WordPress Phishing Hack: Fix and Protect Your Site
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.
You are here because your website has either been marked as a phishing site, sending out phishing emails to your visitors, or has a bunch of phishing pages on it—that you haven’t added.
But, why is any of this happening? Yours is not a phishing website!
If you are experiencing these symptoms, the chances are that your WordPress website has been hacked. More specifically, your site is a victim of the WordPress phishing hack.
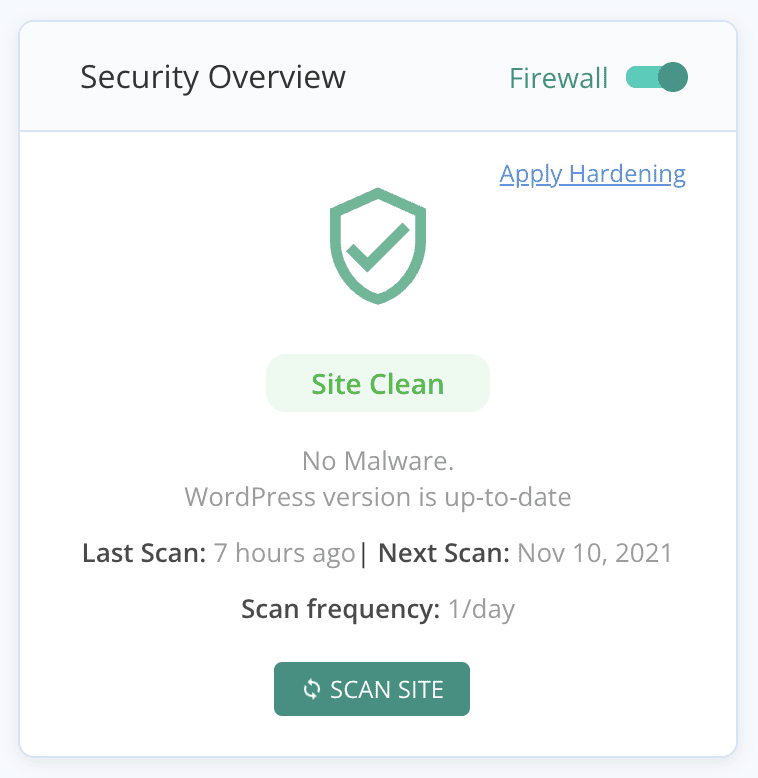
While there is an outside chance that this is a false alarm, the first thing you should do is scan your website for malware. If your website shows up clean, you can breathe a sigh of relief, and skip to the section on how to appeal the warning. If not, stay calm, we’ll tell you exactly how to remove phishing from your WordPress website.
TL;DR: Remove the malware responsible for the WordPress phishing hack from your site in minutes with MalCare. If your site has already gotten flagged by Google Safe Browsing, this is the first and more critical step to get your website back to its original state.
What is the WordPress phishing hack?
