How Meltdown And Spectre Attacks Affect WordPress
by
7-layers of Security for Your WordPress Site
Your website needs the most comprehensive security to protect it from the constant attacks it faces everyday.

New hardware bugs have been reported which affects processors. The ones that are designed by Intel, AMD, and ARM. These security flaws were reported by Google’s Project Zero. And are already being termed as one of the worst CPU attacks bugs ever found.
Spectre Meltdown Explained:
Meltdown and Spectre vulnerabilities allow malicious programs to read. As well as accessing data from other programs. All systems are affected who uses any modern computing device. You might be a WordPress site owner or a casual browser of websites. This issue can harm you. For example, you have a browser tab accessing a malicious site. This tab is able to access data from the password manager installed on the browser. Or even cookies from other tabs. Similarly, if you have a WordPress site hosted with web hosts. And it has multiple sites sharing the same hardware. Your site is susceptible to data breach theft. This means irrespective of whether you are on shared or managed to host. You are in a bad situation.

Why are Spectre and Meltdown dangerous?
This particular issue affects everyone who uses any modern computing device. You might be a WordPress site owner or a casual browser of websites. This issue can harm you. For example, you have a browser tab accessing a malicious site. This tab can access data from the password manager installed on the browser. Or even from cookies from other tabs. In the same way, if you have a WordPress site hosted with web hosts. And the host has multiple sites sharing the same hardware. Your site is susceptible to data theft. This means irrespective of whether you are on shared or managed hosting. You are in a bad situation.
Am I affected as a Website owner?
As of now, you are already affected by Meltdown security bug. The data theft can include passwords, SSL keys, and other sensitive information.
What should I do as a WordPress site owner?
There are four popular ways of hosting a WordPress site:
Shared Hosting – GoDaddy, Bluehost, SiteGround et al.
On shared hosting, there are many sites running alongside many others. And on very close proximity on a server. These servers have a certain level of protection. Ensuring the safety of one site from another. This wall between sites is sufficient under normal operation. But it can be breached. All website instances are running on the same machine. This vulnerability can allow a malicious site to make attempts to access data on other sites.
The web hosts, in this case, are responsible for deploying the Spectre Meltdown patches. You should follow up with your web host. And ensure that they have a plan for this.
Managed WordPress Hosting – WP Engine, Pantheon, etc.
Managed WordPress hosting is traditionally considered a better hosting. And even a more secure option than shared hosting. Most of the popular Managed WordPress Hosting providers host the sites on the big cloud provider. Those providers include AWS, Digital Ocean, Google cloud among others. Managed hosting reduces the risk of one site being able to afflict another site. That is other sites on the same server. However, this case is different as Spectre and Meltdown are hardware bugs. You are hosted on a dedicated container? Know that multiple containers might be running on the same machine. This puts you on the same risk as a site hosted on shared hosting.
Many cloud platforms have already fixed their underlying platforms. Some others have also laid out a plan for the same too. The managed web hosts will also need to apply software patches for Meltdown or spectre meltdown patch. They’ll have to do this to their own systems too.
Cloud Hosting – Digital Ocean, AWS etc.
A few of us run our sites by renting virtual servers from cloud hosting platforms. These cloud platforms allow multiple customers to share a physical server. The customer can install their own operating system. And then manage the entire stack on top of this. Giving them complete flexibility. The underlying server is common. Hence, it is possible to exploit meltdown vulnerability or spectre vulnerability.
The major cloud services are quickly patching their platforms. However, you are responsible for maintaining your own virtual server. You should update your OS as soon as possible.
Dedicated servers
Hosting of privately owned and maintained server is not a popular option. This is because of the complexity and cost. However, if you happen to do so, you are at minimal risk from this bug. Though we would still advice to keep your OS updated.
Can I know if my site is under attack?
Unfortunately, it’s unlikely to know if you are getting attacked. These are hardware bugs that can lead to data theft. That too without leaving any traces in traditional log files. The attack is independent of the operating system. And it does not rely on any software security vulnerabilities. These bugs work on personal computer chips, mobile devices, and the cloud system. It might be possible to steal data from you and your visitors. But that depends on the hosting provider’s infrastructure.
How can I fix it?
Sadly there is not much you can do at the moment. This bug affects almost everyone. Operating System vendors have already started rolling out fixes. But these are stopgap patches and costs performance. Meltdown attacks or Meltdown Spectre patch is supposed to have 5 to 30% CPU performance impacts. Whereas Spectre (and Spectre variants) will not be fixed any time soon. We hope chip manufacturers like Intel and AMD will take steps. That will help deal with these types of future attacks. And would prevent any type of chip flaw.
More recently there has been a fair amount of discussion around Intel processor design flaw and what is dubbed as the Intel Spectre meltdown or meltdown Intel. With secure Intel chips and AMD processor, you’ll be able to protect your PC.
Whom should I contact for help?
Major hosting companies have already started deploying Spectre and Meltdown patches or Meltdown and Spectre patches. As a site owner checks with your hosting provider about the status of their system. Ask them to deploy fixes immediately if they haven’t already. Check with them what these fixes mean to you as an end user. Will it affect the site performance? Will these effects be visible to your end users?
But what are these Meltdown and Spectre attacks anyway or Spectre vulnerability explained?
Google Project Zero revealed the bug as:
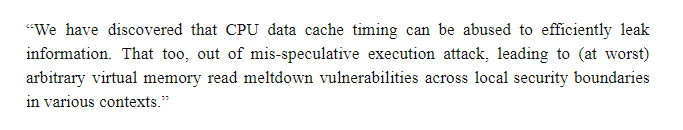
The above statement summarises the exploits made by Meltdown or Spectre. As a matter of fact, they are an example of the side channel vulnerabilities or side channel attacks.
Statements have been released in January by major companies like Amazon, Google, and AMD. They assure their users that their latest software versions are safe. Many other giants like Apple have not commented yet. Use antivirus software on your computer. Also get a Spectre Meltdown checker on your computer. You can also learn more about Project Zero news and updates on Google’s team Blogspot.
Below is a list of the newly discovered attacks:
Meltdown-PK (Protection Key Bypass)
Meltdown-BR (Bounds Check Bypass)
Spectre-PHT-CA-OP
Spectre-PHT-SA-IP
Spectre-PHT-SA-OP
Spectre-BTB-SA-IP
Spectre-BTB-SA-OP
Hope that this blog written by our research teams clarifies most of your doubts. Watch out this space for more security updates as well as a complete guide on WordPress security.
Category:
Share it:
You may also like

