How to Configure the Referrer-Policy HTTP Header in WordPress
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

Adjusting the Referrer-Policy HTTP header in WordPress is like adjusting the curtain for an open window: you can control how much passers-by can peek into your house while not disrupting your view to the outside. In this case, however, you are using the Referrer-Policy header to control how much information your site passes on to the sites it links to without affecting your web browsing experience.
Now, if you think configuring this is going to be like defusing a bomb in an action movie, think again. WordPress makes it so easy that anyone could do it—provided they know their way around a plugin. However, getting the Referrer-Policy header just right can help protect user privacy and secure data because, let’s face it, nobody wants their digital data on display for the whole internet to see.
Let’s walk through the steps to configure the Referrer-Policy HTTP header in WordPress, ensuring that your site is giving away only what it needs to, like a poker player with an ace up their sleeve.
TLDR: The Referrer-Policy HTTP header in WordPress fortifies your site’s privacy and security by controlling what referral information gets passed around. You can either use a plugin or edit the .htaccess file to configure it on your site. And for the full security package, add MalCare to your site.
What is the Referrer-Policy header in WordPress?
The Referrer-Policy header in WordPress is a crucial player in the web security game. It’s an HTTP response header that instructs browsers on how to handle referrer information—the data that tells a site where its visitors are coming from.
When a user clicks a link on your site, the header can signal the browser to limit the amount of referrer data sent along to the new page. This can range from sending the full URL to sending just the domain, or even sending nothing at all. The goal here is to balance the benefits that come from referrer data—such as analytics and personalized user experiences—with the need to protect user privacy and security. It’s like deciding how much to tell a stranger about where you live; maybe just the street name, or perhaps just the city—or maybe you’ll just smile politely and keep walking.
When setting up the Referrer-Policy header in WordPress, you’re given a menu of options, each dish serving up a different level of privacy. Here’s the rundown of the choices on the table:
- no-referrer: This one’s like going off the grid. The browser sends no referrer information with requests. It’s tight-lipped, telling nothing to anyone.
- no-referrer-when-downgrade: This is the default behavior if you don’t set a policy. It’s chatty but smart, sharing referrer info as long as the security level isn’t downgraded (like going from HTTPS to HTTP).
- origin: The minimalist, this one shares just the domain of your site. It’s like introducing yourself with just your first name at a party.
- origin-when-cross-origin: A bit of a split personality, this shares full paths for same-origin requests but only the domain for cross-origin ones. It’s like giving your full bio to friends but being brief with strangers.
- same-origin: The private type that only shares referrer info if the request stays on the same site. It’s like only sharing secrets with your best friend.
- strict-origin: This cautious fellow only sends the origin of the document as the referrer when the protocol security level stays the same (HTTPS→HTTPS) and is tight-lipped for all other scenarios, like a spy who only contacts you via secure lines.
- strict-origin-when-cross-origin: A combo of ‘strict-origin’ and ‘origin-when-cross-origin’, it sends full paths for same-origin but only sends the document’s origin to a different domain if the protocol remains secure. It’s savvy and cautious, like a chess player thinking two moves ahead.
- unsafe-url: The oversharer of the bunch, this option sends the full URL (with all its juicy details), regardless of the security context. It’s the equivalent of live-streaming your GPS location—not recommended if you’re trying to keep things under wraps.
Each of these policies offers a sliding scale of privacy, and the choice is a fine balance between functionality and the level of privacy you wish to maintain.
Check your WordPress site for Referrer-Policy configuration
Before you jump into configuring the Referrer-Policy header for your WordPress site, it’s wise to check if it’s already activated on your website. Head over to the Security Headers website, enter your website’s URL, and hit the Scan button. This quick check-up will lay out if the Referrer-Policy header is part of your site’s HTTP header configuration, along with other security features at work. It’s a smart move to avoid putting on two hats at once.