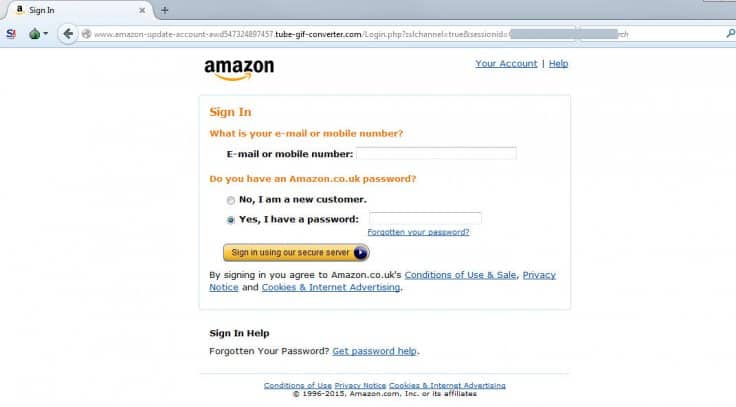
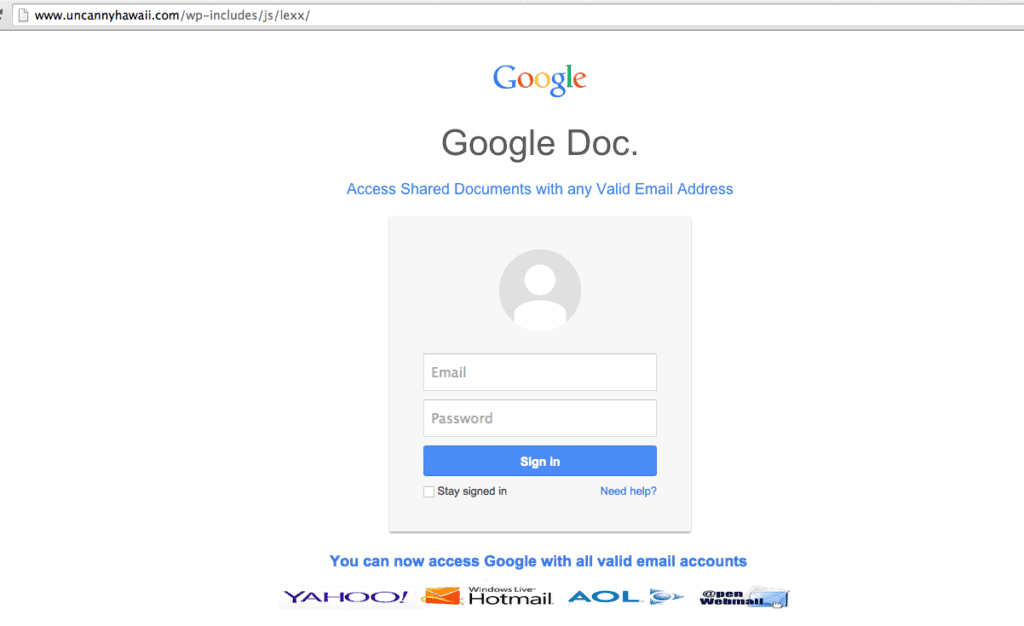
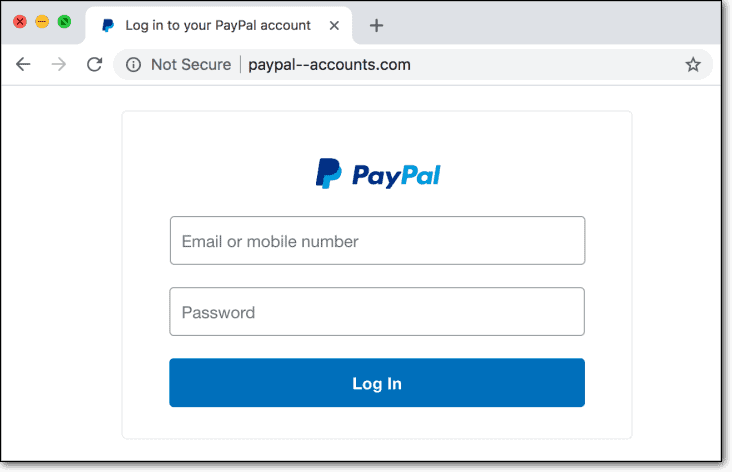
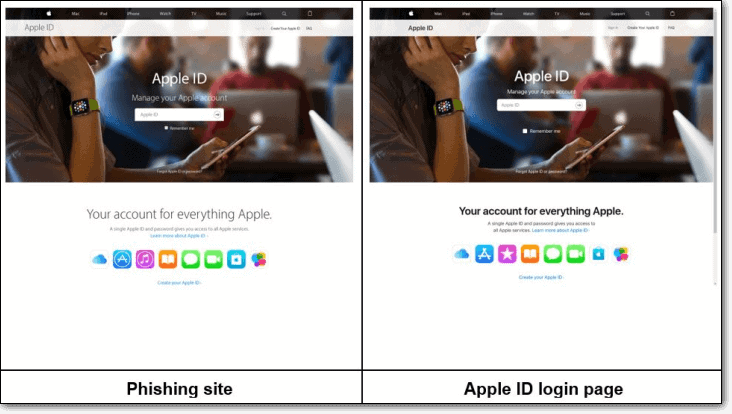
WordPress phishing hack is when hackers trick unsuspecting users into giving up their personal identity and financial data, using a WordPress site to pose as a legitimate brand that the user trusts. In this specific instance, the hackers are using your WordPress site to launch the attack. It is difficult to see the malware behind this attack, unless you scan your site thoroughly.
