How To Prevent SQL Injections? (Complete Guide)
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.
Are you concerned about SQL injection attacks on your website? If you are reading this, you might already know the consequences of the attack. In this post, you will learn the easy ways to prevent SQL injections.
SQL injections can enable a hacker to hijack your WordPress site and access control of it. From there, they can redirect your traffic, steal confidential data, injecting spam links, manipulate search results with Japanese characters and display ads for illegal products. This kind of attack can cause irreparable damage to your site and your business.
Luckily, SQL injections are preventable if you take the right security measures. In this guide, we address SQL injections and discuss in depth the effective measures to prevent them and safeguard your WordPress website.
TL;DR: You can prevent SQL injections on your WordPress site by using a reliable security plugin. Install MalCare and the plugin will automatically scan and defend your site against such attacks.
[lwptoc skipHeadingLevel=”h1,h3,h4,h5,h6″ skipHeadingText=”Final Thoughts”]
What Are SQL Injection Attacks?
All WordPress sites usually have areas of input that allow a visitor to enter information. This could be a site search bar, a contact form, or a login form.
In a contact form, a visitor would enter their data such as name, phone number and email and submit it to your site.
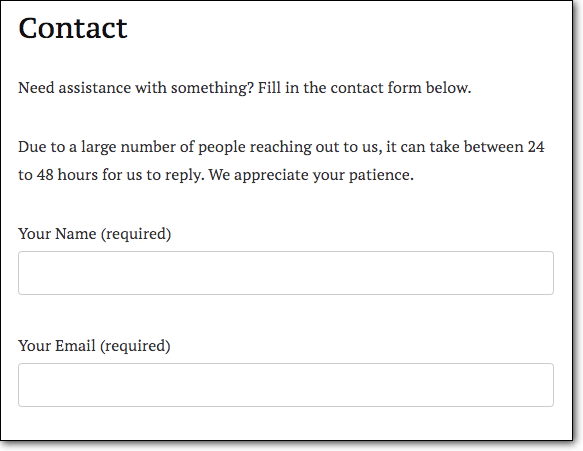
This data is sent to your website’s MySQL database. It is processed and stored here.
Now, these input fields require proper configurations to ensure the data is verified and sanitized before it enters your database. For example, a contact form vulnerability is, that it should only accept letters and numbers. It should ideally not accept symbols. Now, if your site accepts any data through this form, hacker can take advantage and insert malicious SQL query like:
txtUserId = getRequestString("UserId");
txtSQL = "SELECT * FROM Users WHERE UserId = " + txtUserId;
Once the script is stored in your database, hackers run it to gain control of your website. They can then proceed to exploit SQL injections, break into your site, and carry out malicious activities. They can start defrauding customers, redirecting visitors to phishing sites, and the like.
So, if your website doesn’t sanitize the data from these input fields, it means it has an SQL injection vulnerability.
How Does An SQL Attack Work?
Hackers target websites that have weak security measures or vulnerabilities present that makes it easy for them to break in. In our experience, plugins and themes often develop vulnerabilities and hackers are well aware of this. They prowl the Internet constantly in search of sites using vulnerable plugins and themes.
To explain this, we’ll use an example scenario. Say Mr. A is using a plugin ‘Contact Form’ to power a form on the Contact Page of his website. Let’s assume that an SQL injection vulnerability was found in this plugin in Version 2.4 and the developers fixed it and released an updated version 2.4.1.
Upon release, the developers reveal the reason for the update making the security flaw public knowledge. This means hackers know there’s a security flaw present in version 2.4 of the Contact Form plugin.
Now, Mr.X delays installing the update for a few weeks because there simply isn’t time to run the update. This is where things go wrong.
Once hackers find out about vulnerabilities, they run programs or use vulnerability scanners that will crawl through the internet and find websites using a particular version of a plugin/theme.
In this case, they’ll look for websites using Contact Form 2.4. Once they find the site, they’ll know the exact web vulnerability which makes it much easier for them to hack. In this case, they’ll exploit the SQL injection flaw and break into your site.
Types of SQL Injections
Hackers use two types of SQL injections:
1. Classic SQL injection – When you visit a website, your browser (like Chrome or Mozilla) sends a HTTP request to the website’s server to display the content. The web server fetches the content from the site’s database and sends it back to your browser. That’s how you are able to view the front end of a website.
