Top WordPress Security Mistakes & How to Fix Them
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

WordPress Security Mistakes: Did you know that every minute some 90,978 hack attempts are made on WordPress websites? Once your site is hacked, hackers use it to execute all sorts of malicious activities like sending spam emails (read – phishing hack), attacking other websites, injecting spam links, redirecting visitors, etc.
This is why WordPress site owners like yourself have to take their security concerns seriously. There is no silver bullet you can use to solve all your security needs, but rather you need to do many things correctly. On the internet, there is innumerous advice on how to keep your site safe and secure. Some of them are conflicting advice and some are just outdated. Numerous opinions on what a site owner should do and shouldn’t bring confusion and amidst all that confusion, mistakes are inevitable.
Maintaining the security of a site is not an easy job especially for new site-owners who are prone to making mistakes that could leave them vulnerable to common hack attacks. Knowing the common security mistakes website owners make will help in avoiding them. And that’s why we came up with this list so that can stop making the mistakes that most WordPress site owners make.
Top WordPress Security Mistakes Site Owners Make:
We suggest running a WordPress security audit before taking any of the measures below –
1. Not Updating WordPress Core, Plugin & Themes
Keeping WordPress core and add-ons (i.e. themes and plugins) updated is a good security measure. Updating them doesn’t just add more features to the site but also helps patch vulnerabilities. Owing to the ecosystem WordPress works in, news about vulnerabilities spread very quickly and hacker tries to take advantage of the situation. If you don’t update your site which would’ve helped patch the vulnerability, your site will become easy to break into.
While some site owners don’t update their site because they are unaware of how updates are linked to security, others are afraid of incompatibility. WordPress websites can break after updating WordPress core, and its add-ons.
WordPress upgrades are designed to be compatible with all previous versions. Thus if your site is running version 4.1, you can still update it to the latest version, which is, say 4.9. But despite all precautions taken, each update bring news of website crash. Here’s an example from the latest WordPress version 4.9.6.
You may run into similar problems when updating WordPress add-ons, i.e. themes and plugins. Often incompatibility issue arises in themes and plugins because the developer was rushed into releasing a new update or perhaps the developer was incompetent. Plugins and themes have a really competitive market and in a bid to stand out from the rest, developers are pushed to add more and more new features in the shortest amount of time. Sometimes they are not given enough time to see if the version is compatible with every previous version of WordPress. And so if someone is using a very early WordPress version, and updates a plugin that works only with the latest few WordPress versions, his site breaks.
Concerns surrounding the compatibility issues between WordPress Core and an add-on may lead site owners to skip security updates.
How to fix this: A staging service could solve this problem. The process of creating a duplicate site for the purpose of testing the installation of the WordPress core and its add-ons is called Staging. Backup services like BlogVault or even web host providers like Kinsta offer staging environments. Check with your web host or backup services (if you are using one) to see if they have an option to stage a site. If not, then sign up with a service that allows you to stage a site.
Besides keeping your plugins, themes, and core updated, we strongly suggest that you keep your WordPress salts and security keys updated.
2. Using Poor Quality Add-ons
Not all WordPress plugins and themes are well made. Some ignore quality assurance checks, while others are developed by amateur programmers. It’s important that the users pay attention to what he’s choosing to use or buy. But unfortunately, many WordPress users don’t have any technical knowledge which renders them unequipped to find out how good the plugin or theme is.
How to fix this: To help such users, we have listed down a few characteristics that will help spot a good theme or plugin:
i. Make sure that you get the add-ons from a reputed source like the WordPress Plugin repository or popular seller like Elegant Themes, Themeforest, etc.
ii. Ensure the add-ons have a good rating on the WordPress repository and are reviewed by people who’ve used the theme/plugin on their site. A quick Google search will help you find the reviews.
iii. Verify that the plugin has been around a long time and has stood the test of time. Look for security updates and bug fixes listed in either the WordPress repository or the official website.
iv. And make sure that they are often updated and the recent update has been made less than 2 months ago.
3. Using Illegal Plugins & Themes
A lot of websites sell premium themes and plugin for free of cost. Using these free products can spell disaster because many of these WordPress add-ons have malware deliberately injected in them. Installed these illegal add-ons into your sites is like opening doors and inviting hackers to your site. Once an attacker manages to break into your site using the bad code in the theme/plugin you just installed, they’ll use your site to execute a number of malicious activities like sending spam emails or attacking other sites. Furthermore, having malware on your site deems it as compromised that causes hosting providers to suspend your account search engines like Google to blacklist your site, and suspend your AdWords account.
How to fix this: Buy original themes and plugins from popular marketplaces like ThemeForest, Elegant Themes, etc. During the sale period, one can buy themes and plugin at much lower prices. One can look for official websites of the theme or plugin of our choice.
4. Keeping Unused Plugins & Themes on Your Site
Keeping unused themes and plugins on the website provides an opportunity for hackers to infiltrate your site. Many site owners don’t update inactive add-ons because they are unaware of the security benefits. To them, updates bring new features, and since they are not using the plugin, they think they do not need the new features. If an update was released to patch a vulnerability, then your site remains at risk until you update it.