This means that there are official-looking pages on your website that may cause people to share private information.

Phishing attacks cost businesses billions of dollars every year. In 2022 alone, there were 4.7 million phishing attacks. Year on year, attacks are increasing at a rate of 150%.
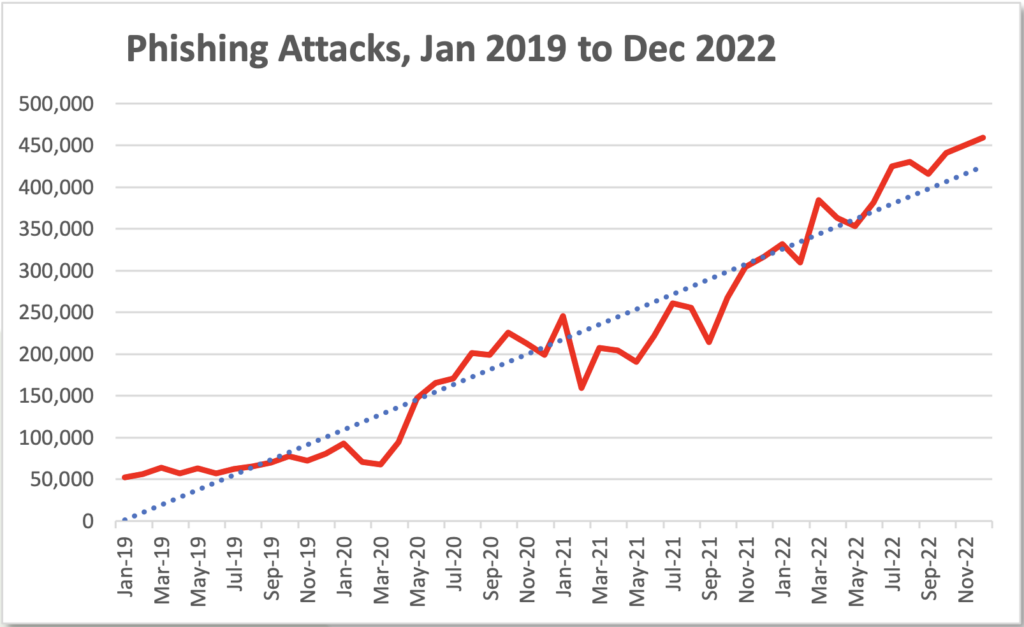
Image credit: APWG
A phishing attack is very bad for your WordPress website. Every minute that the malware remains on your website, you are incurring a loss. Either Google will flag your site and your SEO and traffic will take a hit, or you will lose visitors and customers because they will think your site is unsafe.
But just so we’re clear: removing malware manually is not a straightforward task and we don’t recommend it under any circumstance. A hacked WordPress website can have multiple infections, backdoors, and hidden fake admins due to malicious files like favicon_bdfk34.ico and many more. Trying to find and remove them all by yourself is a surefire way to wreck your site completely.
We strongly recommend you use a security plugin which removes phishing instantly from your website without further delay.
Step 1: Check your site for the WordPress phishing hack
The best way to find the malware on your site is to scan it immediately. Malware scanning is a definitive answer to whether or not your site is hacked. If you haven’t come across instances of phishing campaigns yourself, and you’ve seen Google’s browsing warnings like this site has been marked as a phishing site, you may be wondering if your website has really been compromised. Scanning is a sure-fire way to rule out the possibility.
