WordPress Malvertising Campaign: How to Protect Your Website Against It
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

Imagine you wake up one peaceful morning knowing your website is functioning fine. But when you open up your site, you see that your website is displaying unwanted pop-ups that don’t close! The content of your ads are changed to sell drugs or promote adult websites! That is, so-called, WordPress malvertising!
You can be sure your advertising network has been hacked, and as a result, your website is a victim of malvertising! Hackers use malvertising campaigns to display unwanted content, redirect visitors to malicious sites, and distribute malware.
You might feel helpless as the hack is at the network level through no fault of your own. But it’s you who will suffer the consequences such as adwords account suspension, drastic loss of traffic and revenue!
Luckily, you don’t have to rely on your advertising network to fix it! There are measures you can take to protect your website from hackers right away.
In this article, you’ll learn how malvertising works and the steps you can take to recover from it. You’ll also learn how to prevent it from happening again so that you don’t have to face this ordeal again.
TL;DR: You can protect yourself from malvertising attacks by installing a sturdy firewall. Activate MalCare on your infected site and it will scan and quickly identify any malware present on your site. Fix it in under a few minutes and restore your website to normal.
[lwptoc skipHeadingLevel=”h1,h3,h4,h5,h6″]
To learn how to remedy a malvertising attack or prevent one, you need to first understand what it is and how it works.
What Is Malvertising in WordPress?
Malvertising is a kind of attack in which hackers inject malicious code into online advertisements. This means the website itself is not hacked, but the advertisements have a malware infection.
Hackers launch Malvertisement attacks through the online advertising network where they submit malicious ads. If the network is unable to detect the malware in the ad, they approve these ads. Next, your website displays the ad.
The target of this scheme is the visitor of the website. When a visitor views the page with an infected ad or clicks on the ad, it activates the malvertising scheme. It could install malware or adware on the visitor’s computer or force the user’s browser to redirect to a malicious site. We’ve discussed the impact in detail later.
Let’s take a deeper look into how hackers carry out this WordPress infection.
How Does Malvertising Work?
To understand the WordPress hacking technique called malvertising, let’s take a step back to see how online advertisements work.
How Online Advertisements Work
An online advertisement network brings together advertisers (who want to pay to display their ads) and publishers (who want to earn revenue from displaying those ads on their website).
The publisher signs up to the network (such as Google AdSense, Media.net, Propeller Ads or PopAds) and submits the website for review. Once the network approves, the publisher creates ad spaces on the website.
This ad space is available for sale/purchase through a complex system of exchanges, representatives, and intermediaries. Advertisers bid in real time for ad spaces to show ads to a particular type of user.
These ads include custom Javascript code that runs in a user’s browser.
Here’s where things get tricky. The coding in ads is such that the exact content the user sees depends on many things:
- Who they are
- What they like such as their preferences
- Where they are located
- What kind of device they’re using
So the Javascript code is highly customized which makes it difficult for the ad networks and publishers to review every version of the ad and determine what is malicious.
Now we can see how malvertisement works.
How Malvertisement Works
Hackers take advantage of the complexity of this system and submit ads that have malicious codes disguised and hidden.
By passing the reviews due to the security loopholes, they are successful in getting their ad approved, they bid for ad space. They target big and small websites within the advertising network to display their ads.
The website on which they bought ad space would start displaying unwanted advertisements and pop-up ads.
Lastly, when a visitor views the page with an infected ad or clicks on the ad, it executes the malicious code.
Unfortunately, the repercussions of such an attack fall greatly on website owners and the visitors.
Impact Of Malvertising On WordPress Websites
As we just mentioned, malvertising has detrimental effects on both your visitors and your website. What are these effects? Let’s take a look:
Effects On Website Visitors
Malvertising campaigns affect your website’s visitors in the following ways:
Unwanted Content
The ads will display unwanted content to visitors. This includes adult content, illegal drugs, counterfeit products and the like.Infected Computers
Some ads initiate a download on its own. By simply viewing the page with an infected ad, the hacker could force a download of malicious software on to the visitor’s computer. Hackers can then wreak havoc for the user by hijacking the computer, stealing personal data, installing ransomware, and the like.Malicious Redirects
It can redirect visitors to malicious websites which can also force an automatic download. Visitors could also be directed to a site that looks similar to the site they are visiting but it’s actually a malicious website operated by the hacker. These are called phishing sites and are designed to steal user data such as credit card information.
Effects On Your Website
A malvertising attack affects website owners in the following ways:
Slow Website
It can slow down the speed and performance of your website because malicious advertisements usually use up more resources. This means the WordPress malware infection would use web server resources that otherwise run your website at optimum speed.Reduced Traffic
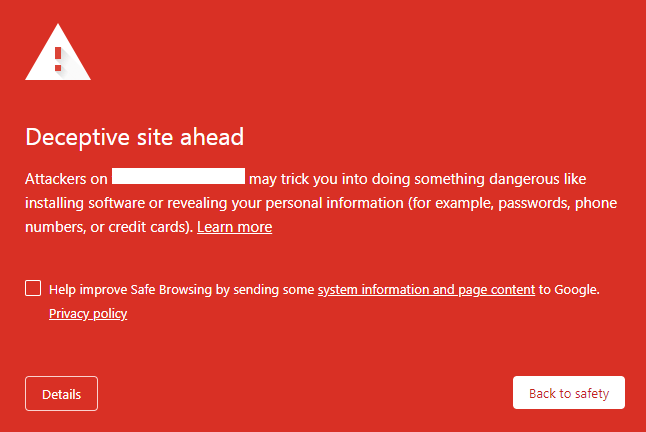
As the ads redirect your visitors to other websites, your traffic will drop and your bounce rate will increase. Once visitors will realize you have a hacked site and they are at risk, they most likely won’t visit your site again.Google Blacklist
