How to Protect Your Site from WordPress Brute Force Attacks
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

Brute force attacks can overwhelm sites, even before an attack is actually successful. These attacks on WordPress sites hammer the login page, attempting to break through to your site dashboard.
If you see a lot of requests on for wp-login.php or wp-admin, you may well be under a brute force attack. Install a WordPress firewall with bot protection to deflect the bad requests, and safeguard your site.
Many site admin sees their server resources depleting rapidly, their sites becoming unresponsive or even outright crashing—causing actual users to be locked out. The issue is that you can feel helpless as brute force bots send request after request to your site.
But you aren’t helpless. If you see several unsuccessful login attempts for a single user, maybe coming in from multiple IPs, you’re in the right place.
In this article, we will break down what a WordPress brute force attack looks like, and how to protect your site from them.
TL;DR: Double up the defence of your site with MalCare’s bot protection and integrated login protection. MalCare prevents brute force bots from attacking your site with a powerful WordPress firewall with bot protection. As a plug, it also limits login attempts so real users are never locked out.
What is WordPress brute force attack?
WordPress brute force attacks are attempts to gain unauthorized access to your wp-admin by trying out various combinations of usernames and passwords. Hackers have developed bots to continuously bombard a login page with credentials on a trial-and-error basis.

Often, the bots try a series of passwords from a dictionary and therefore are also known as dictionary attacks or password-guessing attacks. The attacks can be configured to come from different IP addresses, and thus circumvent basic security measures. There are other types of brute force attacks, which we will cover later in the article.
The goal of a brute force attack is to get access to your wp-admin, and then most typically install malware on your site. Additionally, the effects of an attack are immediately visible. Most sites have limited server resources, which get used up rapidly, and often a site under attack will crash completely.
Fortunately, there is a lot you can do to prevent brute force attacks in WordPress. Here is a list of WordPress brute force protection steps that will block most attacks, and mitigate the worst effects for good measure.
1. Block bad bots
The best defence against WordPress brute force attacks is to have an intelligent firewall with integrated bot protection.
Brute force attacks are almost always carried out by bots. Hackers create bots that try out a series of username and password combinations on a login page till it finds a match. The bots use lists of credentials, either gotten from data breaches, or from dictionaries—which is why unique and strong passwords are so important.
On top of that, over 25% of all website traffic is bots, so there are a lot of security systems that have bot protection in place. However, there is an important distinction to be made here: all bots aren’t bad. There are good ones like other search engine crawlers and uptime monitoring bots. You want those to have access to your site, so it is important to get bot protection that intelligently blocks out only bad bots, like MalCare.

There are other bot protection plugins too, like All in One, but it blocks all bots by default, including Googlebot, which will adversely affect SEO.
2. Limit login attempts
The another effective way to stop WordPress brute force attacks is to limit login attempts. If an incorrect password is entered into the login page too many times, the account is temporarily blocked. This blocks the brute force bot’s effectiveness, as it relies on the trial-and-error method to guess credentials in a short span of time. On top of that, since the bot cannot try out several thousand combinations, the requests are not sent to the server, and resources are not used up by the bot’s activity.
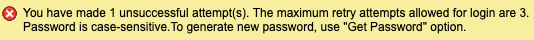
By default, WordPress allows unlimited login attempts, which is why it is susceptible to brute force attacks in the first place. With MalCare, brute force login protection is automatically activated. In fact, in the event a user has legitimately forgotten their password, they can solve a captcha to get past the block easily. Therefore, limiting login attempts keeps out brute force bots without adversely affecting real users.
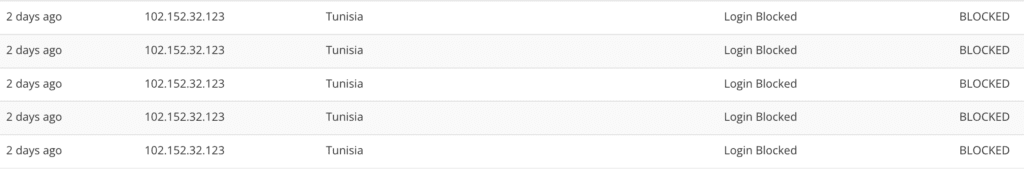
3. Install a web application firewall
Login protection is a defense against brute force attacks specifically, whereas a firewall is a defence against all kinds of WordPress attacks; including brute force ones.
Firewalls use rules to block out malicious traffic, and do a great deal to protect your website. Plus, firewalls mitigate one of the biggest issues with brute force attacks—the excessive load on server resources—by blocking out repeated bad requests.