You can also look for the following symptoms:
- Check Google Search Console > Security Issues for notices about deceptive content.
- Visit some of the flagged URLs from a different computer, on a different network or in incognito mode. Hackers can mask malware from website administrators to prolong infection.
- Check third-party inclusions on your website. Ad networks can sometimes serve ads that have phishing campaigns. As ads are typically cycled, you may have to refresh the website several times to check the ads being shown. Even if an ad has social engineering content—which has nothing to do with your website—your website could still be flagged as containing deceptive content.
- Unusual pages or posts on your website. Although this is a difficult way to find phishing pages, you may be able to spot unrelated pages in your sitemap or in site files.
- Favicons of known brands in site files. Because hackers often impersonate brands, they need to have build a page which can pass for an authentic brand login or payment portal. To do this effectively, hackers often use real brand logos—which you may be able to find on your site.
If Google Search Console flags issues, then you can be certain your website is a victim of the WordPress phishing hack, and can proceed to phishing removal.
Step 2: Remove the WordPress phishing hack
There are a couple of ways to remove phishing pages from your WordPress website. After you have scanned your site thoroughly, and have a malware diagnosis, it is time to suit up. We’ve listed a few ways to remove malware from your site, starting with the most effective, quickest, and therefore recommended option: using a security plugin.
Option 1. Use a security plugin [recommended]
The fastest way to get rid of phishing is to use a security plugin to remove it safely, without compromising your website any further. Then you can go about appealing the warning.
MalCare is a best-in-class WordPress security plugin, which not only detects the most devious and cunningly hidden malware on sites, but removes it instantly with one-click.
- Install MalCare on your site, and give it a few minutes to sync your site.
- The scanner will show up the results of hack.
- Upgrade to use the one-click removal feature.
And that’s all there is to it. You can even reach out to the support team of WordPress security experts to get professional assistance.
Option 2. Remove phishing malware manually
Alternatively, you can remove WordPress phishing hack manually. To be clear, this process involves digging through the code to find the pages and therefore malware. The phishing pages will not be easily visible in your database, but hidden in various system files and directories in your content management system.
Only experienced developers should attempt to remove phishing files, because there is a possibility that you might delete necessary code and cause irretrievable damage to the website. Take a backup of your site before making any changes, and please proceed cautiously with deleting the following pages:
We have detailed instructions on how deal with a hacked WordPress site manually; although we don’t recommend it. If anything goes wrong, you still have the infected website that you started with, and you can decide to opt for a one-click clean up instead.
Step 3: Prevent future phishing attacks
Malware finds its way into WordPress because of security vulnerabilities in plugin or theme code. Hackers exploit vulnerabilities to gain access, and insert their nefarious bits of code into your website. Quite often, website administrators aren’t even aware of these developments—until something goes wrong. And by then, significant damage and loss has already taken place.
The best way to stay on top of these security issues is to have a scanner checking your site daily. MalCare will ferret any malware, pinpoint backdoors, and alert you to vulnerabilities, all while protecting your site from attacks with a powerful firewall.
1. Install a security plugin
We cannot sufficiently stress the importance of installing a good security plugin for WordPress. You do not want to be caught on the back foot, after being informed by a visitor or your web host or Google that your website has problems.
MalCare is able to prevent malware from being installed in the first place and includes a strong firewall. If malware is detected on your website, it will be able to remove it without compromising your website further, and ensuring the content remains intact. And finally, MalCare has a highly reputed, expert manual removal service.
2. Remove backdoors
This critical step in prevention is tricky to execute well, because backdoors can be hidden in legitimate folders. What makes removal even more complex is that many of the functions are used by plugins for benign reasons. So deleting a function that may appear to be a backdoor can cause unintended consequences. We do not recommend doing this on your own, but using a WordPress security plugin like MalCare to do this.
3. Delete unauthorised users
Check your database to identify and remove unverified users. Be careful not to delete real users. Also change all admin passwords after you remove instances of phishing malware.