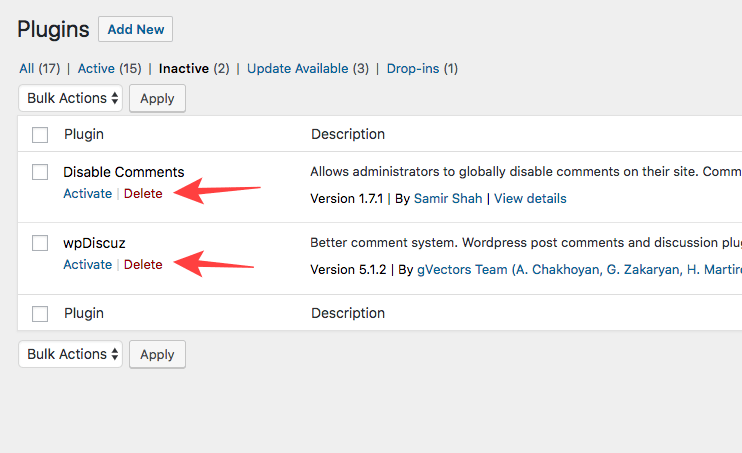
How to fix this: The only solution here is to get rid of the inactive WordPress themes and plugin. Here’s how:
Visit the ‘installed plugins’ page from the WordPress dashboard of your site.
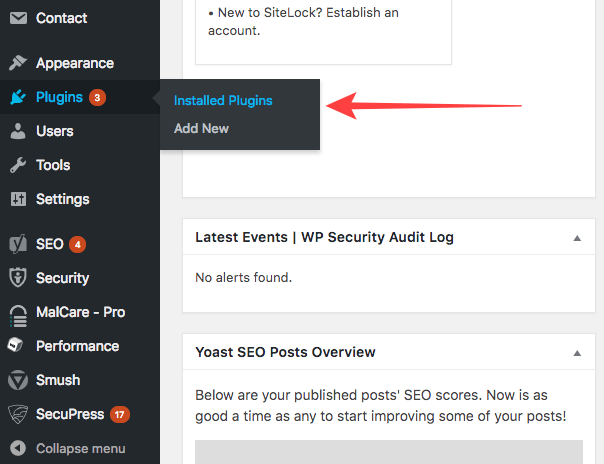
In the page, there is an option called ‘inactive.’ Select that.
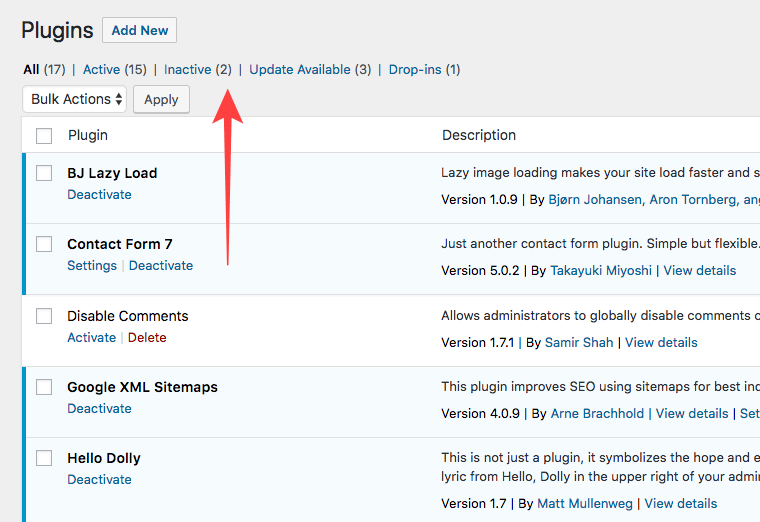
It’ll take to another page from where you can delete the inactive plugins. But before hitting the ‘inactive’ button, we suggest you make sure that you won’t require that particular plugin in near-future.
5. Using Bad Website Login Practices
Two common and yet very dangerous login practices are using easy to guess login credentials and not logging out when the site is not being used. Attackers program bots who try logging into your site using a combination of easy to remember username (like admin) and password (like password123) to hack a site. This peculiar method of hacking a site is called a brute force attack.
How to fix this: It’s recommended that you use a unique username and password (recommended read – WordPress login page protection guide). One downside here is that unique credentials are hard to remember. Therefore you must maintain a document carrying these credentials. And make sure that the document is encrypted to prevent unauthorized access.
6. Giving Every User Admin Access
Making every uses an admin is a bad idea especially for websites where there are a large number of users whom the site owner doesn’t know personally. WordPress allows site owners to assign the following roles to users – Administrator, Editor, Author, Contributor, Subscriber, SEO Manager, SEO Editor. It’s risky to make everyone Admin because it grants access to all areas of a site.