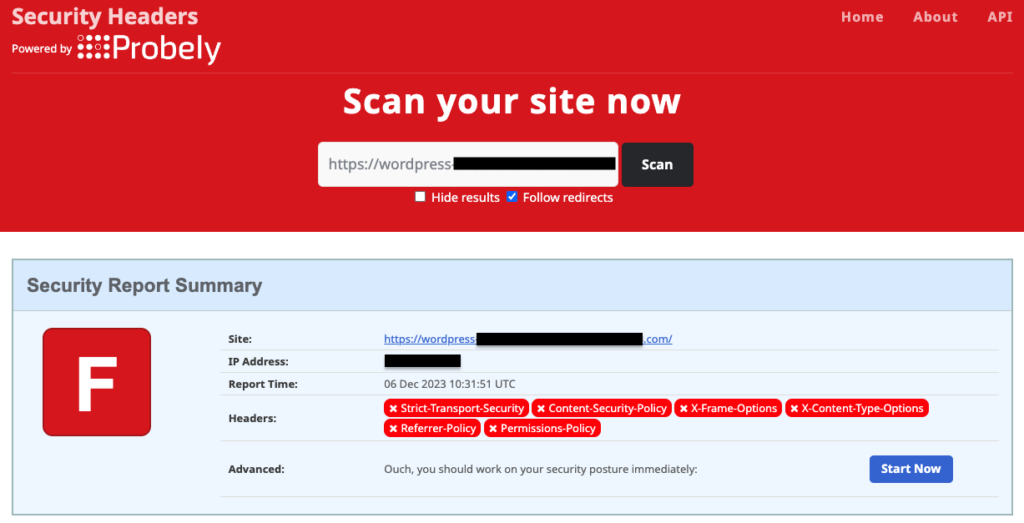
If the scan reveals no Referrer-Policy header on your WordPress stage, don’t sweat it! You can use a plugin, like HTTP Headers, which is tailor-made for the job, or get your hands a little dirty by editing the .htaccess file directly
1. Configure the Referrer-Policy header in WordPress using a plugin
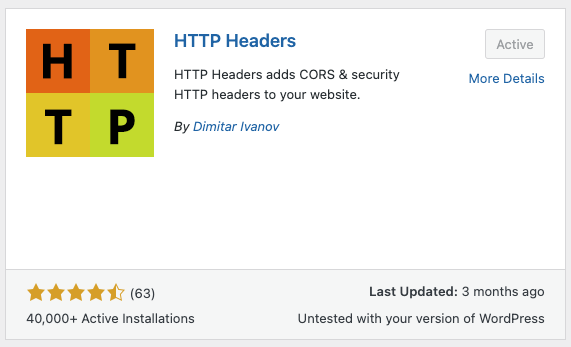
WordPress has both free and premium plugins to help you configure HTTP headers, like the crucial Referrer-Policy. Splurging on a premium tool such as AIOSEO is your call, but if you’re looking to keep your wallet happy, we recommend Dimitar Ivanov’s free HTTP Headers plugin.
Here are the steps to set up the Referrer-Policy header using the HTTP Headers plugin in WordPress:
1. Install and activate the HTTP Headers plugin: On your WordPress admin dashboard, hover over Plugins, and click on Add New Plugin. Search for HTTP Headers in the search bar. Found it? Great; install and activate it to gear up for action.
2. Locate the Referrer-Policy setting: Hover over Settings and click on HTTP Headers to land on its dashboard. Open the Security section to find the Referrer-Policy setting.
3. Configure the Referrer-Policy setting: By default, the Referrer-Policy is off since it’s not set up yet. Click on Edit and tick the On box to activate it. Choose your policy preference, save it with a click on Save Changes, and your mission is accomplished.

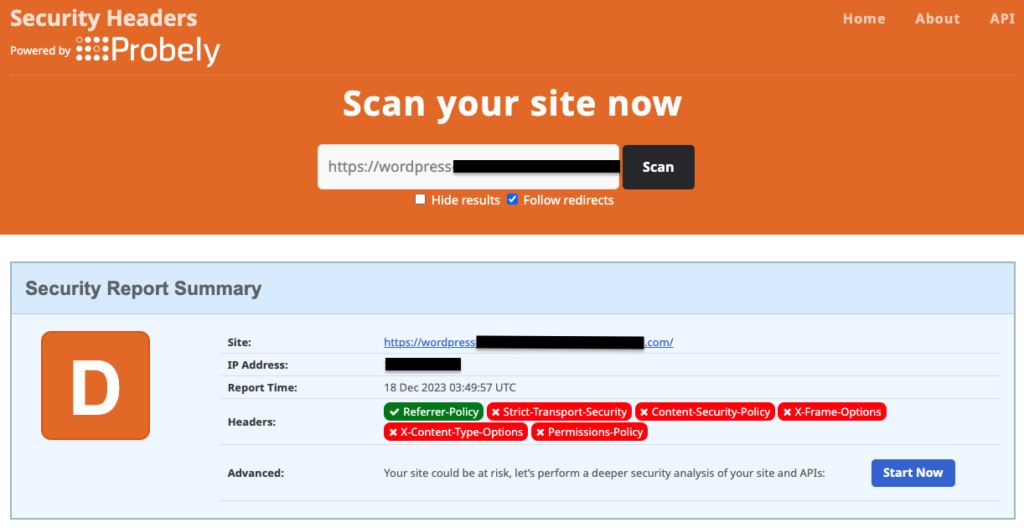
4. Verify header configuration: Return to Security Headers, give your site URL another whirl in the scan, and see your handiwork. If your changes are not visible yet, clear your browser’s cache and try searching later.