4. Keep your website updated
A simple, often overlooked method to ensure WordPress security is to keep your WordPress core and all installed plugins and themes updated. Updates include security patches that address vulnerabilities, among other things, and should be installed on priority.
If there are plugins or themes that you don’t actively use, disable or remove them.
5. Install an SSL certificate
Most web hosts include SSL certificates in their services. SSL certificates encrypt data that is sent back and forth between browsers and servers. It is very simple to set up and use, and is actually a requirement from Google to promote safe browsing and it will also remove site not secure warning on your site padlock.
6. Require strong login credentials
Easy to guess usernames and passwords are still one of the easiest ways for a hacker to gain unauthorized access to a website. Require all users to set strong passwords for their accounts.
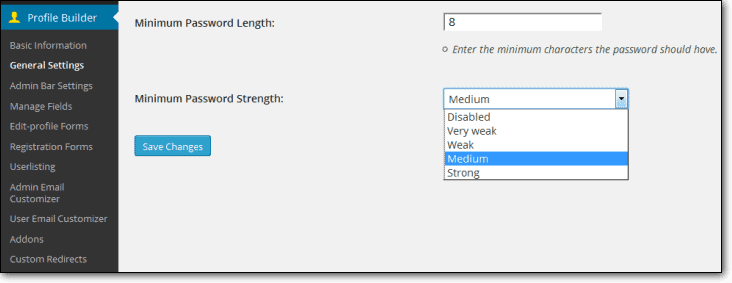
There is a lot you can, and should, do secure your website. Here is a complete guide to all the steps you can take to address vulnerabilities, learn what to look for, and even how to choose the right plugins and themes for your website that ensure your visitors and their data remains safe.
Step 4: Remove the “this site has been marked as a phishing site” warning
Once you have gotten rid of the malware causing the WordPress phishing hack in the first place, you can proceed to getting rid of the Google Safe Browsing notice.
We cannot stress this enough: it is vitally important to make 100% sure that phishing removal was successful. Otherwise, your request will be rejected and the process will just take even longer. As a failsafe, make sure to scan your site once more.
Here are the steps to remove the “this site has been marked as phishing site” warning:
- Go back to Google Search Console > Security Issues
- Check the I have fixed these issues box, and Request a review
- You will need to provide details of what actions you have taken to remove phishing
Please be aware that Google’s review process takes an average of 72 hours to complete. We have seen many instances of the process being stalled because of repeated follow-ups and emails. Please be patient, because the process is a manual one. While we understand it is an incredibly stressful and frustrating situation, impatience with Google will only work to your disadvantage.
Types of phishing attacks
Phishing itself is a type of social engineering attack, which essentially means that the attack relies on pretending to be someone else to be successful. Additionally, social engineering attacks rely on the victim giving up their information willingly, because they believe the request is legitimate.
WordPress phishing hack
The hacker has inserted official-looking pages into your functioning website to defraud people by pretending to be a brand. While this is bad enough, consider that you may have been the victim of a phishing attack to begin with, because…
Targeting website administrators
…sometimes, you are targeted for your admin login credentials, in order for hackers to gain access to the websites you manage.
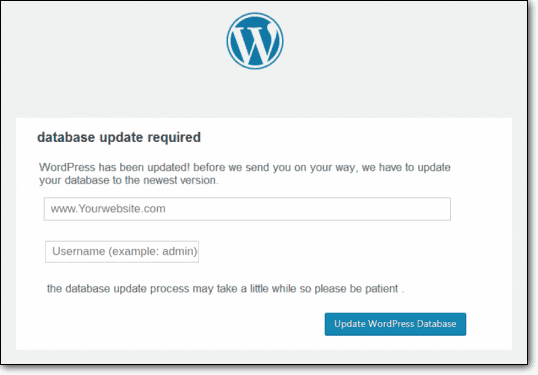
You may have received an email asking you to update your database “urgently”, otherwise something catastrophic will happen. The email will take you to a page which will resemble your web host or admin panel to update your database by entering your credentials.
Or perhaps, a scammer is posing as an irate customer, asking for a refund.