Google has a number of checks to find out if your website has malware. Once it detects malicious ads on your website, Google will blacklist your site to prevent its users from accessing your website. Your visitors will see a deceptive site ahead warning like so:
WebHost Suspension
Similarly, if your web hosting provider detects malware on your website, they will immediately suspend your account and take your website offline. They do this to protect their own infrastructure and other websites hosted on their server.Loss of Revenue
Websites that have been victims of malvertising have experienced a severe loss in revenue. After your site is on the blacklist, your traffic will fall drastically. This means your ads will not generate revenue. If you’re an eCommerce store, you’d lose paying customers as well!Sites have even faced blacklisting by the ad network itself even though the malware originated from the network! Getting back on the network is a long-drawn process. In the meantime, you stand to lose a significant chunk of revenue.
Needless to say, malware from a malvertisement attack needs a clean up promptly. We can tell you that contacting your advertising network would be a long-drawn process and would take the time to sort out the mess.
Ad networks serve ads from millions of advertisers. These ads are dynamic according to real-time bidding. Testing every ad that’s shown to a user becomes impossible.
Here’s what you can do to take matters into your own hands and clean up the attack:
Cleaning up a Malvertisement Attack
There are two ways you can clean up any kind of malware on your website – manually and using a plugin.
We’ve seen many clients who have tried to delete the malicious ads on their own only to see them reappear every time. The problem here is that hackers embedded malicious somewhere in your WordPress files. We discourage the manual method because:
- First, you need to access your hosting control panel and file manager. Next, you need to manually scan your WordPress files on your server.
- You may need to delete code from files such as the wp-config.php file which carries a huge risk. You may need to delete all the files that the hacker has created. Any slight mistake here could lead to a completely broken WordPress site.
- Next, it’s extremely hard to detect manually as they disguise it to look like regular code.
Instead, there are WordPress security tools to clean up your site promptly without the hassle. We strongly recommend choosing a web security plugin. But among these plugins, you also need to choose the right one.
How to Choose a Non-Vulnerable Plugin
Many plugins rely on outdated methods of finding malware. More often than not, the malware goes undetected and it shows your site is clean when it’s not. Most plugins also have a time-consuming process of removing malware. But in such an attack, time is of the essence. The longer you take to fix it, the worse the repercussions become.
To avoid these problems, we will use MalCare. It’s fast, reliable, and does a thorough job. Built on smart technology, the plugin can sniff out even the most complex and deeply hidden malware on your site. The biggest plus is that it has an instant cleaner. If you have a hacked site, you can clean it in a few minutes and get your website back to normal. Let’s take a look:
How to Use MalCare Plugin
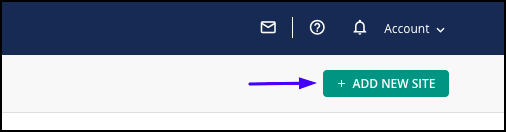
1. Install MalCare on your WordPress website and ‘Add your Site’ to the dashboard.
2. It will automatically begin scanning your WordPress website for malware. Once it detects a malware, you’ll see an alert like so:
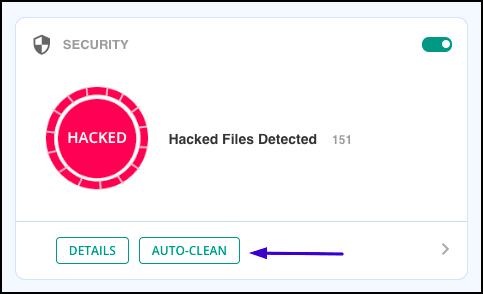
3. Next, click on ‘Auto-Clean’ and the plugin will begin to remove malware from your site.
That’s it. Your site is clean and you needn’t worry about malicious ads being displayed.
Before we leave you, we’ll take you through a few tips to prevent such attacks on your website.
Prevent Malvertising On Your WordPress Site
Protect your site against malvertising by taking the following measures:
Advertising Measures
- Review ad networks – Before signing up on advertising networks, inquire about their process. Check their ad delivery paths and the security practices. Ensure that the ad network vets the ads they display properly before they are passed onto your site.
- Dedicate Resources to Vet Ads – If you have the manpower, it’s best to dedicate a certain amount of time and resources to checking the ads on your site on a regular basis.
- Scan Images for Malware – Always scan image files for malicious code before you upload them to your site. You can do this by using a staging site which will not affect your live site. Upload the ad images here and run a malware scan on it. If it comes clean, you can upload it to your live site.
If you’ve opted for MalCare’s services, you can rest assured that your site is secured from malvertising. The robust firewall and intelligent malware scanner will seek out threats, block the execution of malicious code, and block requests coming from non-trusted sources.
Conclusion
Being a victim of a malvertising campaign can bear catastrophic consequences. Going through this ordeal once is bad enough, you would never want it to happen again.
Unfortunately, malvertising is only one kind of attack that can have such a devastating impact. Hackers are constantly on the prowl to find vulnerable WordPress sites to run all sorts of hacks.
We strongly recommend taking your own security measures to protect your WordPress website. Here are the top measures you should take:
- Always keep a reliable backup copy of your website. If your website is under attack, you can restore your site back to its previous state.
- Take measures to Harden your WordPress website against hackers.
- Install a trusted WordPress security plugin that will regularly scan your website and proactively block such attacks.
Once you’ve take these three steps, we’re confident your WordPress website is secure!
Category:
Share it:
You may also like

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…

MalCare Proactively Defends Against Icegram Express SQL Injection Vulnerability
MalCare’s recent data has revealed numerous attempts to exploit a newly found SQL injection vulnerability in the Icegram Express plugin. Attackers commonly use this sophisticated SQL injection technique to extract…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