Brute force attacks are often configured to attack from different IPs, and therefore can bypass most firewalls. However, with MalCare’s firewall, your website becomes a part of global IP protection. The firewall learns which IPs are malicious from behavior recorded from over 100,000 sites and proactively blocks traffic from them. These measures significantly reduce the amount of bad traffic to your website in the first place, before the bot even has a chance to brute force your site’s login page.
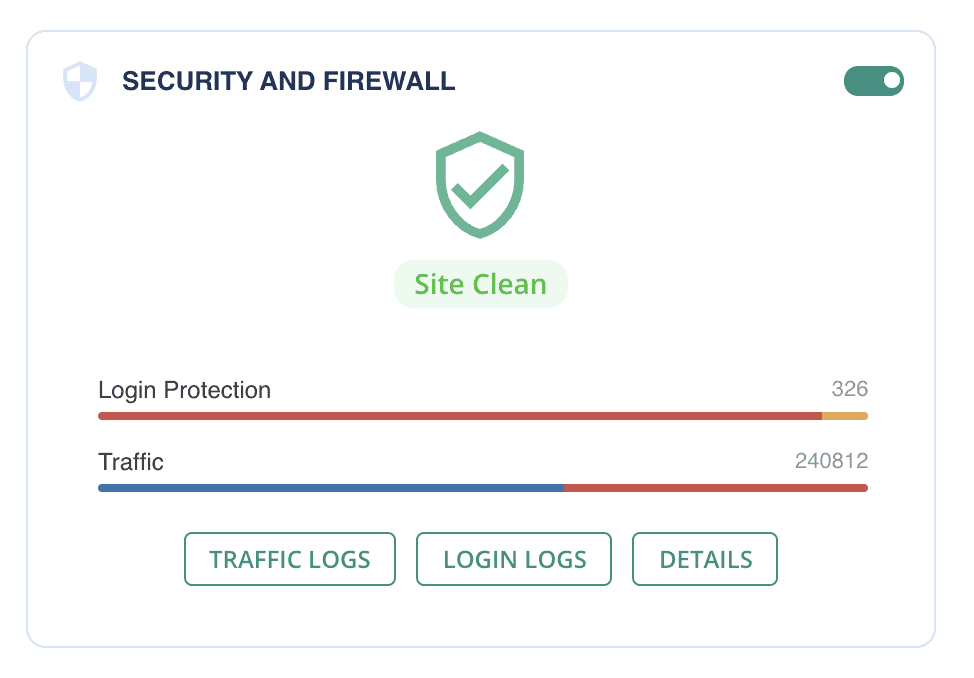
4. Add two-factor authentication to WordPress
Usernames and passwords can be guessed, so two-factor authentication—or indeed multi-factor authentication—has emerged as a way to have dynamic elements to authenticate users. With two-factor authentication, a real-time login token like an OTP or QR code is shared with the user’s device. It has limited validity, usually of about 10-15 minutes, and can only authenticate a user for that session.
The additional token is difficult to crack in addition to the username and password. Therefore, it adds another layer of security to the login page. You can install a plugin like WP 2FA to add two-factor authentication to your site easily.
5. Use strong and unique passwords
The biggest flaw in security is the user themselves, and by extension the passwords they set. Passwords are the biggest vulnerability in any security system because of the (understandable) human tendency to set easy-to-remember passwords and reuse them across different accounts. These are actually two separate and distinct problems with passwords.
First off, never reuse passwords across different accounts. A lot of brute force bots use stolen passwords from data breaches to attack login pages. Secondly, as you can imagine, a password like ‘password’ is terribly easy to guess. Use a minimum of 12 characters of gibberish, or even better use a passphrase as a strong password.
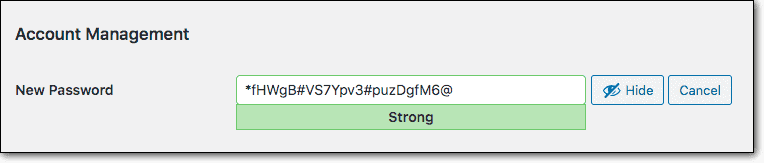
We recommend using a password manager like LastPass or 1Password to avoid reusing passwords, and to generate strong ones as needed. In case you suspect an account has been compromised, you can force reset all passwords from the hardening section of the MalCare dashboard. There are plenty of ways to secure your site with strong passwords and good password policies.
6. Disable XML-RPC in WordPress
The XML-RPC file is another way to authenticate users. In other words, it is an alternative way to gain access to your admin dashboard, so is also susceptible to brute force attacks. It is a largely deprecated file and not in active use by many plugins or themes. It continues to be included in WordPress for backward compatibility and is therefore relatively safe to disable. We strongly recommend you disable XML-RPC on your WordPress site.