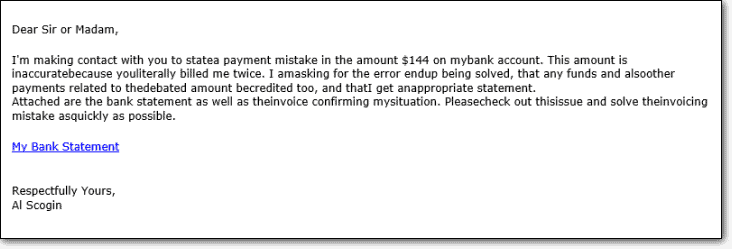
Even WordPress professionals with years of experience can sometimes be taken in by these emails, especially if they are managing multiple websites, and are handling operations of all those websites in different places.
Email phishing vs. WordPress phishing hack
There are various flavours of phishing: using emails, putting up malicious web pages, and most often, a combination of the two. Hackers insert pages on your website, which appear to be from a trusted organisation, in order to collect their login credentials. Generally, an unsuspecting user reaches this fraudulent page via an email, but they can also stumble upon it via a link or a redirect.
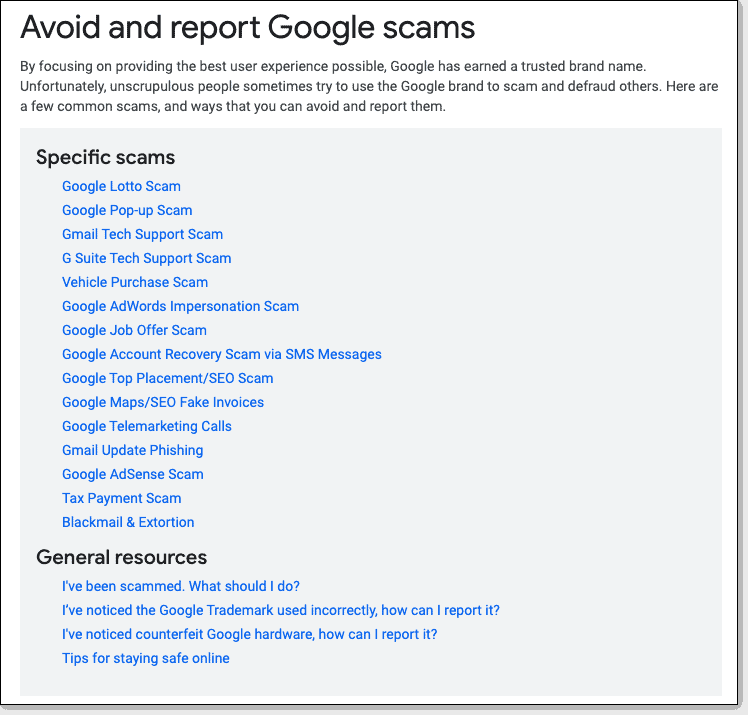
Fun fact: There is a special category of phishing attacks that sport the Google brand. Yup, the mighty Google isn’t free from this menace either. In fact, they have a dedicated support page for misleading pages perpetuated in their name.
Individual vs. spear phishing
Phishing attacks target large groups, and therefore one of the telltale signs of a phishing email is a lack of personalisation. This is not to say that all automated emails are suspect, but if an email is asking for sensitive data, like credit card details or login credentials, lack of personalisation can be a red flag.
Except when it happens to be a spear phishing attack. These types of attacks target specific individuals to give up their data.
Gathering login credentials may not present a big problem for individuals for certain websites, however it becomes a way to tap into the secure environment of that website (and its organisation) if the credentials happen to belong to an employee, for instance.
Also, we tend to use similar credentials across different websites and devices, and those accounts may contain sensitive information.
How are phishing attacks discovered?
The most unfortunate way to find out your website has the WordPress phishing hack is to land up on Google’s blacklist, and for your visitors to see one of the warning messages like this site has been marked as a phishing site; unless you have a strong security plugin installed.
