Sucuri vs Jetpack: Which Security Plugin is Right For Your WordPress site?
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

In a discussion about WordPress security, Sucuri inevitably comes up. It is one of the most popular security plugins available today. The pro plans come with a server-side scanner, a firewall, and unlimited manual malware removal.
Jetpack is an all-in-one solution for a lot of WordPress functionality; not surprising since it is built by Automattic. Also, having one plugin do the work of many is an attractive option, so Jetpack is very much a contender in our security plugin testing series.
But if we disregard the bells and whistles, which security plugin protects your WordPress site better?
We tested the top 5 security plugins to get that answer. Over 45 days, we pitted the plugins against malware, vulnerabilities, attacks and much more. Read on to read more about our results, and most importantly: choose a security plugin that actually works.
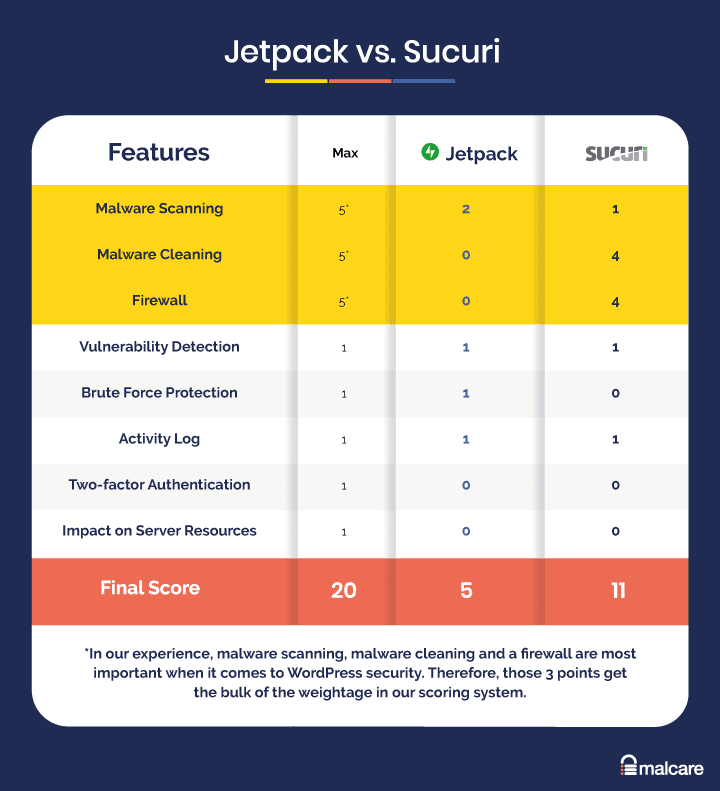
Sucuri vs Jetpack was a hard one to decide, because both failed in different ways. Ultimately, we think Sucuri wins out over Jetpack. Jetpack’s malware scanner managed to detect some of the malware, in contrast to Sucuri’s, which failed to detect anything. But Sucuri’s malware removal service did the job well, whereas Jetpack had no options for cleaning at all. Honestly, though neither of them were good security plugins, so our recommendation is to scan your site with MalCare.
Summary of Sucuri vs Jetpack comparison
In this winner-takes-all contest, Sucuri pulls ahead of Jetpack because of the excellent malware removal services they offer. However, it is a hollow victory, because Sucuri’s scanner is one of the worst we have seen so far.
Jetpack in a nutshell
Jetpack’s paid plans have an average malware scanner, which will detect some of the malware on your website. The rest of the security features are reasonably good, but they do not compensate for the scanner or the lack of malware cleaning and firewall. Overall, Jetpack is a miss.
Jetpack was the second plugin we tested, right after iThemes, and we were favorably impressed because at least it did something. Obviously, that doesn’t make it a good security plugin.
On the positive side, Jetpack’s activity log is great. An activity log is a critical tool for debugging and website security. We also think that the external dashboard on WordPress.com is swell, and is a familiar interface to work with. Since we are huge advocates of backups, we like that part of Jetpack’s features.
None of the above is reason enough to spring for a paid plan though, because Jetpack writes a lot of cheques it cannot cash. We already mentioned that the scanner didn’t work well. It detected about 30% of the malware on the website. The brute force protection is mediocre at best. We tried attacking the login page, and after a few failed logins, we saw a captcha. But our IP didn’t get flagged, and neither did we get an email alert. When we checked the logs, the attack was recorded though.
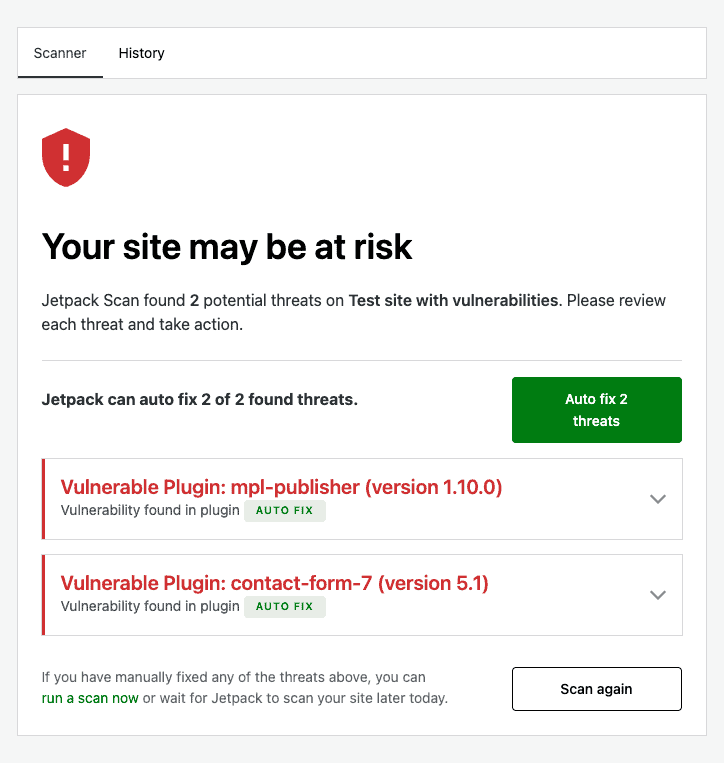
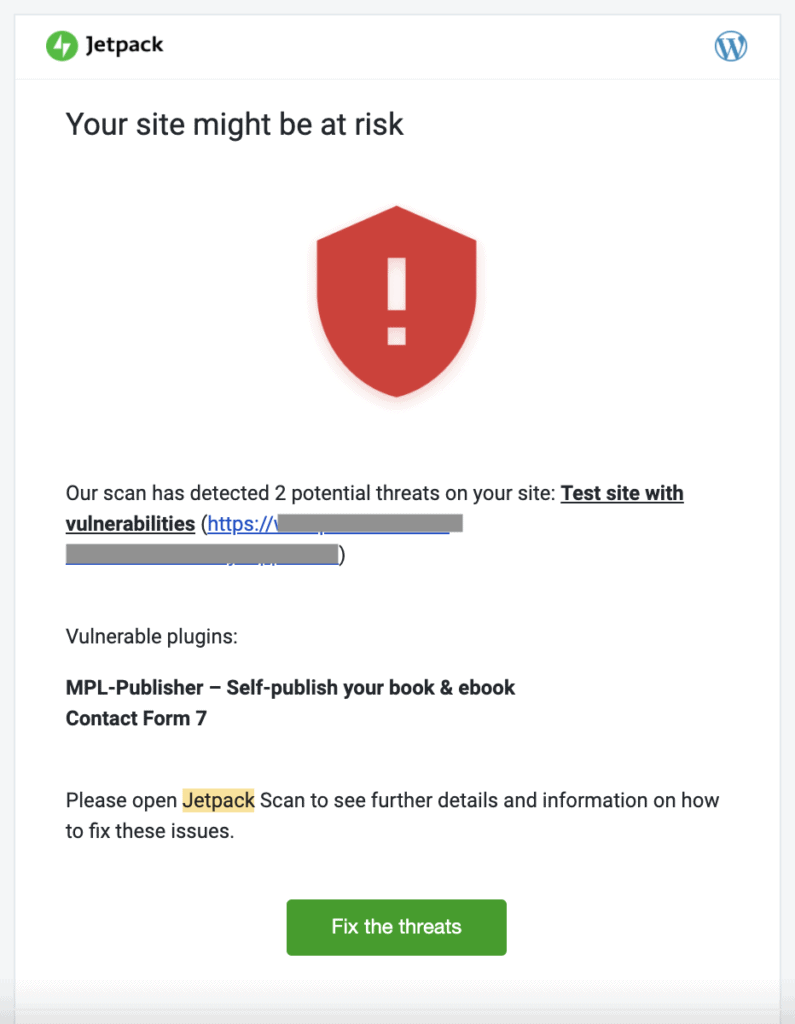
Also, Jetpack detects only some of the website’s vulnerabilities. Out of the 3 that we had installed, it flagged 2. In cases where websites have a lot more vulnerabilities, the ratio is sure to be much worse.