2. Configure the Referrer-Policy header in WordPress by editing the .htaccess file
Another way to configure the Referrer-Policy header on your WordPress site is to edit the .htaccess file. This is a crucial system file, so backing it up first is smart—think of it as insurance for digital hiccups. BlogVault is your go-to backup plugin for this, offering a safety net for your full site, with all files and databases stored offsite. Should glitches strike, BlogVault will swoop in to restore your site in no time.
Once your site is backed up, move ahead with one of these methods to edit the .htaccess file:
A. Edit the .htaccess file via FTP
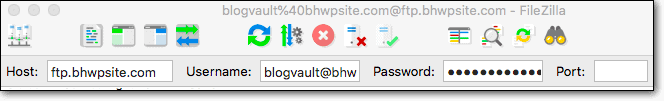
To edit your site’s .htaccess file using FTP, you will need an FTP client. We prefer using Filezilla and the steps to use it are as follows:
- Login to your WordPress site using FTP: Open your FTP client, input your credentials: IP, username, password, port (if needed), and click ‘Quickconnect’ to connect to your server.
- Find the .htaccess file: The .htaccess file is found in your root folder, which in our case was the public_html folder. Remember, it is a hidden file, so you might need to check your FTP client’s settings to view it.
- Edit the .htaccess file: Right-click .htaccess and click on ‘View/Edit’. Check if you already have an <IfModule mod_headers.c> section, where you can paste the Header set directive. If not, just paste the following code snippet before the file ends:
<IfModule mod_headers.c>
Header set Referrer-Policy "no-referrer-when-downgrade"
</IfModule>- Save the changes: Save the file, close the editor, and tell Filezilla ‘Yes’ to update the file on your server.
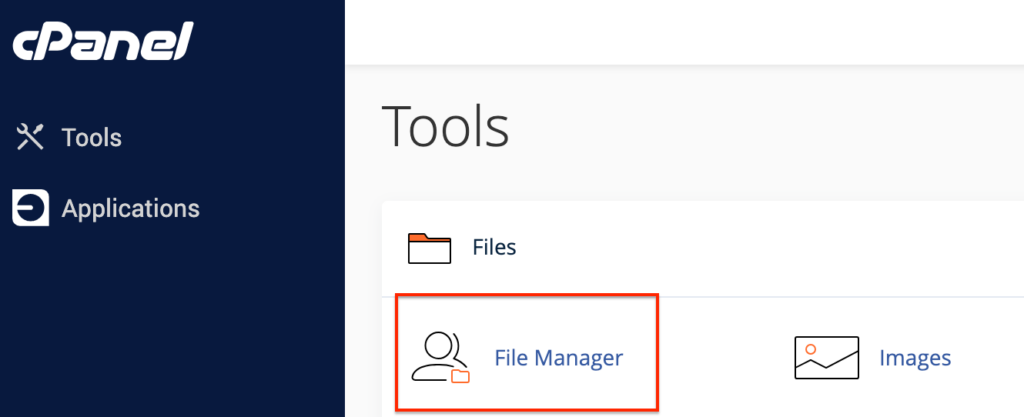
B. Edit the .htaccess file via the cPanel File Manager
If your web host provides a cPanel for site administration, you can use the built-in File Manager to edit the .htaccess file.
- Access the File Manager on cPanel: Log in to your site’s cPanel and find the File Manager in the Tools section.
- Find and edit the .htaccess file: Once in your root folder (which is public_html in our case), right-click on .htaccess, and hit Edit. When the editor opens, add the same code snippet.
<IfModule mod_headers.c>
Header set Referrer-Policy "no-referrer-when-downgrade"
</IfModule>- Save your edits: Click Save Changes on the editing window’s top-right corner to apply your edits.