Now, your website’s database contains all sorts of data including confidential data such as customer details, payment information, and usernames and passwords. Your database should be configured to release only the front-end data. All other confidential data should be safeguarded. But if these application security checks aren’t in place, hackers take advantage.
In a Classic SQL injection attack, hackers send malicious requests to your database retreiving data to their browser. But they use query strings to request for sensitive information such as login credentials of your website.If you haven’t protected this information, it will be sent to the hacker. In this way, they can get their hands on your login details and break into your site. Attackers can also use prepared statements as a way of executing the same or similar database statements repeatedly with high efficiency.
2. Blind SQL injection – In this, the hacker injects malicious scripts through input fields on your website. Once it gets stored in your database, they execute it to do all sorts of damage like changing the content of your site or even deleting your entire database.In this case, they can use the malicious scripts to gain administrator privileges as well.
Both scenarios can have a devastating impact on your website and your business. Luckily, you can prevent such attacks by taking the right security and input validation measures on your website.
Steps For Preventing SQL Injection Attacks
To prevent SQL injection attacks, you need to carry out a security assessment of your website. Here are two types of measures you can take to prevent SQL attacks – some are easy ones and some are complex and technical.
Easy Preventive Measures
- Install a security plugin
- Only use trusted themes and plugins
- Delete any pirated software on your site
- Delete inactive themes and plugins
- Update your website regularly
Technical Preventive Measures
- Change the default database name
- Control field entries and data submissions
- Harden your WordPress website
Let’s get started.
Easy Preventive Measures Against SQL Injection Attacks
1. Install a security plugin
Activating a website security plugin is the first step you need to take to protect your website. WordPress security plugins will monitor your site and prevent hackers from breaking in.
There are plenty of plugins to choose from, but based on what it has to offer, we choose MalCare. The plugin will automatically put up a web application firewall to defend your site against attacks. Hack attempts are identified and blocked.
Next, the plugin’s security scanner will scan your site thoroughly every day. If there’s any suspicious behavior or malicious activity on your site, you’ll be alerted immediately. You can take action and fix your site instantly with MalCare before Google gets a chance to blacklist your site or your hosting provider decides to suspend your site.
2. Update your website regularly
As we mentioned in our SQL injection example earlier, when developers find security flaws in their software, they fix it and release a new version that carries the security patch. You need to update to the new version in order to remove the flaw from your site.
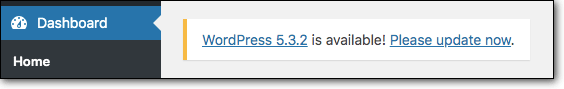
We suggest dedicating time once a week to update your WordPress core installation, themes, and plugins.
However, if you see that a security update is released, install the update immediately.
3. Only use trusted themes and plugins
WordPress is the most popular platform to build websites and that’s partly because of the plugins and themes that make it easy and affordable. But among the plethora of themes and plugins available, you need to choose carefully. Check the details of the plugin such as the number of active installs, the last updated date, and the version it’s been tested with.
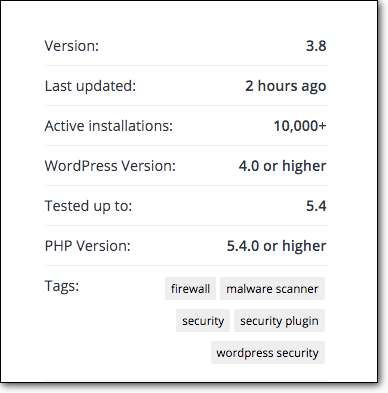
We recommend downloading them from the WordPress repository. For any other themes and plugins, you should do proper research to verify that they can be trusted. This is because some third-party themes and plugins can be maliciously crafted by hackers. It could also just be badly coded which opens it up to vulnerabilities.
4. Delete any pirated software on your site
Pirated or nulled themes and plugins are enticing. It gives you access to premium features for free. But unfortunately, these usually come with preloaded malware. Pirated software is an easy way for hackers to distribute their malware.
When you install it, the malware gets activated and infects your site. It’s best to stay away from such software.