Phishing websites are now being discovered through sophisticated AI. However, they are also manually reported to Google by individuals who experience them.
As we increasingly use devices and the Internet to carry out tasks in our daily lives, internet security is something of a byword now. Everyone receives tips and advice about keeping their data safe from every brand they interact with, right from the government to their bank to their grocery delivery app.
These messages contain practical ways of spotting a phishing attack a mile off: check the sender (for emails), check the URL (for websites), is there unnecessary pressure on someone to complete an action, etc.
Phishing attacks are also becoming more sophisticated, copying the language and the branding of trusted organisations more accurately. Therefore, in order to protect its users from being duped, Google is extra vigilant for hacked websites.
What are phishers after?
Well, what are any kind of hackers after? Information that they are not authorised to have, to be used in ways that they are not authorised to use. Unauthorised use may include theft—of identity, money or property—access to official databases and files, and so much more.
Look at the sectors most affected by phishing scams, and a clear pattern emerges:
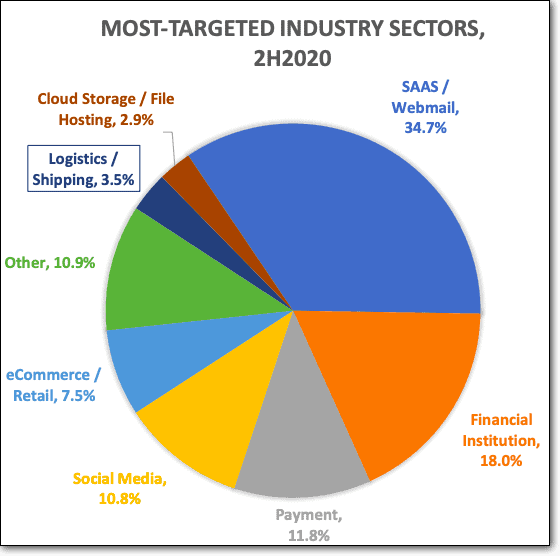
If your website stores any of the following information, you are a target for the WordPress phishing hack:
- Credit card details
- Bank account information
- Social security numbers
- Usernames and passwords
And the list goes on. As you can see from the list, any personal identification information is potentially useful for a hacker. Even email addresses lists are sold to unscrupulous businesses or spammers.
So what’s next?
Hopefully phishing removal was successful, and your website is back up and running, without any malware. We hope you found the information in this article helpful.
Before we go, we want to emphasize that our expertise comes from protecting 1000s of websites like yours every day, and all that expertise is packed into developing MalCare, our best-in-class security plugin. Try it out today, and be stress-free about your website security forever more.
FAQs
How to remove phishing from my website?
The best way to remove phishing campaigns from your website is to use a good security plugin. Manual phishing removal can be a long, complicated process, and prone to errors, because infected files are hidden in necessary and legitimate folders.
However, in case you feel confident about removing phishing attacks manually, we include a list of files to look for.
How to stop WordPress phishing attacks?
Prevent phishing from occurring by addressing vulnerabilities:
1. Install a strong security plugin with a good firewall
2. Search for and remove backdoors if any. If your website had malware before, there is a good chance that it still has backdoors
3. Remove unauthorised users
4. Update WordPress, all plugins and themes
5. Install an SSL certificate
6. Require strong login credentials
Why has my website been flagged as phishing?
Websites are flagged as phishing websites if Google detects it, or if someone has reported your website to have phishing content. Phishing campaigns can occur without the website administrator’s knowledge, and so a visitor may come across a phishing page before you do. Ads served by networks can also contain phishing campaigns.
How to check if my website has phishing?
To check if your website has phishing pages or not, log into Google Search Console, and check the Security Issues tab for reports. If you have not verified your website ownership on Google Search Console, you will have to do that first.
What is WordPress phishing hack?
Phishing hacks are a type of social engineering hacks that rely on users being misled into giving up their information voluntarily. Hackers pretend to be trusted brands and organisations, usually mimicking the language, design and content of websites in order to steal user information.
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








