Beginner’s Guide to HTTP Basic Authentication
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

HTTP Basic Authentication is a commonly used method for improving your WordPress site’s security, assuring the safety of your content and efficiently controlling access. This straightforward but potent security procedure equips you with a robust tool to defend against unauthorized access and bolster general website security.
In this article, we’ll answer the questions:
- What is HTTP basic authentication?
- How do you use it?
- Is it secure?
We’ll also delve into the workings of HTTP Basic Authentication and emphasize its crucial role in protecting your digital assets. By the end of this, you’ll have a better comprehension of the mechanism and be ready to deal with any related challenges. You’ll also learn how to utilize this protocol to enhance your website’s security.
TL;DR: While HTTP Basic Authentication is a simple way to add a layer of security to your website, it’s not enough on its own. Your site needs a powerful security plugin like MalCare to fully protect your site from potential threats. MalCare regularly scans your website for malware, installs a reliable firewall, and helps you remove any malware in just one click.
What is HTTP basic authentication?
The Hypertext Transfer Protocol, better known as HTTP, is a foundational element for data communication on the web. This system functions much like a courier, delivering a myriad of data types, inclusive of HTML files, images, videos, etc., between the client, which is often a web browser, and a server.
When you type a URL into your browser and hit enter, your browser triggers an HTTP request to the server responsible for the resource you’re seeking. It’s the server’s job then to process this request before shipping back an HTTP response containing the data. This dataset is typically in HTML document form which your browser translates into the webpage you see.
HTTP Basic Authentication is a security checkpoint for web resources, ensuring only authenticated users can access them. It’s intrinsic to HTTP and operates by prompting for user credentials when a server responds with a 401 Unauthorized status code. Provided by the user, these credentials are checked for each subsequent request, helping keep your website secure.
Implementing HTTP authentication
HTTP Basic Authentication is often used by developers and website administrators for a straightforward and uncomplicated means to restrict access to specific web resources. It works well for small-scale applications, prototypes, or internal tools, where elaborate authentication mechanisms might be overkill. Furthermore, this method is great for a temporary or interim layer of security, allowing swift implementation without complex configuration.
In this section, we’ll talk about how to use HTTP Basic Authentication on an Apache server. The steps to using HTTP Basic Authentication an NGINX server is different.
Use HTTP Basic Authentication to secure your full site
- First log into your server using SSH with the command, replacing user_name and ipaddress with the credentials for the server:
ssh user_name@ipaddress. Enter your password when prompted.
- Then, verify if a file named .htpasswd already exists using the command:
ls -a.- If the file doesn’t already exist, execute the following command to generate a .htpasswd file:
htpasswd -c .htpasswd user_name Should the file already exist, simply omit the -c parameter and run htpasswd .htpasswd user_name to add a new user.
- When you add a new user, the password will be securely encrypted and stored within the .htpasswd file.
- Once you’ve exited the file, run the pwd command in the directory. Make a note of the full path, as you will need it in the next step.
- Navigate to the .htaccess file situated in the public_html folder and add the following lines:

AuthType basic
AuthName "Protected Site"
AuthUserFile /full_path_to/.htpasswd
Require valid-userIn the above code, replace ‘full_path_to’ with the path to your .htpasswd file.
- Once you’re done, save changes and exit SSH.
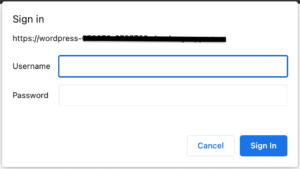
- Open a browser and open your site URL. Check if a pop-up box appears asking for a username and password. HTTP basic authentication is now enabled on your site.
Use HTTP basic authentication to secure a directory
. Directories serve as organizational units, grouping files and resources together based on their functionalities. Some examples of a directory are: wp-admin, wp-content, and wp-includes.
Each of these folders can also have a .htaccess file of its own, which overrides the settings of the .htaccess file in the parent directory. Therefore, you can use HTTP basic authentication to protect each directory by editing the .htaccess file within each targeted directory. The steps are the same as in the previous section, although we recommend changing the AuthName accordingly.