No security plugin is perfect, but we would want one that comes as close to perfect as possible. Jetpack isn’t that plugin.
Recommended read: Jetpack vs Wordfence
Sucuri in a nutshell
Sucuri has a mixed review from us, because its firewall and malware cleaning features worked well, but the scanner did not work at all. Malware scanning needs to be 100%, and no security plugin is worth it without a functioning scanner.
Sucuri is one of the most popular WordPress security plugins available today, and yet it falls short in one critical area: malware scanning. If the scanner doesn’t work, there is no way to know that your WordPress site is infected with malware. And if you don’t know that it is, there is no way you can address it.
In the other two aspects, firewall and malware cleaning, Sucuri fared well. The firewall blocked out most of the attacks, and the malware removal service was top-notch. There are some useful hardening options on the dashboard too. Unlimited malware removal requests is also a great deal, especially when compared to some of the other services available.
On the flip side, the configuration and settings were a nightmare, especially the firewall. We struggled with installing the firewall without a domain registrar, and frankly, it was a frustrating process. The security scans also loaded our server resources to the extent that we saw the difference on our website. Luckily our website was on dedicated hosting, otherwise shared hosting companies would have hit us with a violation email pretty quickly.
The takeaway here is that you have to choose between security and performance with Sucuri. That is a terrible compromise to make. Overall, Sucuri is both a good and bad security plugin, and therefore a contradiction. We do not recommend a contradiction as a security measure. Just saying.
Recommended read: Comparison between Sucuri and Sitelock
How to pick right security plugin for WordPress
In an ever-changing threat landscape, a security plugin is the one way to protect your website, data, visitors, and business. Hackers cause tremendous damage with malware, stealing money, data and identities from people. As a website owner, a security plugin is an essential part of your administration toolkit.
However, choosing the right security plugin is not straightforward. There are so many plugins, each claiming to be better than the next. So how do you pick the right one?
In terms of security, there are only 3 essential features of a security plugin: malware scanning, malware cleaning, and firewall. Everything else is a bonus. That’s not to say that brute force protection isn’t important, because it most certainly is. But if you don’t have the essential 3, then you may as well not have the others.
When evaluating a security plugin, these are the factors you should look for:
- Essential security features
- Malware scanning
- Malware cleaning
- Firewall
- Good-to-have security features
- Vulnerability detection
- Brute force login protection
- Activity log
- Two-factor authentication
- Potential problems
- Impact on server resources
The only plugin which has all the features needed to protect WordPress websites is MalCare. As we go on to talk about in this article, each of the others failed in some way or another, especially letting us down in the 3 essential areas.
Sucuri vs Jetpack: Head-to-head comparison of features
To make this comparison as useful as possible, we’ve organized the sections based on our listed criteria above. These are the most important aspects of a security plugin, but we also want to touch upon our other experiences like the ease of configuration, value for money, and so on.
We have presented our findings fairly, and as concisely as possible in order to help you make the right decision for your website’s security. However, if you need a security solution quickly, we recommend you install MalCare for unparalleled security for a WordPress site.
Malware scanning
Neither SiteCheck nor Sucuri’s server-level scanner detected the malware on our website. Jetpack’s scanner detected some of the malware.
Sucuri has two malware scanners: SiteCheck and a server-level scanner that you need to install from your Sucuri dashboard. We wanted to test both, because we often recommend SiteCheck, a free scanner, as a first-level diagnostic for websites. SiteCheck scans the publicly visible parts of your website, so just if it doesn’t find malware that isn’t a guarantee of a clean website. However, you don’t have to install SiteCheck to use it. So many admin find it easier to use in the event a web host has suspended their site, or Google has blacklisted it.
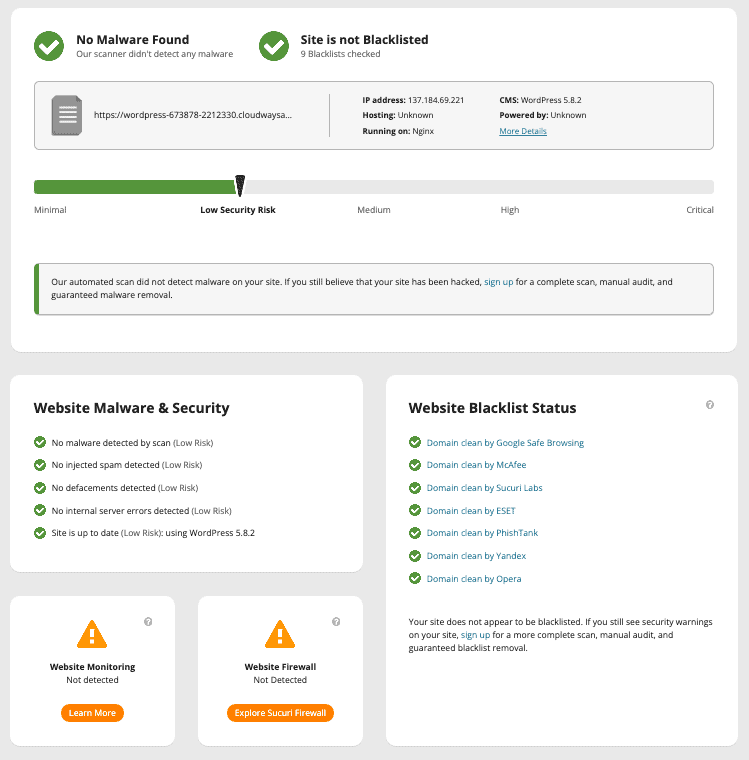
Moving to the server-level scanner, which comes with Sucuri’s premium plans, you need to install it onto your web server. You have the choice to do so manually, or input your FTP details to do so from your dashboard. Once we had it installed, the scanner took a long time to check our website for malware.
When the scan was completed, the results showed that our website was free of malware. The results were wrong, because our website was full of malware, both in the files and in the database. We then tried to run the scan again a few hours later, but the results were the same. There was apparently no malware on our severely hacked website.