5. Delete inactive themes and plugins
It’s common to install a plugin and completely forget about it for years. But this habit can expose your site to hackers. The more plugins and themes you have installed on your site, the more chances there are of vulnerabilities appearing and hackers taking advantage of them.
We suggest keeping only the plugins and themes you use. Delete the rest and make your site more secure. Also scan your existing themes and plugins regularly.
Technical Preventive Measures
These measures may require a bit more knowledge of the inner workings of WordPress. However, nowadays, there’s a plugin for everything. So you needn’t worry about the complexities involved in implementing these measures. We make it simple!
1. Change the default database table name
Your WordPress site is made up of files and a database. In your database, there are 11 tables by default. Each table houses various data and configurations. These tables are named with a prefix ‘wp_’. So the name of the tables can be wp_options, wp_users, wp_meta. You get the drift.
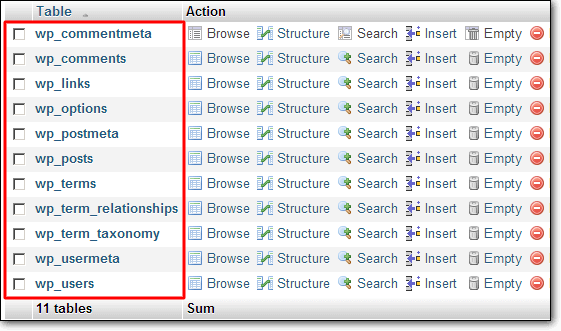
These names are the same across all WordPress sites and hackers know this. Hackers know which table stores what kind of data. When hackers insert malicious scripts on your website, they know where the script would be stored. Using a simple method, they can execute SQL commands to run malicious activities.
But if you change the name of the table, it can deter hackers from finding where the scripts are located. So when hacks try to inject SQL codes into your database tables, they won’t be able to figure out the table name.
You can do this by using a plugin like Change Table Prefix or Brozzme. Simply install one of them on your site and follow the steps.
You can also do this manually by editing your wp-config file. A word of caution – a slight misstep here could lead to database errors and site malfunctions. Take a backup before you proceed.
- Go to your hosting account > cPanel > File Manager.
- Here, access the public_html folder and right-click on wp-config file.
- Select Edit and find the following code
“$table_prefix = ‘wp_’;” - Replace it with –
“$table_prefix = ‘test_’;”
You can choose any prefix of your choice. Here we’ve chosen ‘test_’ as the new database name. Once done, hackers won’t be able to locate their SQL commands.
2. Control field entries and data submissions
You can configure all input fields on your website to accept only certain types of data. For example, a name field should allow only alpha entries (letters) because there’s no reason why numeric characters should be entered here. Similarly, a contact number field should accept only numerals.
You can use the sanitize_text_field() function that sanitizes the user input. This input validation makes sure that entries that are not correct or simply dangerous can be blocked.
3. Harden your WordPress website
This is one of the most important steps you can take towards protecting your WordPress site against SQL injection attacks. What is website hardening?
A WordPress website offers you many functions to help you run the site. However, the majority of people don’t use many of these functions. WordPress.org recommends disabling or removing some of them if you don’t use them. This will reduce the chances of attacks as there are lesser elements for hackers to try!
Some WordPress hardening measures are:
- Disabling the file editor
- Disabling plugin or theme installations
- Implementing 2-factor authentication
- Limiting login attempts
- Changing WordPress security keys and salts
- Blocking PHP execution in unknown folders
To implement these measures, you can use a plugin like MalCare that lets you do this with just a few clicks.
Or you can implement it manually by following our Guide on WordPress Hardening.
That brings us to the end of preventing SQL injection attacks. If you’ve implemented the measures we’ve discussed in this SQL injection cheat sheet, your site will be safe
Final Thoughts
Prevention really is better than cure. SQL injection attacks can cause unnecessary stress and severe financial burden.
Most of the measures we discussed today can be easily implemented with the use of plugins. So you needn’t be worried if you are not tech-savvy! You can still protect yourself!
Along with implementing these measures, we strongly suggest activating MalCare on your site. Its firewall will actively defend your website against attacks. It scans your site every day to check for hack attempts and malware on your site.
You can think of it as your website security guard that monitors your site and keeps the bad guys out. You can have peace of mind knowing your site is protected.
Category:
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








