware on your website, these are the steps you should take:
- Scan your website with MalCare—it’s free!
- If you confirm malware, it’s time for a clean up
- Take a backup of your website
- Clean WordPress from malware using a security plugin like MalCare
- Install a firewall on your website
- Change all the passwords
- Remove the malware warnings on Google
How do I check for malware warnings on Google?
Google flags websites with malware on them for its users. It will either throw up a ‘Deceptive Site Ahead’ warning, or blacklist your website from its search engine. Pay attention to user feedback and occasionally visit your website from an incognito window to make sure that there are no warnings attacked to your site.
How do I manually check for malware?
If you wish to check for malware manually, you can do the following:
- Check for recently modified files
- Check WordPress core file integrity
- Check the number of pages on your website
- Check the .htaccess file
How do I protect my WordPress site from malware?
The best way to secure your website is to invest in a security solution. But in addition to that, you can do the following:
- Use strong passwords
- Take frequent backups
- Conduct scans regularly
- Harden your website
- Update everything
- Install SSL
How do I find malicious code in WordPress?
There are three ways in which you can find malicious code on your WordPress website:
- Deep scan with a security plugin
- Scan with online tools
- Scan manually
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