The scanner is set to run once a day, but you can request ad hoc scans. The requests are put into a queue and then executed. The only thing here is that Sucuri warns you about running too many scans, because scans use up server resources. That’s.. not good. Scans shouldn’t take up a website’s resources because that has a performance impact on the website. We’ll come back to this point later in the article.
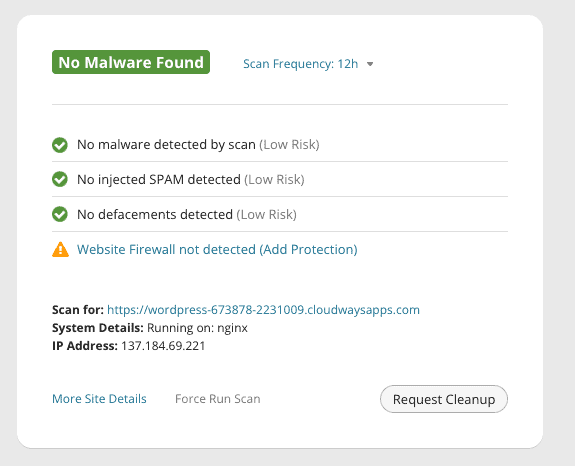
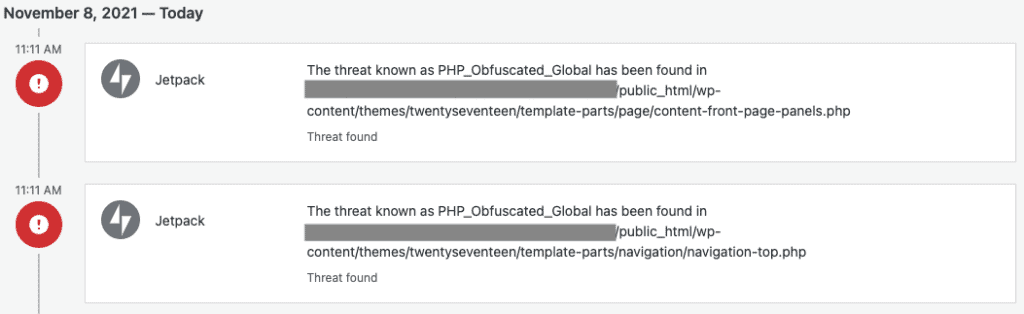
Jetpack has a malware scanner in its paid plans, and after seeing how Sucuri flaked out on the scanning part, we were pleasantly surprised to see that Jetpack actually flagged some of the malware.
The excitement was short-lived though, because Jetpack didn’t flag all of the malware. In fact, it didn’t detect a big chunk of malware. So although it did better than Sucuri in this respect, detecting some malware is as good as detecting no malware. The website is likely to stay hacked as a result. For a thorough scan of your website, look no further than the MalCare malware scanner.
Malware cleaning
Jetpack doesn’t have malware cleaning. Sucuri has a great manual malware cleaning service that got rid of the malware from our website within 12 hours.
We are conflicted about Sucuri at this point, because while we were seriously impressed by their cleaning service, the scanner had given our hacked site a clean chit. Based on those results, theoretically we wouldn’t have known that our website had malware. But since this was a testing activity, we requested a manual cleanup knowing our site definitely had malware.
As per our plan, we could expect our cleanup to have been done within 30 hours. On the face of it, that’s a long time to wait if your website is hacked. If your website is on Google’s blacklist for instance, time ticking past is lost revenue. However, we got a cleaned site back in less than 10 hours. We were super impressed.
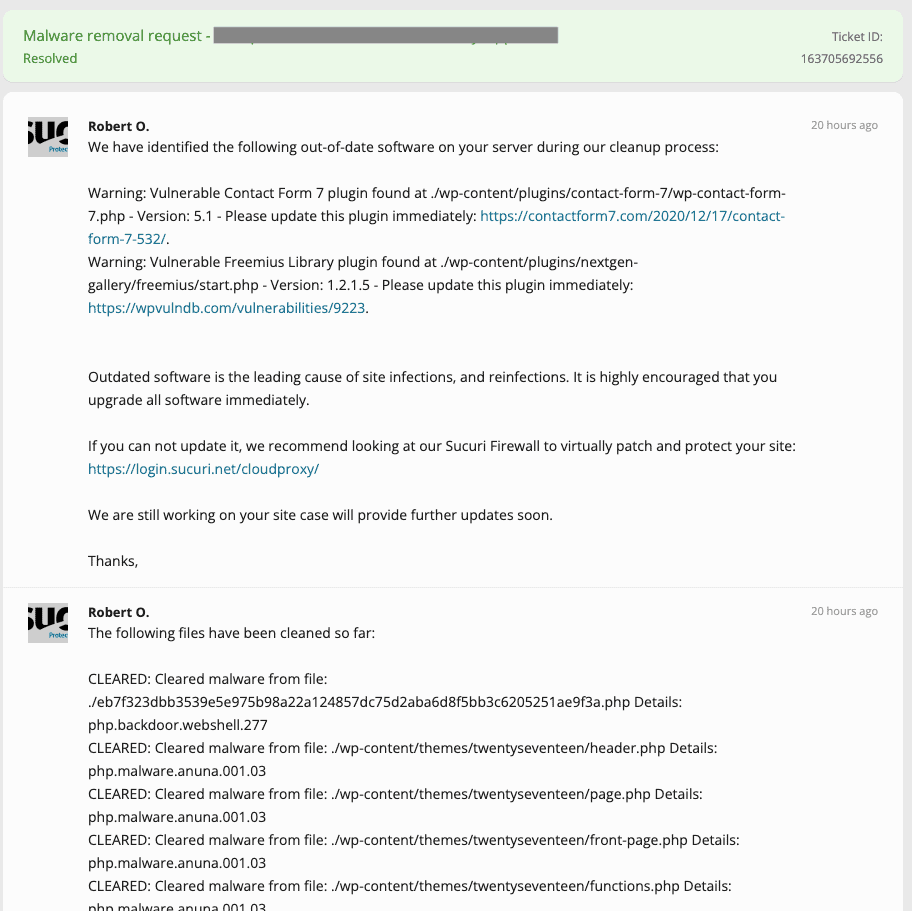
To request a malware cleanup from Sucuri, you need to fill out a form with all the details that you can put in. Indicate your tech abilities, put in your FTP credentials, and you get a cleaned site back. We checked the cleaned site with MalCare, and it was squeaky clean. Fantastic! The team gave us a post-cleanup checklist, warned us about vulnerabilities on the website, and we were good to go.
Except for one small thing: after Sucuri’s team removed the malware, and MalCare confirmed it, Sucuri’s scanner then said that the site was hacked. After it was cleaned by their team? Go figure.
Jetpack’s security plans don’t include malware removal, although they do say that they can get rid of some infections. After we ran the malware scanner, we saw that some of the malware was flagged, but none of it was fixable. In fact, in all the flagged instances of malware, Jetpack kindly recommends that we approach a malware removal service.