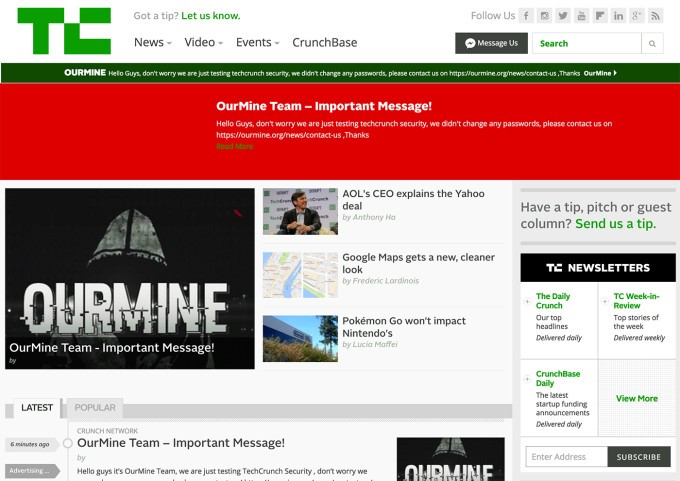
Giving users unrestricted access to the entire site leads to exploitation as seen in this case with TechCrunch (a popular tech site) who were hacked by OurMine (a hacker’s group). After getting access to a user account, OurMine were able to post on the site. Here’s a screenshot of the home page when readers woke up to after the TechCrunch was hacked:
How to fix this: Each user role on WordPress allows access to only specific areas of the site. Based on what you need a user to do on your site, you can assign these roles. Following this principle ensures that only people you trust can access the entire site. And if anything goes wrong, you know who’s accountable.
7. Not Taking Backups
Backups are your safety net. Not having one in place could land you in trouble when disaster strikes. If your site gets hacked and posts get deleted, you can easily restore your site back to normal using the backups. But using just any backup service is not advisable because many backup services are not efficient. For instances, many backup plugins store backups in your web servers. Some of them store backups in a single place. Your website server is not an ideal place to store backups because the server takes up the burden of backing on top of performing regular processes. It bogs down your site speed. Storing only one backup means if you lose that back, you’ll have no other backups to fall back on.
How to fix this: Before choosing a backup service, check the features to see where they store backups. If you can’t find proper information, shoot them a mail asking direct questions as to where they store backups and if they store it in multiple locations. To know more about how to choose reliable backups, check out this post.
8. Not Using a Security Service
Many websites owners, especially those who have small websites which draw in lower traffic think their site is insignificant and therefore won’t draw a hacker’s attention. But hackers today have plenty of reasons to attack a small website. They could be using it to store files or send spam mails among other things. Many hacking groups, in fact, prefer attacking small site because small websites are lax about their security and are therefore easier to hack. They launch massive brute force attacks where bots try to guess the correct username and credentials to break into a site. One of the most preferred hacking techniques involves taking advantage of vulnerable plugins and themes.
How to fix this: A standard security service offers essential security features like WordPress Firewall that helps prevent hackers from brute-forcing into your site.
Besides taking the above measures to fix your site, you can take a few more security measures. We strongly suggest following this guide – Secure Your WordPress Site With wp-config.php.
Whenever a vulnerability in the plugin or themes or even the core crops up, developers release a patch via an update. Therefore keeping all your themes, and plugins and WordPress core updated is a good security practice. MalCare – one of the best WordPress security plugins out there offers Site Management feature that allows you to update plugins, themes, and WordPress core from the MalCare dashboard. It’s especially helpful for people who have many websites to maintain. Logging into each website and updating themes, plugins, and core is a time-consuming job. Services like MalCare makes it easier for site owners to follow good security practices.
Besides firewall and site management, a security plugin also offers daily scanning services. If your website is malware-infected, the plugin will help you repair your hacked website. If you’d feel more comfortable with a team providing WordPress website maintenance services to you directly to fully manage your website security, WP Buffs is going to be a great option. They look after updates, security, website speed and ongoing edits regardless of whether you’re managing 1 website or 1000!
What Next?
Using a good WordPress security plugin is the first step towards building a secure website or keeping WordPress safe. Some more security measures that you can take include IP blocking, protecting the login page, and following this complete guide on WordPress security to learn further on how to secure your WordPress site.
If you have committed any of these mistakes in the past, hopefully, the post helped to see what you had been doing wrong and how to fix them. We welcome any questions that you may have regarding these WordPress security mistakes and their fixes. Kindly get in touch with us through our contact us page.
Category:
Share it:
You may also like
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…

MalCare Proactively Defends Against Icegram Express SQL Injection Vulnerability
MalCare’s recent data has revealed numerous attempts to exploit a newly found SQL injection vulnerability in the Icegram Express plugin. Attackers commonly use this sophisticated SQL injection technique to extract…

Atomic Security’s Deep WordPress Integration Helps Protect Against Core XSS Vulnerability
The recent WordPress core vulnerability is a critical one, primarily because of two reasons. Firstly, it affects the WordPress core itself, which means that every WordPress site is vulnerable to…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