C. Edit the .htaccess file via SSH
If you are a tech-savvy site admin, you might want to use SSH to make the edits to the .htaccess file. For this, you will need Command Prompt, if you are a Windows user, or Terminal, if you are a Mac user.
- Connect to your WordPress site via SSH: Open a Command Prompt or Terminal window and enter the following command:
ssh username@ipaddressSwap ‘username’ and ‘ipaddress’ with your login details, followed by your password when prompted.
- Find the .htaccess file: Get to the root directory (public_html in our case), if you are not already there, by entering the following command:
cd public_htmlThen, list all files, hidden and otherwise by entering:
ls -aYou should find the .htaccess file here.
- Edit the .htaccess file: Open the .htaccess file using the built-in Vmacs editor by entering:
vi .htaccessPress ‘i’ to get to insert mode and paste the same code.
<IfModule mod_headers.c>
Header set Referrer-Policy "no-referrer-when-downgrade"
</IfModule>- Save the .htaccess file and exit: Hit Esc, type :wq, and press Enter to save the edits and exit the editor.
Tip: If you use an nginx server to host your WordPress site, you will need to edit the nginx.conf file, and add the following lines of code before the file ends:
add_header Referrer-Policy "no-referrer-when-downgrade" always;Potential issues and how to resolve them
Tweaking the Referrer-Policy header can sometimes lead to a few head-scratchers. Let’s look at some potential issues you might encounter while configuring it on your WordPress site and, more importantly, how to troubleshoot them:
Changing the Referrer-Policy header affects features like third-party widgets or analytics tracking
Fix: Balance is key. Start with a less restrictive policy, such as ‘origin-when-cross-origin’, and test your site’s features. Gradually move toward more privacy-oriented settings until you find the sweet spot where both functionality and privacy harmonize like a well-rehearsed choir.
.htaccess file edits not taking effect
Fix: First, make sure you’ve edited and saved the file correctly and uploaded it back to the server if using FTP. If that’s already done, the stubborn refusal could be due to server caching. Clear the cache on your hosting environment, and while you’re at it, clear your browser cache too, just to cover all bases.
I’m seeing a 500 Internal Server Error
Fix: Stay calm and fetch that backup. Restore the .htaccess file to its previous state using the backup copy from BlogVault to resurrect your site. Once breathing again, review your .htaccess edits to ensure there are no typos or syntax issues. Copy and paste the code snippets carefully, like handling fine china.
Plugin conflicts over header handling
Fix: Disable related plugins one by one to spot the mischief-maker. Once identified, decide which plugin gets to configure HTTP headers, or reach out to the plugin authors—they’re often more helpful than a squadron of knights when it comes to defending your site’s harmony.
Importance of HTTP headers in WordPress
HTTP headers in WordPress are the silent guardians and efficiency experts of your website. Far from the cryptic code they appear to be, they’re the power-ups that ensure your visitors enjoy a secure and smooth browsing experience.
- Encouraging secure conversations: Think of security-focused headers as the secret service of internet communications, always ensuring that browsers talk to your site in the secure dialect of HTTPS, encrypting data to maintain privacy like whispers in a noisy room.
- Maintaining privacy: Craft these headers to be the ultimate gatekeepers of information, sharing only what’s necessary with web requests. It’s like having a top-notch privacy filter ensuring your site doesn’t overshare in the digital sphere.
- Speeding up load times: Like optimizing a pit stop in a race, well-configured caching headers navigate browser caching so efficiently that your site loads faster than a racecar off the blocks.
- Blocking MIME confusion: Position the right headers at the door, and they’ll keep browsers from misunderstanding your content’s MIME types, refusing to engage with disguised or mislabeled data as if saying, “Nope, not on the list!”
- Boosting security: Employing HTTP headers is akin to assembling an around-the-clock security squad for your WordPress site, repelling cross-site scripting and harmful code injections.
- Protecting from prying frames: Set headers with finesse to stop your website from being hijacked into rogue frames, a move as strategic as installing an invisible shield against the dark arts of clickjacking.
Are HTTP headers enough for WordPress security?
While mastering the art of HTTP headers is a vital move for your WordPress site’s security regimen, it’s really just the first step. Let’s talk about what more you can do to turn your website into a digital fortress:
- Enlist MalCare for full-scale security: Kick off with the big guns by adding MalCare to your WordPress site. Its firewall, automated malware scanner, and one-click malware cleaning provide real-time, on-the-go defense.