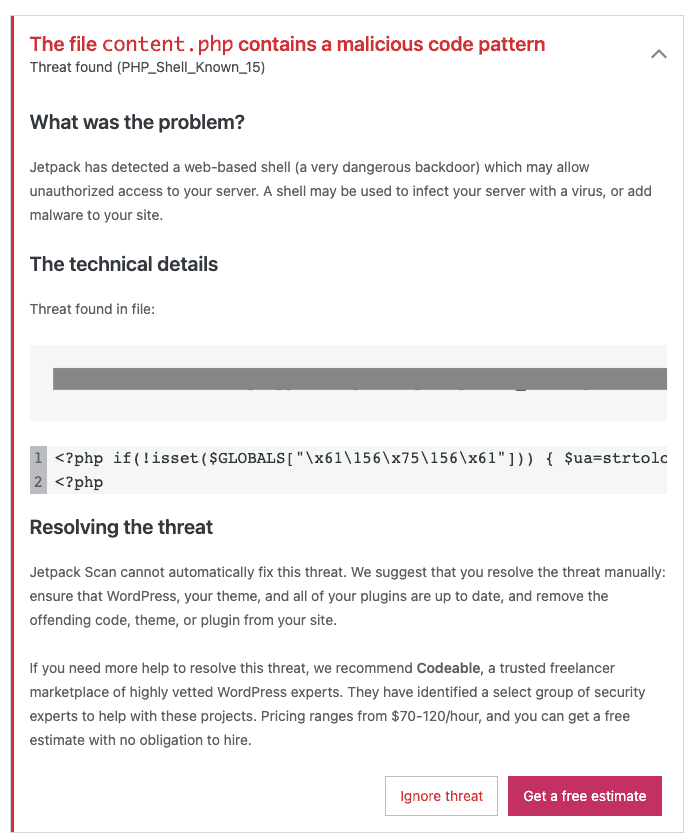
Our concern with Jetpack is that by flagging the location of the malware and the code itself, it seems to advocate manual cleaning as an option. This is not a wise decision. Hacked websites are minefields, especially since malware can hide anywhere. Manually cleaning malware is prone to human error, and runs the risk of breaking the website completely.
A malware removal service is an expensive proposition, and there is no guarantee that your website won’t get hacked again. The costs can pile up significantly in that case. Sucuri’s plans have unlimited cleanups, which is great. Our only problem with Sucuri is that the scanner won’t alert you to most of the malware, so how would you know when to request a cleanup?
We used MalCare to scan for malware, and also to clean our website in minutes. The auto-clean feature got rid of the malware from our site, without the need for FTP credentials, or requesting a removal. It was painless and seamless, and almost instant. Hard to beat that.
Firewall
Sucuri’s firewall did a decent job of dealing with most common attacks, but was a nightmare to install. Jetpack doesn’t have a firewall.
Sucuri has a firewall included with its security plans, but also has standalone firewall plans. We wanted to test the efficacy of the firewall, so we tried to configure it to our website.
Before we even talk about how the firewall works, we have to take out time to express how awful the experience of installing Sucuri’s firewall is. We had an existing premium plan, and there was already a website configured to the firewall. So when we tried to replace that website with our test website, Sucuri just refused to budge.
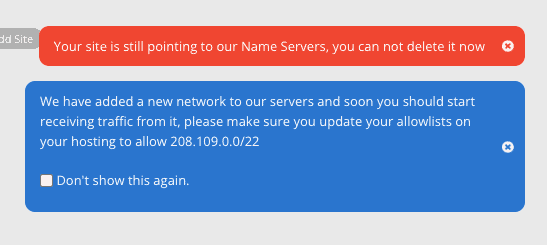
The issue here is that to use the firewall, you have to point the DNS of your website to the firewall’s nameservers. Which means that all the traffic hitting your website will first go through Sucuri’s firewall and then be redirected to your website. If this sounds complicated, that’s because it is insanely complicated.
In any case, we were able to configure a testing site with vulnerabilities like unrestricted file uploads, XSS, and SQL injection after a few days. The firewall blocked all our attempts to exploit these vulnerabilities and upload malicious files.
In all transparency, we weren’t able to test more complex attacks in our given timeframe. However, whatever we threw at Sucuri’s firewall was stopped.
Firewalls are an integral part of your website’s security. They keep out malware by preventing hackers from exploiting vulnerabilities in the website. Jetpack doesn’t have one, and that’s a gaping hole in their security plugin.
MalCare does an excellent job of protecting your website against different kinds of attacks. And it is easy to configure unlike Sucuri’s.
Vulnerability detection
Both Jetpack and Sucuri detected only some of the vulnerabilities on our websites.
Once we installed Sucuri’s server-side scanner, the scan told us we had a few vulnerabilities on our website. The scanner didn’t detect some of the more obscure ones and basically recommended that we update the outdated plugins and themes.
Interestingly, there is a post-hack tab on the Sucuri plugin on wp-admin. It has a list of versions of the installed plugins and themes, alongside the latest versions. In the small print on this page, Sucuri mentions that out-of-date software is a security hazard and often leads to malware infections.
Sucuri’s team also sent us a list of recommendations to update the out-of-date plugins and themes, so as to address the vulnerabilities. Again, they were only able to detect some of the vulnerabilities, not all.
Jetpack’s scanner picked up on some of the vulnerabilities as well, and gave us an auto-fix option; essentially, we could update them. There is little to differentiate between Sucuri and Jetpack in this instance. Jetpack interface was easier to manage, but then again Sucuri is a much more complicated plugin in general.
Brute force login protection
Jetpack adds a captcha to the login page after multiple failed login attempts, but doesn’t block the IP. Sucuri doesn’t seem to have a functioning login protection feature.
Jetpack has brute force login protection on their free and paid plans. When we tried to brute force the login page, we saw a numeric captcha being added after 10 failed attempts. The logs show all failed login attempts after the first 3 as a brute force attack.
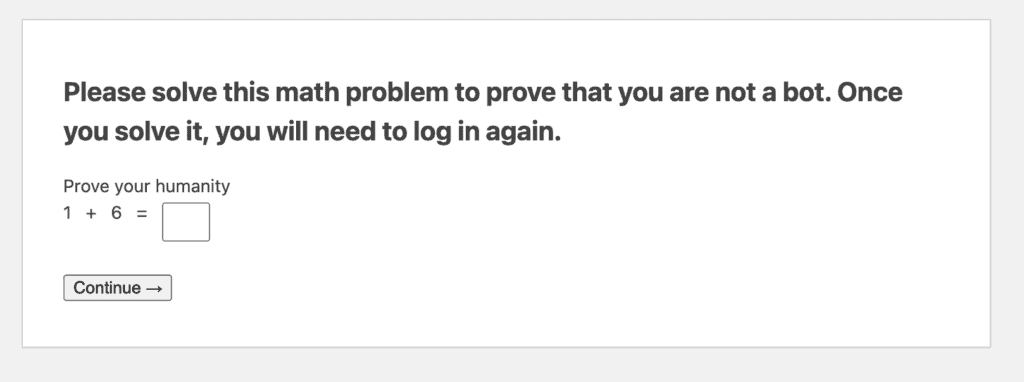
Jetpack also has an elaborate IP whitelisting feature, so we assumed that at some point we might get locked out of the website altogether. However, that didn’t happen at all. We tried upwards of 50 incorrect passwords for the admin account in less than a minute, and nothing happened.