7. Review user accounts regularly
Dormant accounts are often targets for hackers because the chances are that the users won’t notice if their accounts are hijacked. Additionally, dormant accounts have the same passwords for long periods of time, making them easier to brute force.
Therefore, review user accounts regularly, and remove any that aren’t in active use. For extra credit, ensure that each account has the bare minimum user privileges needed to manage their account. It is foolhardy to make everyone an admin, for instance.
8. Consider geoblocking in WordPress
If you see a lot of bot traffic from one location, you can consider blocking the entire country. However, we advise discretion when using geoblocking. It is useful only if you don’t anticipate any legitimate users from that location at all. Additionally, be warned that it can keep out good bots from that region. For instance, Googlebot can operate from any of its server locations in the world, and you definitely want Googlebot to access your site.
While there are many ways to block countries on WordPress websites, we strongly recommend using a powerful firewall instead.
9. Disable directory browsing
By default, most WordPress core folders and files are openly accessible via a browser. For instance, you can type yourwebsite.com/wp-includes into your browser URL bar, and the entire contents of the folder will be immediately visible.
Although directory browsing itself isn’t a vulnerability, it can reveal information about the site that can be in turn used to exploit vulnerabilities. The /wp-content folder has plugins and themes, and if a hacker can see which ones are installed and their version numbers, they can potentially find and exploit vulnerabilities. This is a less popular type of brute force attack called directory brute force.
Therefore, it makes sense to disable directory browsing altogether, as a safeguard.
Things you should avoid doing
There is a ton of well-intentioned but poor security advice out there. So, in addition to our list of things to do, we’re listing what not to do just as well.
- Password protect wp-admin directory: Don’t do this at all. It appears in practically every brute force prevention article. Password protecting the wp-admin directory will break AJAX for non-logged in users, by restricting access to the admin-ajax.php file.
AJAX is often used to power the dynamic aspects of websites. Suppose there is a search bar on your site. If a visitor uses it to search through products, only the search results will reload, not the entire website. This is a huge resource saver, and makes the user experience of websites significantly faster and better.
You will also see a lot of workarounds for excluding the admin-ajax.php file, but they don’t always work seamlessly. The bottom line is that the effort that the workarounds entails does not reflect a commensurate amount of security. Therefore it is a huge step for little additional benefit. - Changing your wp-login URL: You see this advice often in WordPress security or hardening articles. However, we strongly recommend against changing the login URL because it is next to impossible to recover if it gets lost.
- Avoid the use of admin as a username: Since brute force bots are effectively trying to guess username and password combinations, there is some value in avoiding obvious usernames like admin. WordPress doesn’t allow you to change usernames from the dashboard, so you will need to install a plugin to do so.
However, this measure is of limited value, and we advise against spending too much time and effort here. There are other ways to recover usernames from certain types of sites, like membership ones. The effort needed to have unique usernames for members, enforce the policy, and then deal with the inevitable fallout when people forget their unique usernames is not worth the limited beneficial effect.
Impact of a brute force attack in WordPress
There are two ways to think about the effects of a brute force attack. Firstly, what happens during an attack, and secondly what happens if an attack is successful.
Generally, with attacks, the first question doesn’t often arise, because there is little to no impact to the website, as it experiences an attack. The consequences rear their heads once an attack is successful. However, that is not the case with a brute force attack.
What happens when your site is being brute forced?
You will see an immediate impact on server resources. Because the attack is bombarding your login page with requests, the server has to respond to each one. Therefore you will see all the effects of increased server usage on your website: a slower website, some users being unable to log in, downtime, inaccessibility, and so on. Web hosts are also quick to restrict server usage that is going through the roof, because this will impact their metrics, especially if you are using shared hosting.
What happens if the brute force attack is successful?
If the attack is successful, you can reasonably expect to see malware or defacement of some kind. There are several reasons why hackers want access to your website, and none of them are good.
If that wasn’t bad enough, your website can become part of a botnet, and be used to attack other websites without your consent. This can have major ramifications because other security systems will flag your website as malicious if it is part of a botnet.
How to deal with a hacked WordPress website
If a brute force attack has been successful, you should assume the worst: your website has been compromised. Therefore, your first priority is to secure your website. Here are the major steps you should take to contain the damage:
- Force log out all users and change all passwords
- Scan your website for malware immediately
Once you are certain that your site is clean of malware, implement the prevention measures listed above. We strongly recommend installing MalCare, which takes care of login protection and bot protection, while also packing in a malware scanner, cleaner, and an advanced firewall for good measure. With MalCare installed, you can rest assured that your site is safe from WordPress attacks.