Use HTTP basic authentication to lock a single file
This method is particularly valuable when the file contains proprietary information, confidential data, or is a sensitive document that should be accessible only to a select group of individuals. By requiring authentication, you mitigate the risk of unauthorized access and maintain tighter control over who can view or download the protected file, enhancing overall data protection within your web environment.
You can protect a single file by creating or editing the .htaccess file in the directory that contains the file to add the following code:
<Files filename>
AuthType basic
AuthName "Protected File"
AuthUserFile /full_path_to/.htpasswd
Require valid-user
</Files>
Replace filename with the file you want to protect. You can add multiple filenames here to protect more than one file, with each file separated by the pipe (|) character.
Is HTTP basic authentication secure?
HTTP basic authentication stands as a rudimentary yet polarizing approach to bolstering web security. While its simplicity is appealing, a comprehensive evaluation reveals a lot of limitations.
- Very basic security: HTTP basic authentication provides a fundamental layer of security, serving as a straightforward gatekeeper to restricted areas of a website or application. Its implementation involves minimal complexity, making it an accessible option for quickly adding a modicum of protection.
- The credentials aren’t confidential: One of the key drawbacks lies in the fact that the transmitted credentials are not encrypted, rendering them susceptible to interception by malicious actors. This vulnerability makes it imperative to utilize HTTP basic authentication in conjunction with HTTPS, ensuring the encryption of data in transit and bolstering the security of user credentials.
- Persistent login: An inherent limitation of HTTP basic authentication is its lack of a built-in logout mechanism. Users remain logged in until they close their browser, which can compromise security if a shared or public computer is used.
- Vulnerability to brute force attacks: This authentication method is susceptible to brute force attacks, where hackers systematically attempt various username and password combinations until they gain access.
- Server-side credential storage: A crucial consideration is the secure storage of user credentials on the server side. Proper encryption and storage practices are essential to prevent unauthorized access to stored passwords, ensuring that user data remains well protected.
While HTTP basic authentication offers a first line of defense, its limitations underscore the importance of carefully evaluating its implementation against the specific security requirements of a given application or website. Its simplicity can only provide initial protection.
For a higher level of security use security protocols like good password security and a WordPress security plugin like MalCare. Amidst things like a great scanner and malware removal, MalCare also offers top-notch protection against bots with a powerful firewall.
What are some alternatives to authenticate users on your site?
Apart from HTTP basic authentication, WordPress offers a range of alternative methods to authenticate users and enhance the security of specific pages, posts, or even products within the WooCommerce ecosystem. These methods provide diverse options to control access and protect sensitive content.
- WordPress built-In password protection: WordPress comes equipped with a native password protection feature that allows you to require passwords for accessing individual pages, posts, and even WooCommerce products. This straightforward method ensures that only users who possess the correct password can view the protected content. This approach is particularly useful when you need to limit access to specific pieces of information without implementing complex solutions.
- Password protection plugins: In addition to WordPress’s native functionality, there are dedicated plugins designed to offer various levels of control and customization when it comes to password protection.
- Passster: Passster is a versatile plugin that goes beyond basic password protection. It enables you to implement more advanced features, such as time-limited access, IP-based restrictions, and conditional logic. This granularity allows you to tailor access rules according to specific user segments or usage scenarios.
- Password Protect: The Password Protect plugin focuses on providing a simple and efficient way to protect content with passwords. It offers options to customize password forms, set global passwords, and manage access across multiple pages and posts. This plugin streamlines the process for site administrators seeking quick and effective access control.
What are some must-have security measures to protect your WordPress site?
There is no magic wand that keeps your site secure. You have to incorporate multiple layers of security to protect your site.
- Utilize a security plugin: A dedicated security plugin, such as MalCare provides real-time monitoring, malware scanning, and firewall protection. These tools act as vigilant guardians, swiftly detecting and mitigating threats before they compromise your site.
- Deploy an anti-spam plugin: Combat unwanted spam and malicious content by integrating an anti-spam plugin like Akismet. This solution filters out harmful comments and safeguards your site’s user engagement.