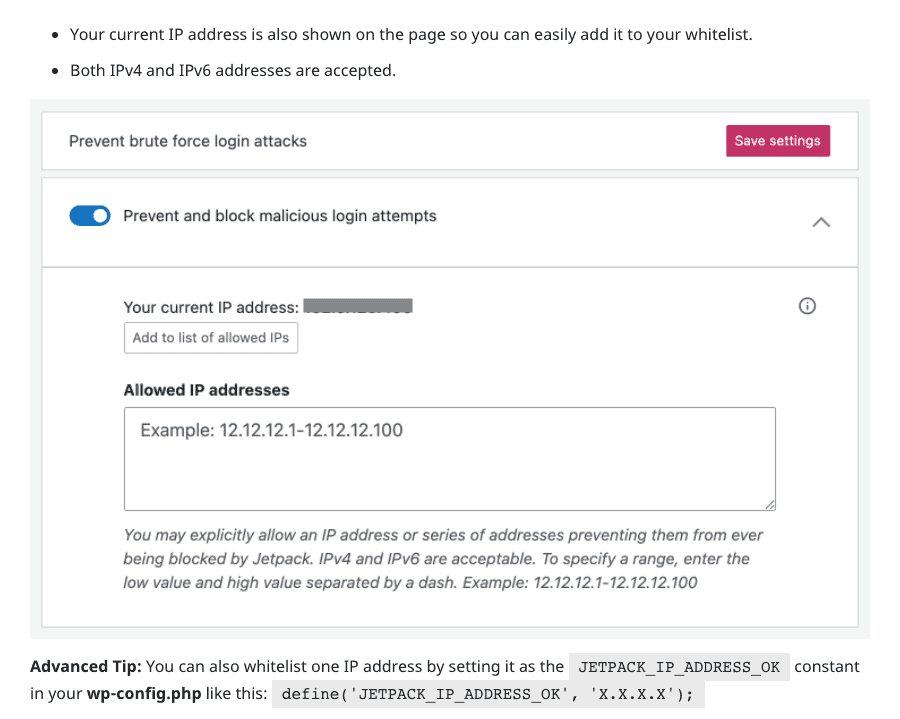
Frankly, IP whitelisting is a bit of an eyewash. Device IPs can change, so whitelisting an admin’s IP is no guarantee against a potential lockout. However, if the feature exists, it should work. But it didn’t.
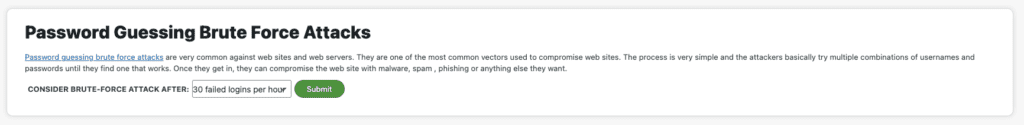
We thought Sucuri would do much better than Jetpack on this point, because it has an elaborate set of options for configuring brute force alerts. You can set the threshold at which an attack is considered to be brute force. The limits are unrealistic though, because there is an option to consider 30 failed attempts per hour as an attack, whereas in reality, a brute force attack pummels the login page at upwards of 100 requests per minute. In fact, there are usually so many login requests that the server is incapable of handling them.
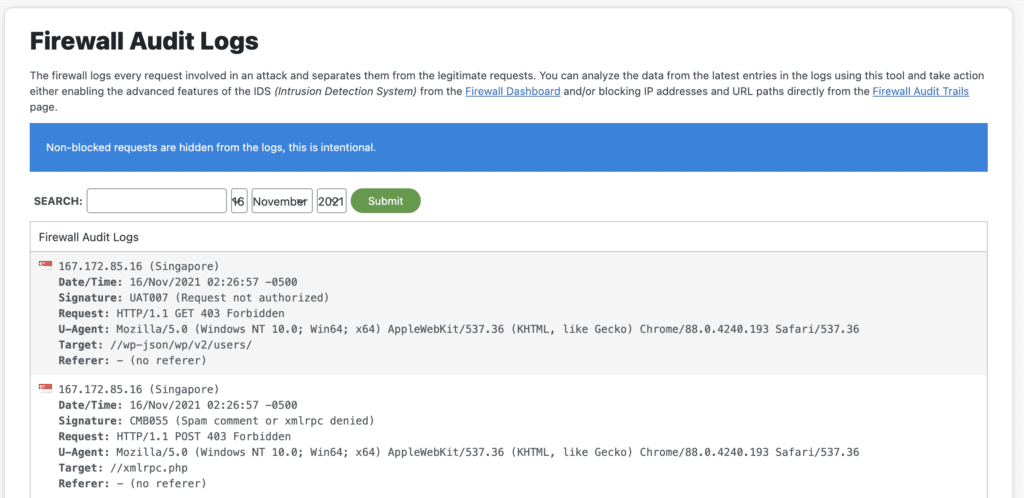
Long story short, Sucuri didn’t alert us about login attacks. The attacks did show up in the audit logs, but we didn’t get any alerts.
Activity log
Jetpack’s logs are great. They track every user and plugin action. Sucuri audit logs work too, but can be entirely incomprehensible.
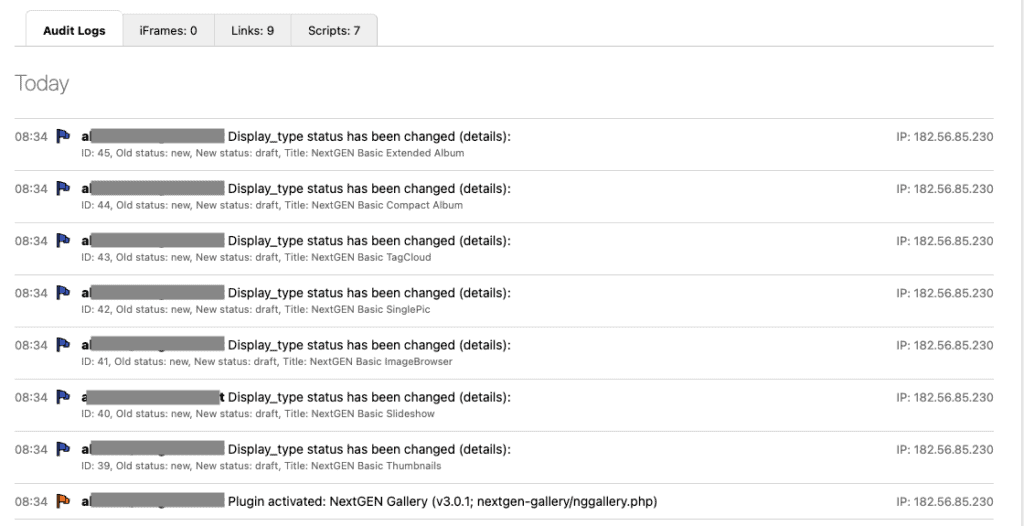
Sucuri’s audit logs track all user actions, and plugin and theme changes. All changes made to any files and tables show up in the audit logs. So far so good. There is also an option to set an API key to prevent attackers from deleting logs, by allowing Sucuri to save your website logs offsite.
The logs collect the requisite information like user, action, timestamp, etc. However, we noticed that in some cases, they are very difficult to understand. Case in point: we installed a gallery plugin on our website. The logs registered 7 different entries for the plugin, indicating that 7 files had been changed. Or so we thought. It was actually logging changes to the post template, but we couldn’t figure any of that out from the logs.
Jetpack has a great activity log feature, and it is available for preview on the free plans. The logs show all user, plugin, and theme activity, in addition to showing things that require immediate attention, like detected malware or vulnerabilities.
Jetpack’s data only goes up to 30 days though. Ideally, logs should save for a much longer time period.
Two-factor authentication
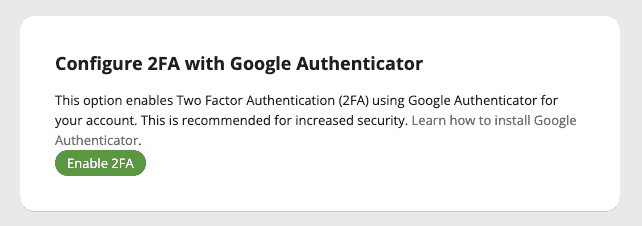
Neither security plugin has two-factor authentication.
There isn’t much to talk about in this section, because neither Jetpack nor Sucuri has two-factor authentication for your websites.