- Stay updated: Think of updates as your website’s health regime—keeping it in top shape. Regularly updating WordPress itself, themes, and plugins, is like a digital vaccine that keeps new vulnerabilities at bay. But, do it safely.
- Double down on login security: Relying on ‘password123’ is like leaving your keys in the door. Opt for passwords that give hackers a run for their money and add two-factor authentication as your digital shield against invasion attempts.
- Backup with BlogVault: Make BlogVault your safety net. With regular backups, if things go south, you can click a few buttons to restore your site.
- Restrict user access: The fewer people who have the all-access key to your WordPress backend, the harder it is for hackers to slip through.
- Tighten file permissions: Tightening file permissions in WordPress is a crucial security measure. It works much like locking your drawers and safes in the physical world. By setting strict permissions, you’re ensuring that unauthorized users cannot access or modify your site’s data.
- Monitor activity logs: Keep an eye on what’s happening backstage with activity logs. It’s like having CCTV footage to spot any unusual activity before it becomes a headline act. MalCare offers a top-notch activity log that is automatically installed when the plugin is activated.
Final thoughts
Configuring the Referrer-Policy HTTP header is a vital best practice for your WordPress site. It manages the transmission of referral data to maintain user privacy and preserve your website’s credibility. While this represents a significant step in safeguarding your digital presence, it does not safeguard your site from other security threats like malware, attacks, and vulnerabilities.
To improve your site’s security posture beyond the Referrer-Policy header, integrate a full-fledged security plugin like MalCare. MalCare’s robust security measures, which include a powerful firewall, real-time malware scanning, and automatic threat removal, provide a thorough defense mechanism for your WordPress site. It is a proactive guard against the multitude of cyber threats that can compromise the safety of your online ecosystem. By choosing MalCare, you ensure that the security of your site is managed proficiently, allowing you to focus on your content and audience with peace of mind.
FAQs
What is a referrer on WordPress?
A referrer is a site that sends its users to another site when they click on links on the first site. Referrers could be search engines like Google, other websites, etc.
Why is configuring the Referrer-Policy header important?
Configuring the Referrer-Policy header is important because it helps safeguard user data, minimize the risk of privacy breaches, and prevent potential security vulnerabilities that can be exploited through referrer headers.
Can setting the Referrer-Policy header affect my website’s SEO?
Setting the Referrer-Policy header to certain values could potentially impact analytics and the tracking of referral traffic, but it generally does not directly affect SEO. It’s important to choose a value that strikes a balance between privacy and the ability to track legitimate traffic sources.
Is it necessary to use a security plugin alongside configuring the Referrer-Policy header?
Yes. While configuring the Referrer-Policy header adds an important layer of privacy and security, you must also take into account all the different aspects of security. And a security plugin is one of these aspects. Hence, it’s highly recommended to use a comprehensive security plugin like MalCare. This provides a more holistic approach to protecting your WordPress site against a wide array of security threats.
How often should I update my Referrer-Policy header settings?
You should review and update your Referrer-Policy header settings whenever there are changes to your site that might affect how referrer data should be handled. Generally, you’ll want to revisit these settings as part of your regular site security audits.
Are there any risks associated with configuring the Referrer-Policy header?
The main risk associated with setting the Referrer-Policy header improperly is that it may inadvertently block legitimate and useful referral data. Ensure you understand the implications of each policy value and test thoroughly after applying changes.
Can I set the Referrer-Policy header without technical expertise?
Yes, WordPress plugins designed to manage HTTP headers can help non-technical users set the Referrer-Policy header easily. However, for those preferring to edit server files, technical knowledge is required, and caution is advised.
Category:
Share it:
You may also like
How to Fix the Google Blacklist Warning from Your Website
Google blacklist is a colloquial term used to describe big red warnings visible when visiting websites. There are a few flavours, depending on various factors, but they all mean that…

MalCare Stands Strong Against WP Activity Log Premium SQL Injection Vulnerability
A significant SQL injection vulnerability was identified in the WP Activity Log Premium plugin, a popular tool for tracking user activity on WordPress sites. An SQLi vulnerability poses a serious…
Fix Pharma Hack on WordPress and SEO
Pharma hack is a prolific malware that redirects visitors from your site to an online pharmacy that sells Viagra, Cialis, Levitra, Xanax, Tadalafil, and other drugs. It also shows up…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