- Regular security scans: Routinely scan your website for vulnerabilities and malware. Scheduled scans with your chosen security plugin can swiftly identify and neutralize potential risks, ensuring your site remains resilient against attacks.
- Keep everything updated: Regular updates address security vulnerabilities and enhance performance, reducing the risk of exploitation by malicious actors. However, they can be incompatible with other plugins on your site or have bugs. The safest way to update your plugins and themes is to use a staging site to test the update.
- Implement two-factor authentication (2FA): Bolster user authentication with 2FA. This method requires an additional verification step beyond passwords, providing an extra layer of defense against unauthorized access.
- Employ SSL encryption: Secure your site with an SSL certificate, encrypting data transmitted between users and your server. This measure safeguards sensitive information and enhances user trust.
- Enforce strong passwords: Encourage robust password practices for all user accounts. Encourage a combination of uppercase and lowercase letters, numbers, and symbols to create formidable barriers against unauthorized entry.
- Select a reliable web host: Choose a reputable and secure web hosting provider. A reliable host employs robust server-side security measures and actively monitors for potential threats.
- Take regular backups: Implement a rigorous backup regimen to preserve your website’s data and content. Scheduled backups, stored in secure off-site locations, act as a failsafe, enabling you to restore your site swiftly in the event of a security breach or data loss. BlogVault does it all and more, in just a few clicks.
- Stay informed and educated: Keep abreast of the latest security trends and practices in the WordPress ecosystem. Regularly educate yourself and your team about emerging threats and preventive measures to maintain a proactive stance against potential risks.
- Limit user privileges: Assign user roles with the least privileges necessary. Restricting access to critical areas and functionalities reduces the potential impact of unauthorized activities.
- Regularly monitor and audit: Conduct routine security audits to identify vulnerabilities and areas for improvement. Monitoring your site’s traffic and activities helps detect and respond to suspicious behavior promptly.
- Educate your users: Educate your site’s users about security best practices, such as creating strong passwords, recognizing phishing attempts, and safeguarding their own accounts.
Final thoughts
It’s important to acknowledge that HTTP basic authentication, while valuable in its simplicity, isn’t a robust solution. Its basic nature means it will not protect against every security threat.
For true protection, we recommend using MalCare, a best-in-class security plugin for WordPress sites. MalCare has an amazing firewall with formidable bot protection that can help protect your website from security breaches. Together, they create a powerful defense strategy that safeguards your site effectively.
FAQs
What is HTTP basic authentication?
HTTP basic authentication is a simple method used to secure web resources by requiring users to provide a username and password when accessing a protected area of a website or application. It’s a basic form of authentication that prompts users to enter their credentials before granting access to specific content or functionalities.
How secure is HTTP basic authentication?
HTTP basic authentication provides a basic level of security by requiring credentials for access. However, it has limitations: credentials are sent in a way that can be intercepted if not using HTTPS, and it lacks advanced security features like token-based authentication. It’s recommended to use HTTPS in conjunction with HTTP basic authentication to mitigate these limitations.
How do I check HTTP basic authentication?
To check if a website or resource is using HTTP basic authentication, you can try accessing the URL. If it’s protected, your web browser will prompt you to enter a username and password. Alternatively, you can inspect the HTTP headers of the server response to look for an Authorization header, which indicates the use of HTTP basic authentication.
Where are the credentials stored in HTTP basic authentication?
In HTTP basic authentication, the credentials (username and password) are stored on the server side. In Apache servers, these credentials are stored in the .htpasswd file. When a user attempts to access a protected resource, the server checks the credentials provided by the user against those stored in a secure manner on the server. The server uses these credentials to authenticate the user and determine whether they should be granted access to the requested content. It’s important to note that while the credentials themselves are stored on the server, they are transmitted by the client (user’s browser) in an encoded format as part of the HTTP request headers. This is why it’s crucial to use HTTPS in conjunction with HTTP basic authentication to encrypt the transmission of these credentials and enhance overall security.
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