However, when we were testing the plugins, we looked for two-factor authentication on Sucuri. There is in fact two-factor authentication on the Sucuri dashboard, but it was available for your Sucuri account. Not your website.
Server resource usage
Both plugins will consume server resources to perform scans on your website. Sucuri’s scanner slowed down our website noticeably.
We give Sucuri points for honesty, because they claim to use server resources for scans right on the dashboard. Other that than though, it is terrible that they do it.
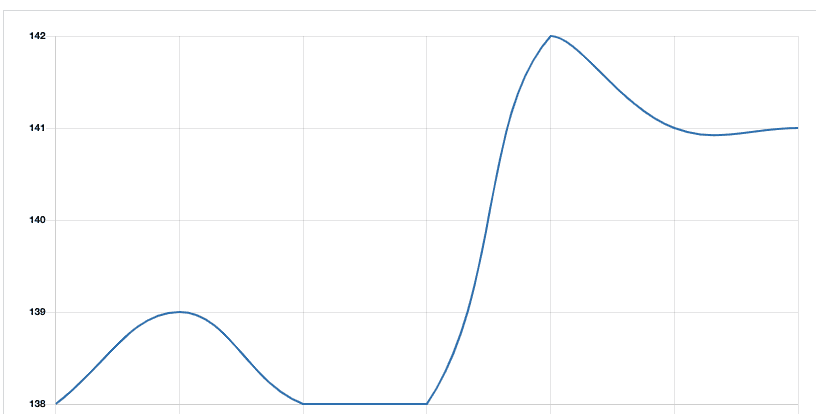
Sucuri scans showed a noticeable blip in our server CPU usage. And our test sites are small; hardly more than a 100 MB for the largest one. If we had a WooCommerce site or one with a large database, the performance of the website would be seriously affected. Plus, Sucuri scans also take a considerable amount of time. So the impact would go on for a while.
Apart from the CPU usage, in the General Settings on wp-admin, you will see that Sucuri uses your server to store data. Even if the storage space is negligible, the point remains that it is your website’s server space being used.
Jetpack also had an impact on the server resources. Granted, it was not as noticeable as Sucuri’s scans, but it is still not ideal at all.
Honestly, we are not impressed by this state of affairs. No website admin should have to choose between security and performance. A lack of either can affect revenue in major ways, so it should not be a trade-off.
Alerts
Sucuri’s alerts can fill up your inbox in an hour, so you need to be absolutely certain about what you want to be alerted about. Jetpack sends alerts about the critical stuff only.
Sucuri allows you to customise the format of the alerts, send them for specific actions, send them to certain people, and so on. You can also configure a setting to ignore certain IPs so they don’t trigger an alert.
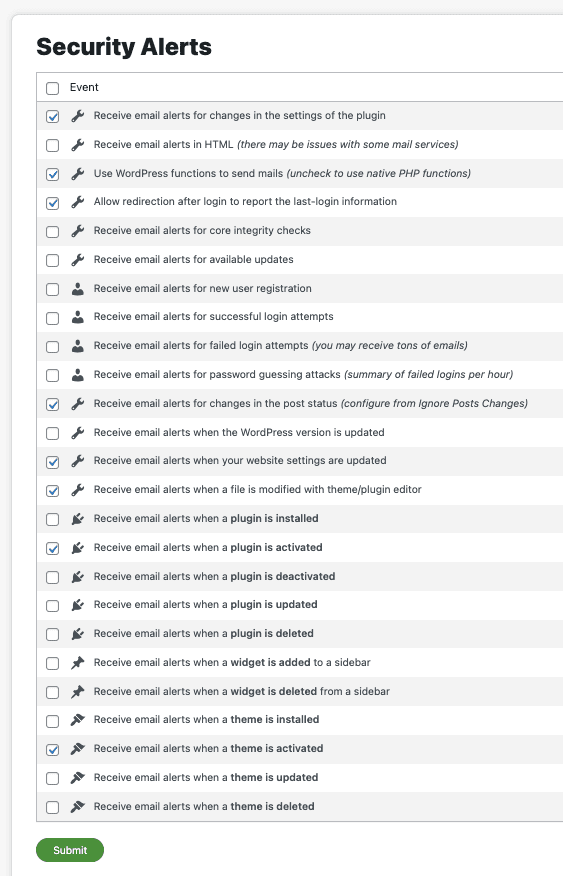
The sheer number of options for Sucuri’s alerts is staggering. Of course you only really need to configure it the one time, and then forget about it. But really, the options themselves deserve special mention. And if the number wasn’t daunting enough, the tech-speak was totally off-putting.
Ultimately the alerts are too granular to be useful. An admin should be able to rely on their security plugin to alert them to things that need to be dealt with, and filter out all the noise. In Sucuri’s case, we are fairly certain that there is a good chance of missing the signal in all the noise.
Jetpack handles alerts elegantly. There aren’t a million options to sift through, and the plugin will send you alerts about things that need your attention. Like vulnerabilities and malware, for instance.
As an aside, we also tested Jetpack’s downtime monitoring feature. It is supposed to alert us if the site goes down, but it didn’t. We crashed the site in a few different ways, and saw that Jetpack didn’t register those crashes at all.
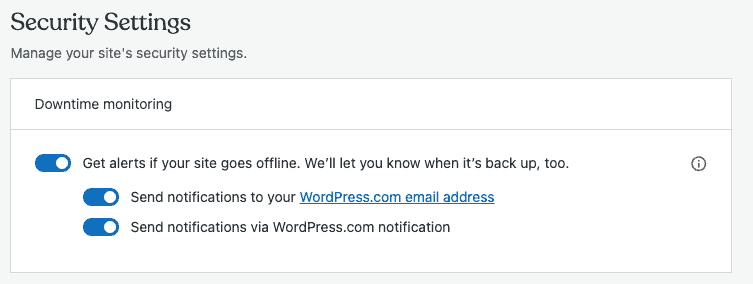
Although downtime monitoring is not a security feature as such, it is an important metric for your website. Down or crashed websites are often an indication of hacker activity or malware. Jetpack’s downtime feature doesn’t work.
Installation, configuration, and usability
Sucuri was easy in the beginning, but became progressively more difficult. Jetpack was easy to configure but the interface constantly prods you towards an upgrade.
Jetpack installation was tedious. Although your plugin is installed, there is no way to move forward without creating a WordPress.com dashboard. It serves as your external dashboard though, so you do need the account. It is just somewhat disconcerting to be taken back and forth from your own dashboard to Jetpack’s without a clear understanding of when and why that is required.
Sucuri’s installation was easy, and the frontend scanner started running right away. To access the paid features, like the firewall and the server-side scanner, you need to create an account on Sucuri. However the free version is self-sufficient.
Jetpack’s external dashboard is comfortable to use because it mimics wp-admin. However, there are a ton of locked features depending on your plan, so it is not the best user experience to see ‘upgrade’ everywhere. Some of the metrics are useless from a security point of view, so overall we are not enamoured of Jetpack’s interface.