Is your site susceptible to brute force attacks?
Yes, all systems are vulnerable to brute force attacks. Because of the way they work, brute force attacks can be launched against any system with a login page. WordPress websites are no different.
The popularity of WordPress makes it a target for hackers. Firstly, this is because much of the Internet is powered by WordPress, and secondly because certain aspects of WordPress are well known. In an example particularly relevant to brute force attacks, WordPress doesn’t restrict incorrect login attempts. You can correct this with MalCare’s limit login feature, as we talked about in the measures section.
On top of this, many site owners tend to use usernames and passwords that are easy to remember. Common ones include admin as a username and password1234 or 12345678 set as a password.
These factors make your website susceptible to brute force attacks. That’s why a strong understanding of WordPress security is important.
Types of brute force attacks
Brute force attacks are different from other types of threats and attacks, like social engineering attacks or XSS attacks. Social engineering attacks, like phishing, manipulate people into sharing their credentials, by posing as a trusted entity, whereas XSS attacks exploit vulnerabilities on the website. Brute force attacks rely on weak or stolen credentials to succeed.
You’ll see a few flavours of brute force attacks in the wild. They all follow the same pattern of trial-and-error, but the credentials they try or the mechanism they use can vary. Here are a few of the most common types of brute force attacks:
- Simple attacks: Simple brute force attacks use logic to guess credentials based on their knowledge of the user, like pet names or birthdays gotten from social media sites for example.
- Credential stuffing: This type of attack uses data obtained from breaches, operating under the assumption that users tend to use the same usernames and passwords across multiple systems.
- Dictionary attack: As the name implies, these bots use dictionary files for passwords. This can be an actual dictionary, or one specially created for password guessing.
- Rainbow table attacks: Similar in concept to a dictionary attack, a rainbow table is a special kind of dictionary list. Instead of a list of passwords, a rainbow table contains a list of hashed passwords instead.
- Password spraying: This type of attack is logically a reverse brute force attack. In typical brute force attacks, a particular username is the target and the guessing game is played with the password. Conversely, with password spraying, a list of passwords is tried against multiple usernames to find a potential match. It is a more distributed attack, as compared to a targeted one.
As a site admin, you may not need to know the differentiators between different types of brute force attacks. However, these terms are often used interchangeably, so it helps to have an understanding of the underlying mechanisms.
Other good security practices
Preventing brute force attacks in WordPress is an admirable goal, but it is only a part of website security. Here are a few of our top recommendations to keep your site safe and free of malware:
- Install a security plugin with a good malware scanner and cleaner
- Keep everything updated
- Invest in daily backups
For a full list of recommendations, check out our ultimate security guide.
Conclusion
Brute force attacks can debilitate a website, even if they are not successful. The best way to deal with this potential threat is to install a firewall that has integrated bot protection, like MalCare.
Even if a brute force attack has been successful, MalCare will help you detect malware quickly and remove it. As is the case with all infections, quick action limits damage significantly.
FAQs
What is a brute force attack in WordPress?
A brute force attack in WordPress is when a hacker tries to gain access to the site’s wp-admin by trying to guess the login credentials of a legitimate user account. Brute force attacks make use of bots to try hundreds, thousands, and sometimes even millions of passwords on a wp-login page in an attempt to guess the right one.
Brute force attacks are not only dangerous for a site in case they are successful, but also have a huge impact on site performance. The attack uses up server resources and can even crash the site on occasion.
How to protect your WordPress site from brute force attacks?
The most effective way to protect your site from brute force attacks is to have bot protection and to limit login attempts. By default, WordPress allows unlimited login attempts, so you can use MalCare to protect your site from brute force attacks. In addition to login protection, MalCare includes bot protection and an advanced firewall, both of which help protect your site, and mitigate the ill effects of a brute force attack.
Share it:
You may also like

Top 9 MainWP Alternatives: Manage Multiple Sites Easily
Managing multiple WordPress sites can be a daunting task. Keeping track of updates and security patches, and maintaining backups can quickly become overwhelming. This is where solutions like MainWP come…
How to Fix the Google Blacklist Warning from Your Website
Google blacklist is a colloquial term used to describe big red warnings visible when visiting websites. There are a few flavours, depending on various factors, but they all mean that…

MalCare Stands Strong Against WP Activity Log Premium SQL Injection Vulnerability
A significant SQL injection vulnerability was identified in the WP Activity Log Premium plugin, a popular tool for tracking user activity on WordPress sites. An SQLi vulnerability poses a serious…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