MalCare Ensures Unmatched Protection Against User Registration Privilege Escalation Vulnerability
Imagine discovering that your WordPress site, which should be secure and under strict control, has suddenly become accessible to unauthorized users who have the same administrative powers as you. This…

MalCare Ensures Proactive Protection Against WP-Members XSS Vulnerability
MalCare continues to protect its customer sites from all kinds of attacks, even the ones exploiting zero-day vulnerabilities. The recent stored cross-site scripting (XSS) vulnerability found in the WP-Members Membership…
![Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]](https://www.malcare.com/wp-content/uploads/2022/12/malcare-default-image.jpeg)
Top 9 ManageWP Alternatives To Manage Multiple Sites Easily [Reviewed]
ManageWP is a popular name in the WordPress maintenance plugins market. People love how much you get for a free plan, how easy it is to set up, and how…
How can we help you?
If you’re worried that your website has been hacked, MalCare can help you quickly fix the issue and secure your site to prevent future hacks.

My site is hacked – Help me clean it
Clean your site with MalCare’s AntiVirus solution within minutes. It will remove all malware from your complete site. Guaranteed.

Secure my WordPress Site from hackers
MalCare’s 7-Layer Security Offers Complete Protection for Your Website. 300,000+ Websites Trust MalCare for Total Defence from Attacks.