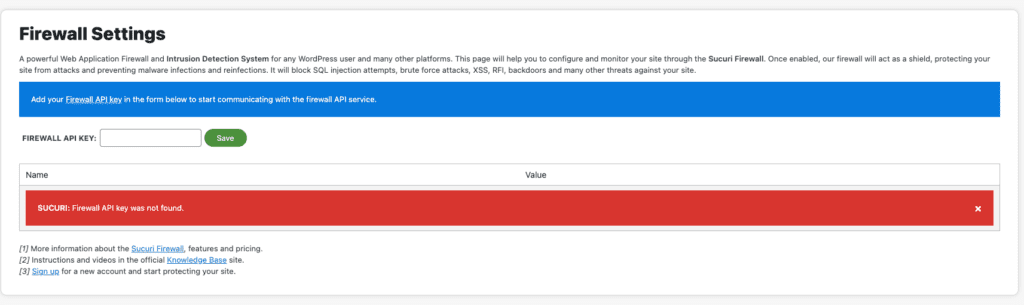
Having said that, we would prefer Jetpack’s interface to Sucuri’s. If we had to describe Sucuri in one word, that word would be confusion. There is just so much tech jargon in the configuration and settings. We actually spent hours trying to figure out what some of the terms even meant. Also, the descriptions are unhelpful, and in some cases condescending. Not sure why anyone thought it was a good idea to write descriptions that effectively say: if you don’t know what this means, best leave it alone.
Setting up Sucuri’s firewall was a nightmare. It may seem simple if you have access to a domain registrar, and the know-how to fiddle around with nameservers (which incidentally take a few hours to update). Our test site doesn’t have a domain, because we don’t want Google to index it or people to land on it accidentally, so changing the nameservers was not a simple task. If someone wanted to set up the firewall on a staging site, they would find it difficult to do without engineering assistance.
Jetpack: Extras
Jetpack combines multiple WordPress admin tasks into one plugin, so there are a lot of extras. We like that it has backups, because backups are super important to have for any website. Other than that, the WordPress.com account is familiar to use, although if you have multiple websites on one account, it is tedious to switch back and forth between them for management.
Sucuri: Extras
Sucuri has a ton of extra bells and whistles in their plugin. Unlike Jetpack that offers more than security, Sucuri is only about security. So we tried digging around in the features to see what could have an impact on security.
When you install the plugin, the first and biggest you will see is the WordPress integrity infobox. It looks really impressive, but it actually is a very dressed up version of a WordPress core file change monitor. There is obviously some utility to having a file change monitor for core files, especially since malware is known to infest core files regularly. However, the prominence and placement is misleading, in our opinion. A file change monitor is not the extent of WordPress security. Frankly, it isn’t even the beginning.
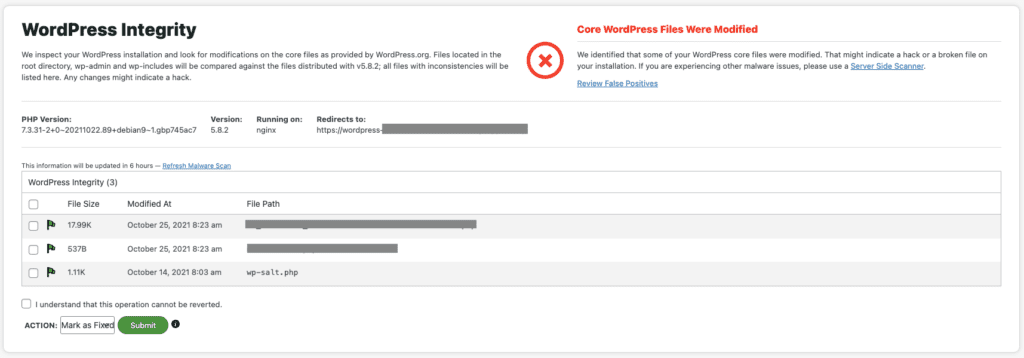
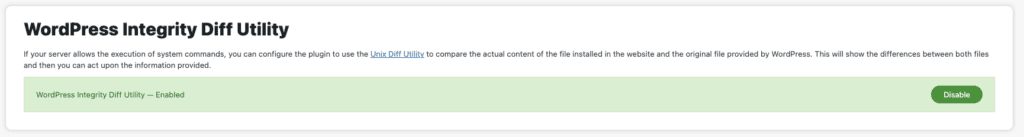
There is also an integrity diff utility to compare core files on the website with the original build. It is easier than using an online diffchecker for core files, if you are cleaning out malware manually.
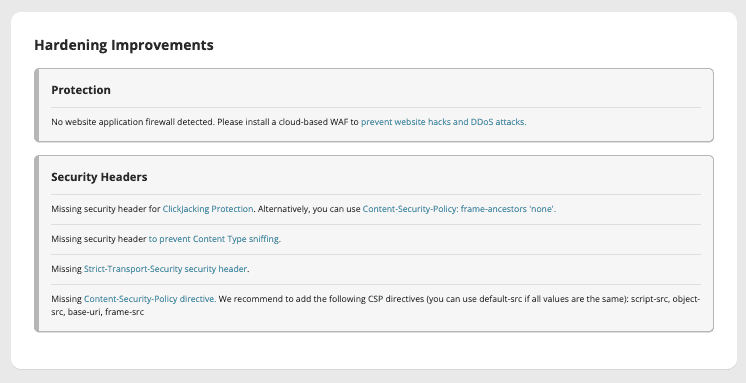
Sucuri has a ton of WordPress hardening options. Some of them are useful, while the others are older hacks that have since ceased to be useful security-wise.
For instance, blocking PHP in the uploads folder is a good idea, and so is the ability to change the WordPress salts easily from the dashboard. But this is not an unequivocal endorsement though. It would have been much safer to have the feature on the Sucuri dashboard rather than on wp-admin. If a hacker gains access to the website backend, the salts will be compromised because they are shown in plaintext.
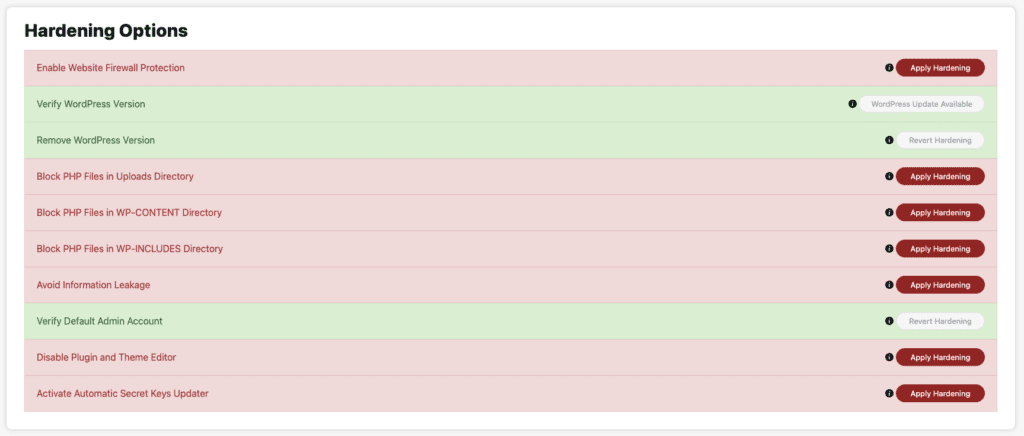
Things like verifying WordPress version, removing WordPress version, avoiding information leakage, and verifying default admin account are meaningless security features. They do very little to secure the website in concrete ways. Forget the security industry, even hackers have moved on from these tricks.
Some of the hardening features had us puzzled. If we chose to disable plugin and theme editor, how would we update our plugins and themes when vulnerabilities are discovered? Also Sucuri stores PHP files in the uploads folder, so cutting off all external access means that they won’t be able to access their own files. Perhaps there is a rule that allows them that access, but this is not clear to an end-user at all.
There is a password management feature, but the accompanying warning would scare off most people from ever using it:“Select users from the list in order to change their passwords, terminate their sessions and email them a password reset link. Please be aware that the plugin will change the passwords before sending the emails, meaning that if your web server is unable to send emails, your users will be locked out of the site.”
What’s missing from Jetpack and Sucuri
Our biggest issue with Sucuri is the fact that the malware scanner doesn’t work. We would have expected that it would detect some of the malware, considering how widely Sucuri is used on websites. But it didn’t detect anything! Unforgivable in our opinion.
Jetpack doesn’t have a firewall nor malware cleaning, automated or otherwise. It does half the job of finding the malware that is already on the website, but nothing to remove it or protect it. Nowhere close to adequate, in terms of security.
Sucuri vs Jetpack: Pricing
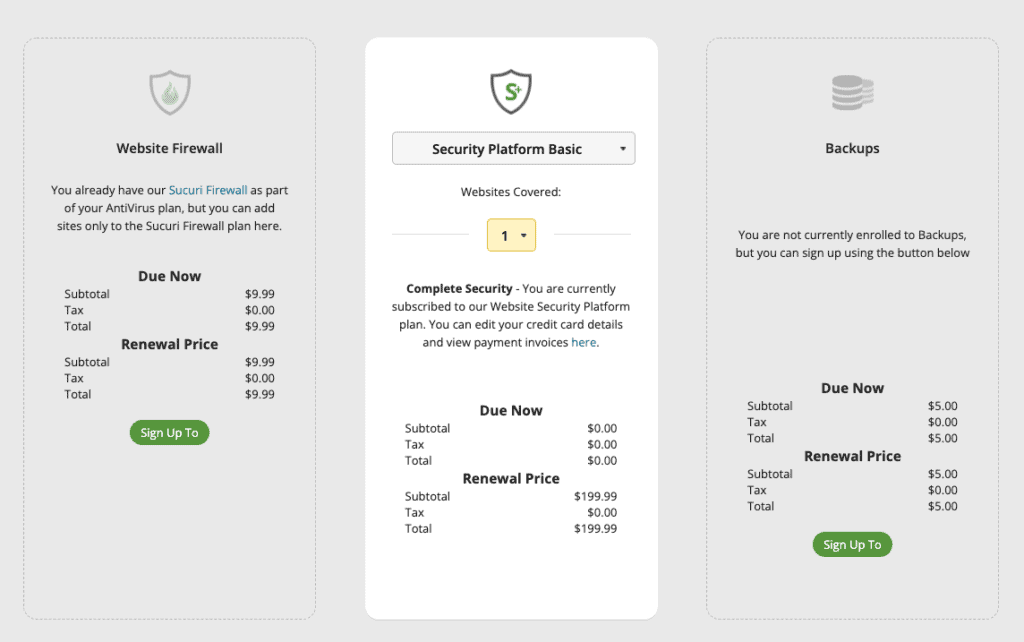
Sucuri’s lowest premium plan clocks in at $199.99 a year per site. It is a good deal for the unlimited malware removal requests you can have. The firewall is also decent, but the scanner is terrible. It is not entirely value for money. Jetpack is not a good security plugin for the $300 price tag.
If we were going to pay $300 for a security plugin, we would ask a lot of that plugin: an unerring malware scanner, a firewall and cleaning options. Jetpack has none of these. It helped with identifying some of the malware, detecting some of the vulnerabilities, and having average brute force protection.
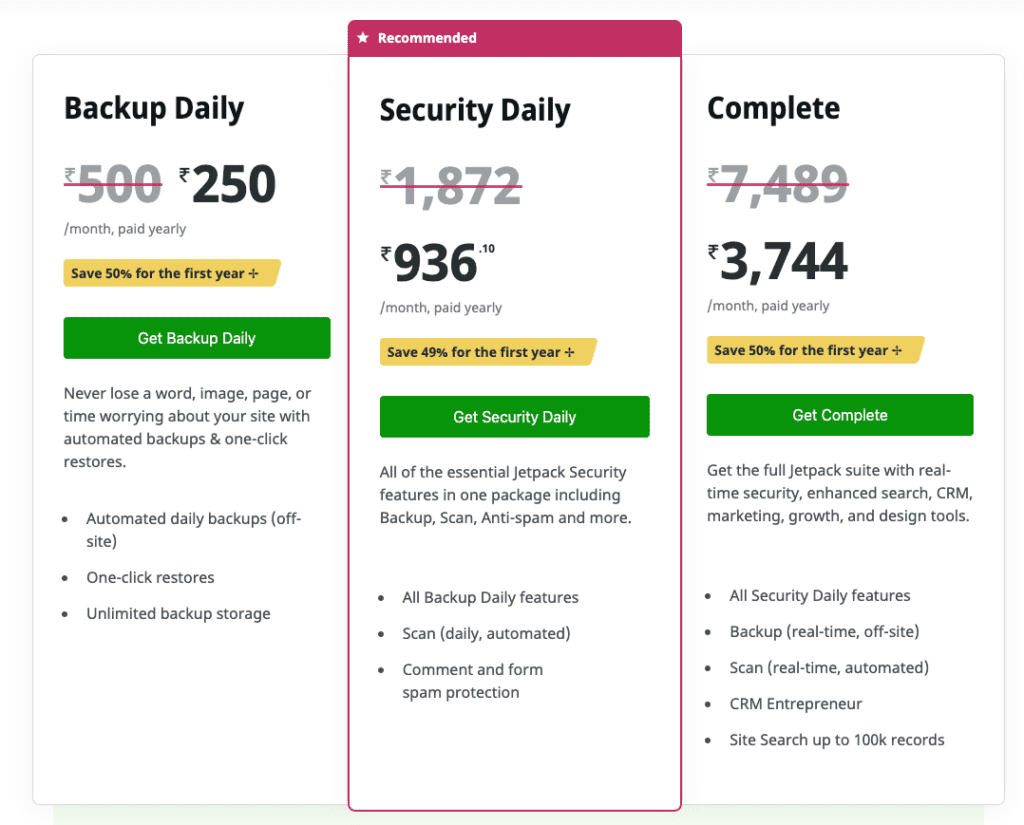
Unlimited malware removal is a huge positive in Sucuri’s favour. The response time was great, there was a post-hack checklist shared with us, and all the malware was cleaned. But—and this is a big but—the malware scanner was a complete failure. We were so disappointed that it didn’t detect a flicker of malware. And yet, the team cleaned it all up. If Sucuri could bring some of the manual malware cleaning energy to the scanner, it would become a formidable plugin. Till then though, not so much.
Better alternative to Jetpack and Sucuri: MalCare
In this article, we’ve presented all our findings from intensive testing sessions. Neither Jetpack nor Sucuri works effectively to protect WordPress websites from hackers and their malware. If you have read this far into the article, you know that security is non-negotiable. So investing in a solid and reliable security plugin is the way to go forward.
The best WordPress security plugin available today is MalCare. MalCare has a top-notch malware scanner, automated malware cleaning, and an advanced firewall to protect your website from attacks.
In a feature-to-feature comparison between all the other security plugins, MalCare also works out to be significantly more economical. Against Jetpack’s hefty $300, MalCare’s $150 plan is a much better deal for many more features. Similarly for Sucuri, MalCare’s $99 plan is vastly better than their $199.99 Basic Platform plan.
Recommended read: Alternatives to Sucuri
Conclusion
A security plugin is an essential part of your administrative toolkit. It is one of those things that should require minimum intervention and work out of the box. MalCare has the best security, without the unnecessary noise that most other plugins bring to the table. It is a worthwhile investment to protect your revenue from hackers.
Did this article help? Drop us a line and let us know. We would love to hear from you!
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








